Loading questions...
Updated
Want a break from the ads?
Become a Supporter and enjoy a completely ad-free experience, plus unlock Learn Mode, Exam Mode, AstroTutor AI, and more.
Create a free account to unlock all questions for this exam.
Log In / Sign Up. (Choose four.)
In an enterprise deployment, where are the binary and library files that are required for Oracle Access Management located? (Choose the best answer.)
How would you add support for additional Internet Identity Providers for Oracle Access Management Mobile and Social, other than the preconfigured ones such as
Facebook and LinkedIn? (Choose the best answer.)
Identify two protocols that the Oracle Access Management Social module supports for Authentication and Authorization using Internet Identity services. (Choose two.)
replace and provide a converged platform for? (Choose two.)
E. Oracle Enterprise Single Sing-On
Your customer wants to use the information available in the Identity Context in their application to determine a users journey through various screens and functions.
One of the attributes they want to use is the Oracle Adaptive Access Manager (OAAM) risk score. They have deployed OAAM and think they have integrated it correctly into the Oracle Access Management platform. However, when their application interrogates Identity Context, none of the OAAM attributes are present.
Which three configuration settings should you check as part of troubleshooting the problem? (Choose three.)
Identify the mandatory attribute that is used when creating an application profile for a mobile application in Single Sign-On with Oracle Access Management Mobile and Social services.
By default, which four Oracle Access Management platform components write attributes into the Identity Context? (Choose four.)
View the Exhibits.
Exhibit 1 -
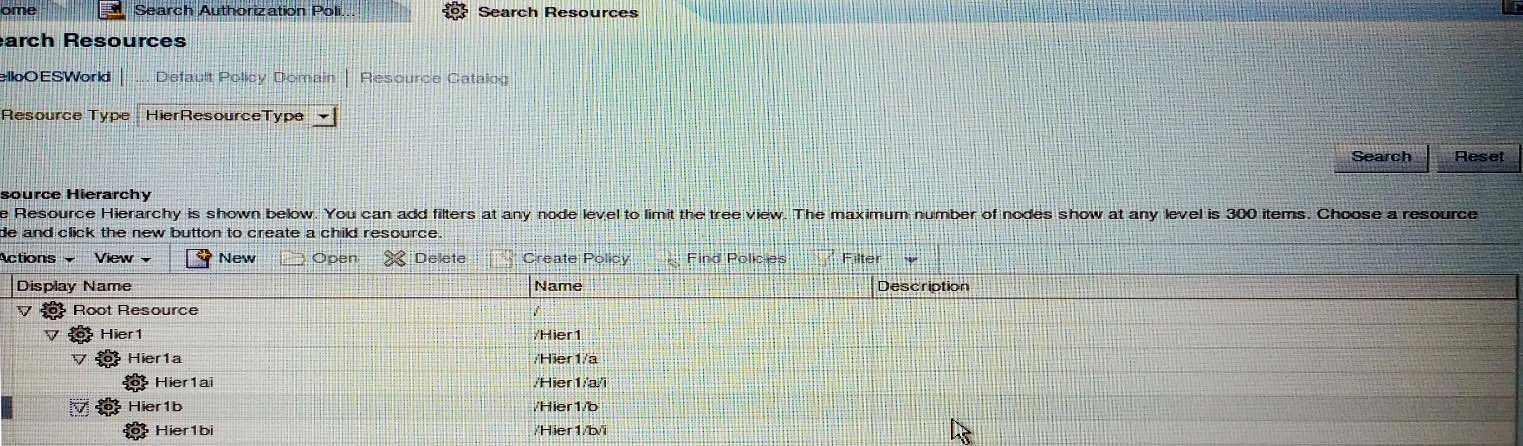
Exhibit 2 -
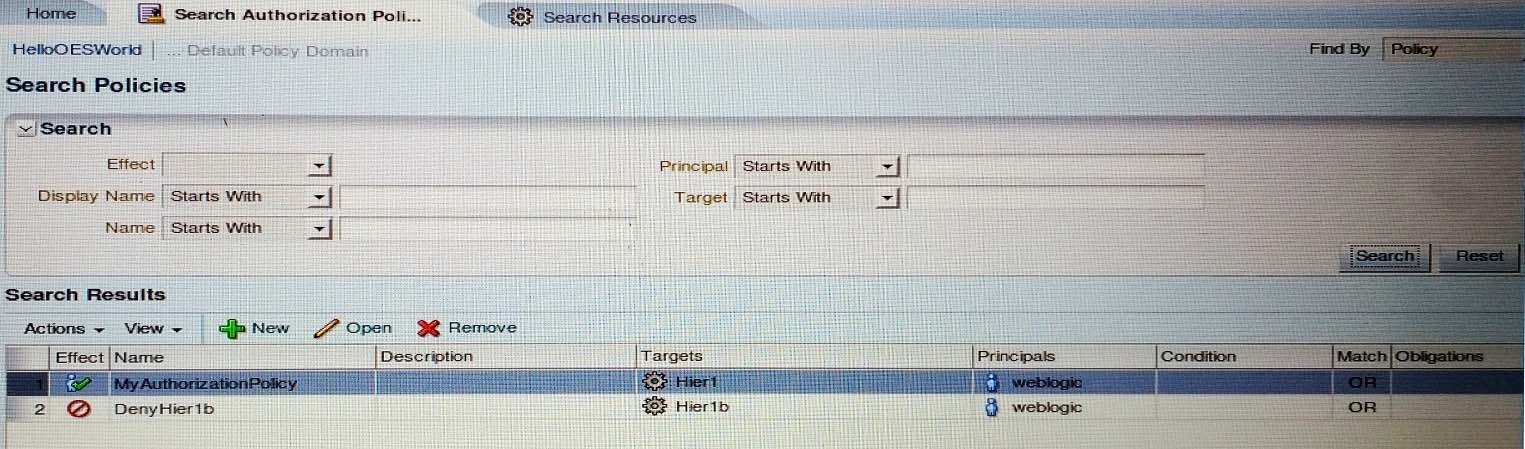
You have created a set of hierarchical resources in Oracle Entitlements Server and an associated set of authorization policies as shown in the Exhibits.
You execute a newQueryPepRequest in order to evaluate exactly which resources the weblogic user has access to.
Which three hierarchical resources can user access? (Choose three.)
when it is configured as an Identity Provider (IdP)? (Choose the best answer.)
You have defined an application and its associated policies in Oracle Entitlements Server (OES) to protect your customer's banking application. This application is written in Java and deployed on WebLogic, using the WebLogic security module for integration. Using the policy simulator, your policy logic appears to be correct.
However, while testing, it appears that your authorization policies are not being applied and all authorization decisions are being returned as false from the security module.
Which two configuration settings in your OES admin console may be the cause if this problem? (Choose two.)
Identify two registration artifacts that are created when an 11g WebGate is registered using the Oracle Access Management console.