Loading questions...
Updated
Want a break from the ads?
Become a Supporter and enjoy a completely ad-free experience, plus unlock Learn Mode, Exam Mode, AstroTutor AI, and more.
Support Examcademy
Your support keeps this platform running. Become a Supporter to remove all ads and unlock exclusive study tools.
Create a free account to unlock all questions for this exam.
Log In / Sign UpWhich file can be used to validate repcli authentication was enabled for Carbon Black Cloud?
An administrator found an unwanted/untrusted application running in their environment.
What is the most efficient way of preventing the unwanted application from running and stopping any existing instances in Carbon Black Cloud?
In the NSX Manager UI, which tab is selected to manage firewall rules?
Which is the name of the default policy that is applied to all applications in Workspace ONE Access?
In a Carbon Black Cloud deployment, which two are recommended troubleshooting steps for Live Response not working? (Choose two.)
When creating a sensor group in VMware Carbon Black Cloud, which three are valid criteria? (Choose three.)
An organization is expanding NSX to deploy the NSX Distributed Firewall on an AWS VPC and Azure VNET.
Which statement is true concerning the expansion?
What is the correct sequence of options when creating a new compliance policy in Workspace ONE UEM?
Which is the built-in two factor authentication method in Workspace ONE Access?
What command does an administrator use on an ESXi Transport Node to check connectivity with the management plane?
Refer to the exhibit.
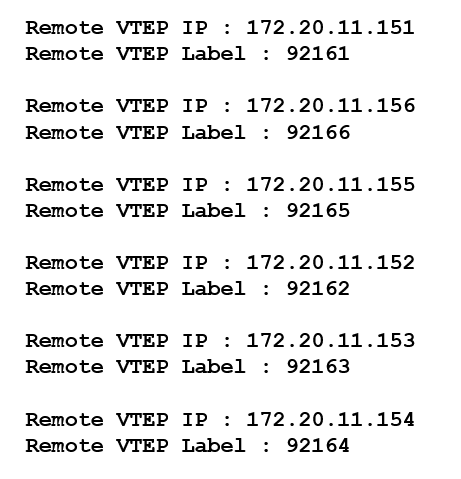
What command was run on the NSX Edge node to pull this information?
Which Carbon Black Cloud feature allows an administrator to audit at scale and identify gaps in least privilege configuration controls?
In what order are NSX-T Distributed Firewall configurable rules categories processed?
Which statement is true about TraceFlow when used in an NSX-T Data Center deployment?