Loading provider exams...
Sign Up & unlock 100% of Exam Questions
No Strings Attached!
Updated
Northern Trail Outfitters (NTO) wants its customers to use phone numbers to log in to their new digital portal, which was designed and built using Salesforce Experience Cloud. In order to access the portal, the user will need to do the following:
This exam has 58 community-verified practice questions. Create a free account to access all questions, comments, and explanations.
Universal Containers (UC) is using its production org as the identity provider for a new Experience Cloud site and the identity architect is deciding which login experience to use for the site.
Which two page types are valid login page types for the site? (Choose two.)
Northern Trail Outfitters (NTO) is planning to build a new customer service portal and wants to use passwordless login, allowing customers to login with a one-time passcode sent to them via email or SMS.
How should the quantity of required Identity Verification Credits be estimated?
Northern Trail Outfitters would like to use a portal built on Salesforce Experience Cloud for customer self-service. Guests of the portal should be able to self-register, but be unable to automatically be assigned to a contact record until verified. External Identity licenses have been purchased for the project.
After registered guests complete an onboarding process, a flow will create the appropriate account and contact records for the user.
Which three steps should an identity architect follow to implement the outlined requirements? (Choose three.)
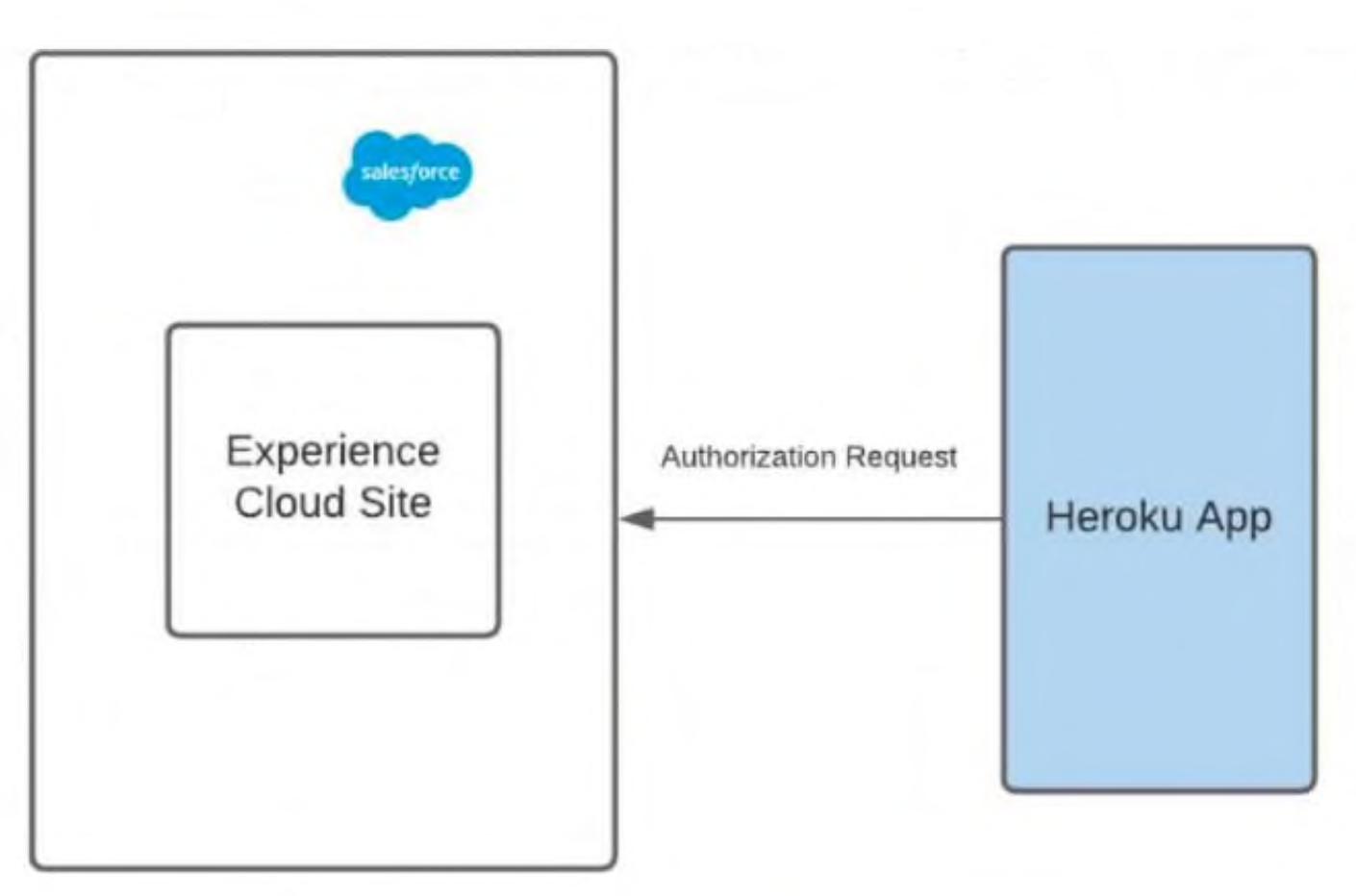
A user should select either of the two brands in Heroku before logging into the community. The app then performs Authorization using OAuth2.0 with the Salesforce Experience Cloud site.
NTO wants to make sure it renders login page images dynamically based on the user’s brand preference selected in Heroku before Authorization.
What should an identity architect do to fulfill the above requirements?
An Identity and Access Management (IAM) architect is tasked with unifying multiple B2C Commerce sites and an Experience Cloud community with a single identity. The solution needs to support more than 1,000 logins per minute.
What should the IAM Architect do to fulfill this requirement?
Northern Trail Outfitters (NTO) has an existing business-to-consumer (B2C) website that that does NOT support single sign-on standards, such as Security Assertion Markup Language (SAML) or OAuth. NTO wants to use Salesforce Identity to register and authenticate new customers on the website.
Which three Salesforce features should an Identity architect use in order to provide social sign-in capabilities for the website? (Choose three.)
The CMO of an advertising company has invited an Identity and Access Management (IAM) specialist to discuss Salesforce out-of-box capabilities for configuring the company’s login and registration experience on Salesforce Experience Cloud.
The CMO is looking to brand the login page with the company’s logo, background color, login button color, and dynamic right-frame from an external URL.
Which two solutions should the IAM specialist recommend? (Choose two.)
Universal Containers is creating a mobile application that will be secured by Salesforce Identity using the OAuth 2.0 user-agent flow. Application users will authenticate using username and password. They should not be forced to approve API access in the mobile app or reauthenticate for 3 months.
Which two connected app options need to be configured to fulfill this use case? (Choose two.)
An administrator created a connected app for a custom web application in Salesforce which needs to be visible as a tile in App Launcher. The tile for the custom web application is missing in the app launcher for all users in Salesforce. The administrator requested assistance from an identity architect to resolve the issue.
Which two reasons are the source of the issue? (Choose two.)
A leading fitness tracker company is getting ready to launch a customer community. The company wants its customers to login to the community and connect their fitness device to their profile. Customers should be able to obtain exercise details and fitness recommendation in the community.
Which should be used to satisfy this requirement?
Universal Containers is implementing a new Experience Cloud site and the identity architect wants to use dynamic branding features as part of the login process.
Which two options should the identity architect recommend to support dynamic branding for the site? (Choose two.)
Want a break from the ads?
Become a Supporter and enjoy a completely ad-free experience, plus unlock Learn Mode, Exam Mode, AstroTutor AI, and more.
A university is planning to set up an identity solution for its alumni. A third-party identity provider will be used for single sign-on and Salesforce will be the system of records. Users are getting error messages when logging in.
Which Salesforce feature should be used to debug the issue?
A Salesforce Administrator is tasked with setting up Just-in-Time (JIT) provisioning for SAML to enable Single Sign-On (SSO) for your organization. They have already configured the SAML settings for SSO in Salesforce.
What should be their next steps to enable JIT provisioning?
Universal Containers (UC) wants to provide single sign-on (SSO) for a business-to-consumer (B2C) application using Salesforce Identity.
Which Salesforce license should UC utilize to implement this use case?
An identity architect is setting up an integration between Salesforce and a third-party system. The third-party system needs to be able to authenticate to Salesforce and then make API calls against the REST API.
One of the requirements is that the solution needs to ensure the third party service providers connected app in Salesforce minimizes the need for end user interaction and maximizes security.
Which OAuth flow should be used to fulfill the requirement?
Universal Containers is creating a web application that will be secured by Salesforce Identity using the OAuth 2.0 Web Server Flow (this flow uses the OAuth 2.0 authorization code grant type).
Which three OAuth concepts apply to this flow? (Choose three.)
Universal Containers (UC) has built a custom time tracking app for its employees on a third party system. UC wants to leverage Salesforce Identity to control access to the custom app.
At a minimum, which Salesforce license is required to support this requirement?
An identity architect is implementing a mobile-first Consumer Identity Access Management (CIAM) for external users.
User authentication is the only requirement. The users email or mobile phone number should be supported as a username.
Which two licenses are needed to meet this requirement? (Choose two.)
A farming enterprise offers smart farming technology to its farmer customers, which includes a variety of sensors for livestock tracking, pest monitoring, climate monitoring etc. They plan to store all the data in Salesforce. They would also like to ensure timely maintenance of the installed sensors. They have engaged a Salesforce Architect to propose an appropriate way to send an alert when something goes wrong.
Which OAuth flow should the architect recommend?
A global company has built an external application that uses data from its Salesforce org via an OAuth 2.0 authorization flow. Upon logout, the existing Salesforce OAuth token must be invalidated.
Which action will accomplish this?
A global fitness equipment manufacturer uses Salesforce to manage its sales cycle. The manufacturer has a custom order fulfillment app that needs to request order data from Salesforce. The order fulfillment app needs to integrate with the Salesforce API using OAuth 2.0 protocol.
What should an identity architect use to fulfill this requirement?
A company’s external application is protected by Salesforce through OAuth. The identity architect for the project needs to limit the level of access to the data of the protected resource in a flexible way.
What should be done to improve security?
Universal Container’s (UC) is using Salesforce Experience Cloud site for its container wholesale business. The identity architect wants to use an authentication provider for the new site.
Which two options should be utilized in creating an authentication provider? (Choose two.)