Loading provider exams...
Sign Up & unlock 100% of Exam Questions
No Strings Attached!
Updated
You have a Microsoft 365 E5 subscription that uses Microsoft Defender 365.
You need to ensure that you can investigate threats by using data in the unified audit log of Microsoft Defender for Cloud Apps.
What should you configure first?
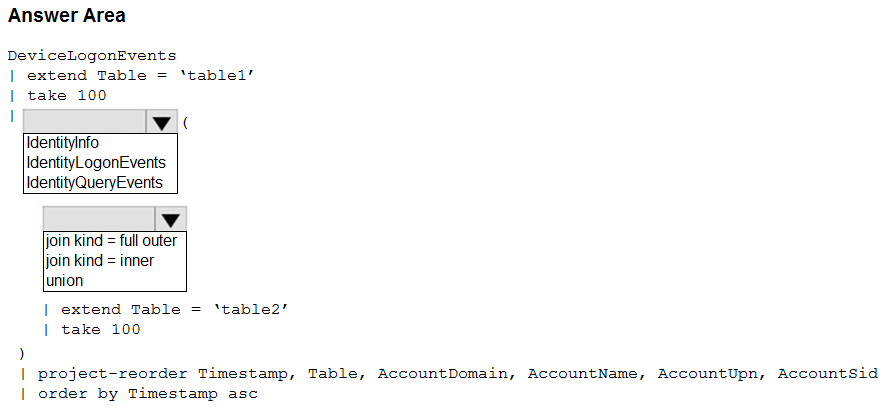
You have a Microsoft 365 E5 subscription that uses Microsoft Defender 365.
Your network contains an on-premises Active Directory Domain Services (AD DS) domain that syncs with Azure AD.
You need to identify the 100 most recent sign-in attempts recorded on devices and AD DS domain controllers.
How should you complete the KQL query? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
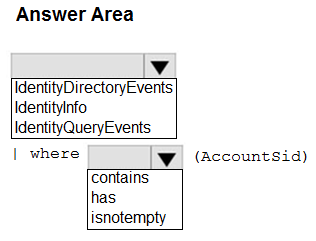
You have a Microsoft 365 E5 subscription that uses Microsoft Defender 365.
Your network contains an on-premises Active Directory Domain Services (AD DS) domain that syncs with Azure AD.
You need to identify LDAP requests by AD DS users to enumerate AD DS objects.
How should you complete the KQL query? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You have an Azure subscription that uses Microsoft Defender for Servers Plan 1 and contains a server named Server1.
You enable agentless scanning.
You need to prevent Server1 from being scanned. The solution must minimize administrative effort.
What should you do?
You need to configure Microsoft Defender for Cloud Apps to generate alerts and trigger remediation actions in response to external sharing of confidential files.
Which two actions should you perform in the Microsoft 365 Defender portal? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
Want a break from the ads?
Become a Supporter and enjoy a completely ad-free experience, plus unlock Learn Mode, Exam Mode, AstroTutor AI, and more.
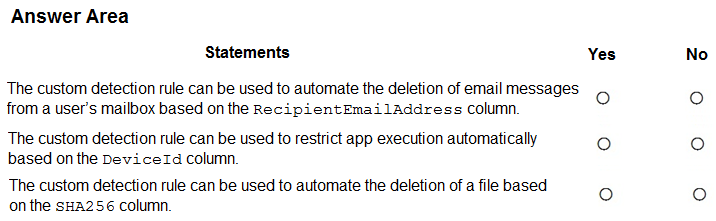
51 HOTSPOT
You have a custom detection rule that includes the following KQL query.
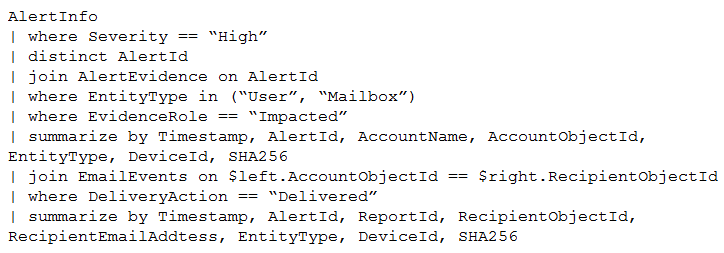
For each of the following statements, select Yes if True. Otherwise, select No.
NOTE: Each correct selection is worth one point.
You have a Microsoft 365 E5 subscription that uses Microsoft Defender for Endpoint.
You need to identify any devices that triggered a malware alert and collect evidence related to the alert. The solution must ensure that you can use the results to initiate device isolation for the affected devices.
What should you use in the Microsoft 365 Defender portal?
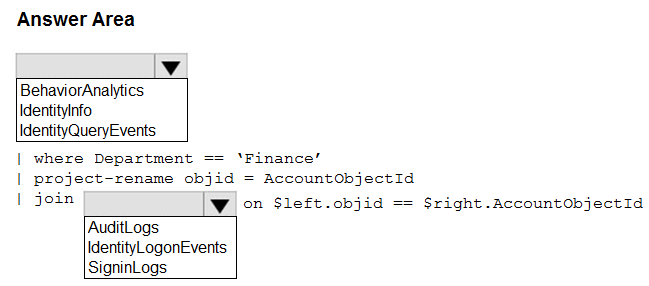
Your network contains an on-premises Active Directory Domain Services (AD DS) domain that syncs with Azure AD.
You have a Microsoft 365 E5 subscription that uses Microsoft Defender 365.
You need to identify all the interactive authentication attempts by the users in the finance department of your company.
How should you complete the KQL query? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You have an Azure subscription that uses Microsoft Defender for Cloud.
You have a GitHub account named Account1 that contains 10 repositories.
You need to ensure that Defender for Cloud can access the repositories in Account1.
What should you do first in the Microsoft Defender for Cloud portal?
You have the resources shown in the following table.
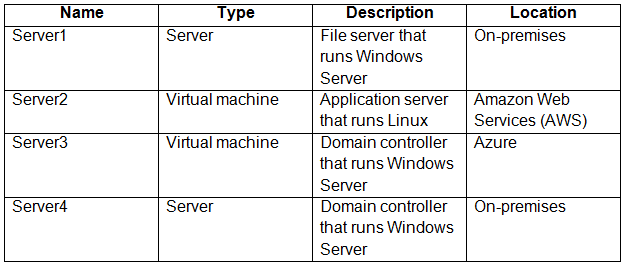
You have an Azure subscription that uses Microsoft Defender for Cloud.
You need to enable Microsoft Defender for Servers on each resource.
Which resources will require the installation of the Azure Arc agent?
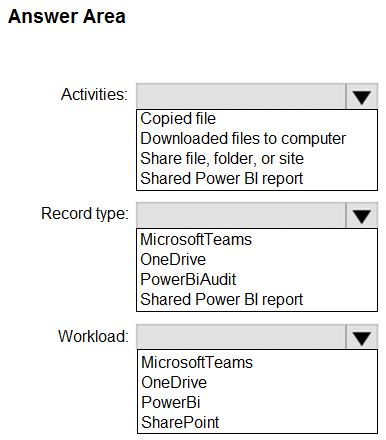
HOTSPOT -
You have a Microsoft 365 E5 subscription that uses Microsoft Purview and contains a user named User1.
User1 shares a Microsoft Power BI report file from the Microsoft OneDrive folder of your company to an external user by using Microsoft Teams.
You need to identify which Power BI report file was shared.
How should you configure the search? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
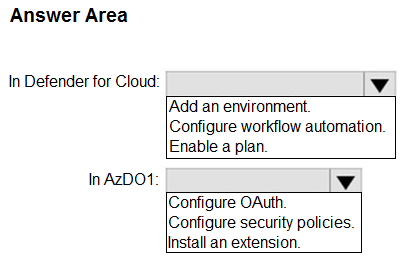
You have an Azure subscription named Sub1 that uses Microsoft Defender for Cloud.
You have an Azure DevOps organization named AzDO1.
You need to integrate Sub1 and AzDO1. The solution must meet the following requirements:
• Detect secrets exposed in pipelines by using Defender for Cloud.
• Minimize administrative effort.
What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You have a Microsoft Sentinel playbook that is triggered by using the Azure Activity connector.
You need to create a new near-real-time (NRT) analytics rule that will use the playbook.
What should you configure for the rule?
HOTSPOT -
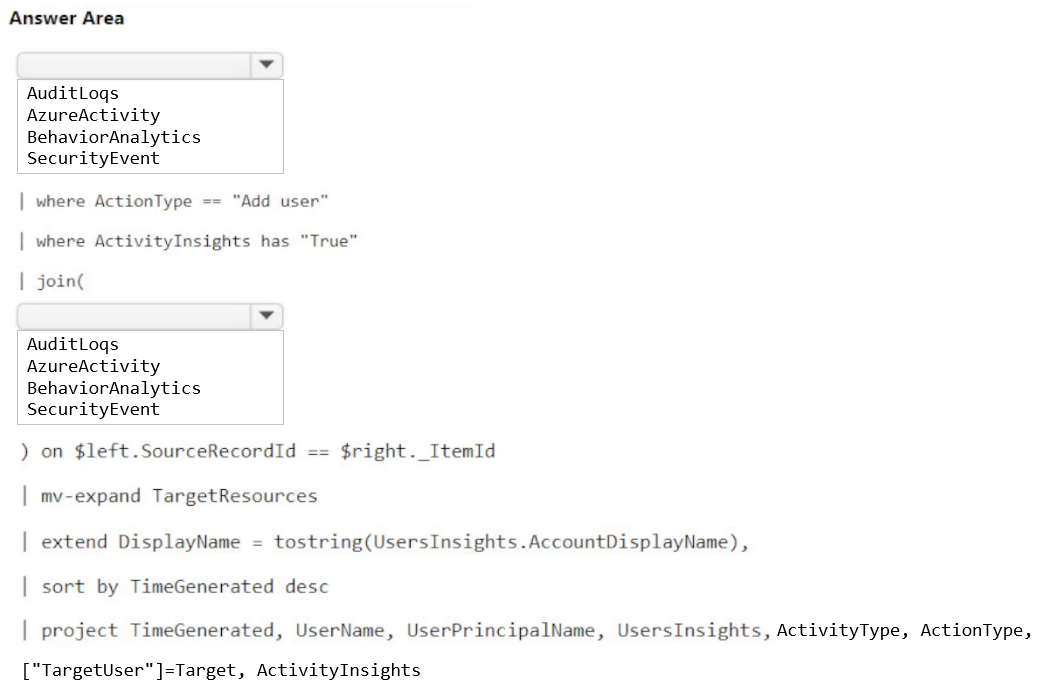
You have a Microsoft Sentinel workspace named sws1.
You need to create a query that will detect when a user creates an unusually large numbers of Azure AD user accounts.
How should you complete the query? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
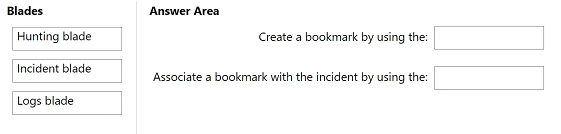
DRAG DROP -
You have a Microsoft Sentinel workspace that contains an Azure AD data connector.
You need to associate a bookmark with an Azure AD-related incident.
What should you do? To answer, drag the appropriate blades to the correct tasks. Each blade may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.
NOTE: Each correct selection is worth one point.
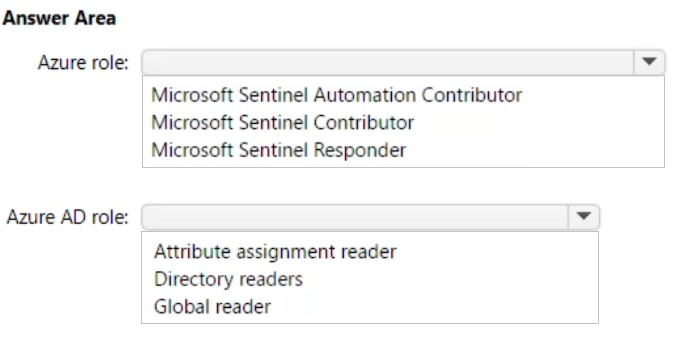
You have an Azure subscription that contains a guest user named User1 and a Microsoft Sentinel workspace named workspace1.
You need to ensure that User1 can triage Microsoft Sentinel incidents in workspace1. The solution must use the principle of least privilege.
Which roles should you assign to User1? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You have a Microsoft Sentinel workspace.
You enable User and Entity Behavior Analytics (UEBA) by using Audit Logs and Signin Logs.
The following entities are detected in the Azure AD tenant:
• App name: App1
• IP address: 192.168.1.2
• Computer name: Device1
• Used client app: Microsoft Edge
• Email address: [email protected]
• Sign-in URL: https://www.company.com
Which entities can be investigated by using UEBA?
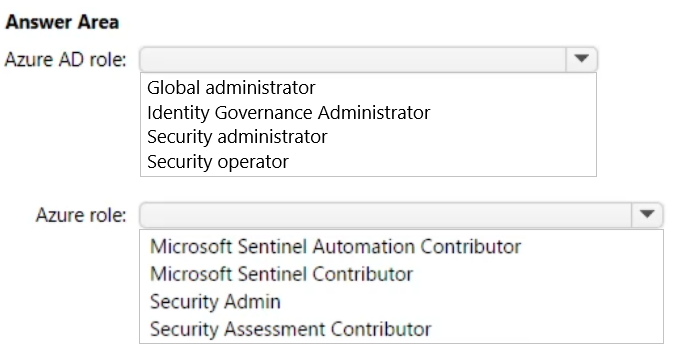
You have an Azure subscription that uses Microsoft Sentinel and contains a user named User1.
You need to ensure that User1 can enable User and Entity Behavior Analytics (UEBA) for entity behavior in Azure AD. The solution must use the principle of least privilege.
Which roles should you assign to User1? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
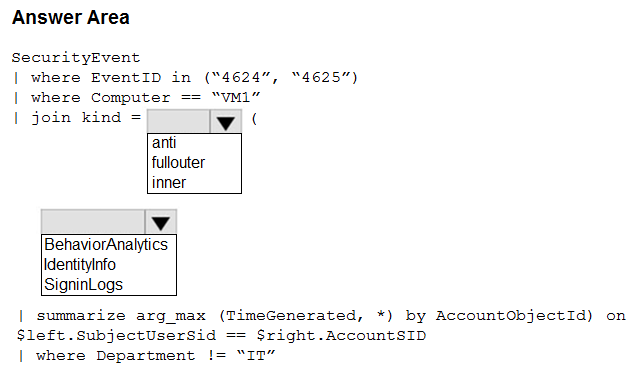
You have an Azure subscription that contains the following resources:
• A virtual machine named VM1 that runs Windows Server
• A Microsoft Sentinel workspace named Sentinel1 that has User and Entity Behavior Analytics (UEBA) enabled
You have a scheduled query rule named Rule1 that tracks sign-in attempts to VM1.
You need to update Rule1 to detect when a user from outside the IT department of your company signs in to VM1. The solution must meet the following requirements:
• Utilize UEBA results.
• Maximize query performance.
• Minimize the number of false positives.
How should you complete the rule definition? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
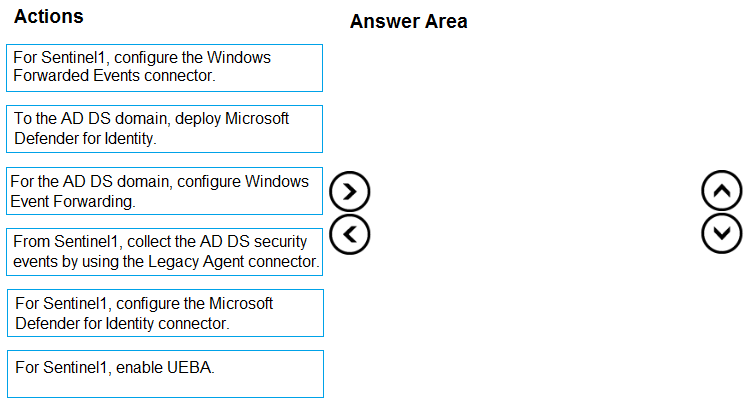
Your network contains an on-premises Active Directory Domain Services (AD DS) domain that syncs with an Azure AD tenant.
You have a Microsoft Sentinel workspace named Sentinel1.
You need to enable User and Entity Behavior Analytics (UEBA) for Sentinel1 and collect security events from the AD DS domain.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
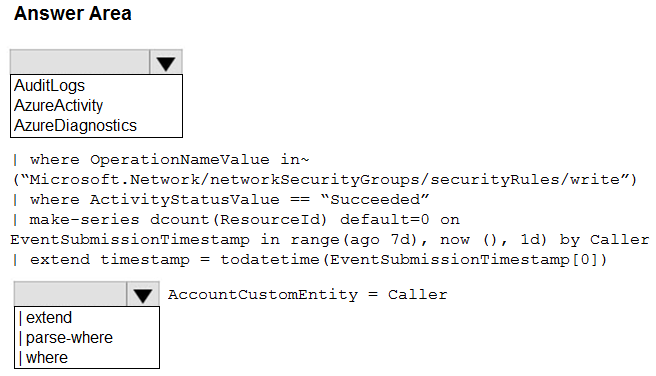
HOTSPOT -
You have an Azure subscription that contains a Microsoft Sentinel workspace.
You need to create a hunting query using Kusto Query Language (KQL) that meets the following requirements:
• Identifies an anomalous number of changes to the rules of a network security group (NSG) made by the same security principal.
• Automatically associates the security principal with a Microsoft Sentinel entity.
How should you complete the query? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You have a Microsoft Sentinel workspace that uses the Microsoft 365 Defender data connector.
From Microsoft Sentinel, you investigate a Microsoft 365 incident.
You need to update the incident to include an alert generated by Microsoft Defender for Cloud Apps.
What should you use?
You have a Microsoft Sentinel workspace.
You investigate an incident that has the following entities:
• A user account named User1
• An IP address of 192.168.10.200
• An Azure virtual machine named VM1
• An on-premises server named Server1
You need to label an entity as an indicator of compromise (IoC) directly by using the incidents page.
Which entity can you label?
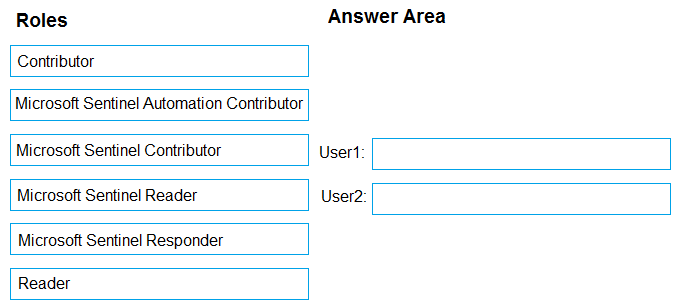
You have an Azure subscription that contains two users named User1 and User2 and a Microsoft Sentinel workspace named workspace1.
You need to ensure that the users can perform the following tasks in workspace1:
• User1 must be able to dismiss incidents and assign incidents to users.
• User2 must be able to modify analytics rules.
The solution must use the principle of least privilege.
Which role should you assign to each user? To answer, drag the appropriate roles to the correct users. Each role may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.
NOTE: Each correct selection is worth one point.
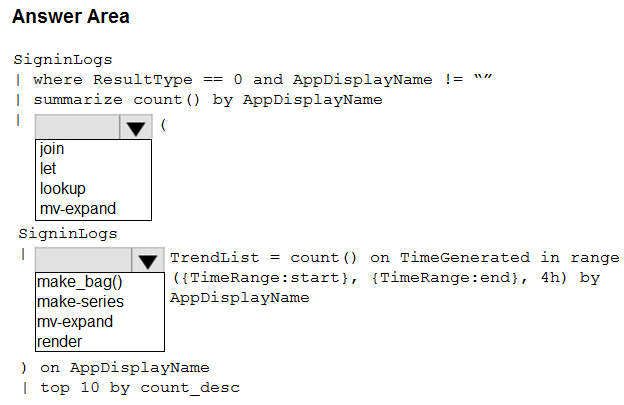
You have a Microsoft Sentinel workspace.
You need to configure a report visual for a custom workbook. The solution must meet the following requirements:
• The count and usage trend of AppDisplayName must be included.
• The TrendList column must be useable in a sparkline visual.
How should you complete the KQL query? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.