Loading questions...
Updated
Want a break from the ads?
Become a Supporter and enjoy a completely ad-free experience, plus unlock Learn Mode, Exam Mode, AstroTutor AI, and more.
Support Examcademy
Your support keeps this platform running. Become a Supporter to remove all ads and unlock exclusive study tools.
Study without distractions
Supporters get zero ads, spaced-repetition Learn Mode, timed Exam Mode, and AI-powered explanations from AstroTutor.
You are planning to upgrade Internet Explorer.
You have the following requirements:
✑ Create a report that identifies which computers are successfully upgraded.
✑ Do not install additional software on the client computers.
You need to design a deployment method that meets the requirements.
What should you do?
Your company's network has client computers that run Windows 7. Multiple users share the computers in the shipping department. These computers reside in the
Shipping Computers organizational unit (OU).
The company wants to deploy a new application. The application is not packaged.
You have the following requirements:
Deploy the application to all computers in the shipping department.

✑ Perform the deployment from a central location.
You need to plan the software deployment process to meet the requirements.
Which two actions should you include in the process? (Each correct answer presents part of the solution. Choose two.)
Your network has client computers that run Windows XP. All users access a custom line-of-business application. The line-of-business application is not compatible with Windows 7.
You are planning to deploy Windows 7.
You have the following requirements:
✑ The application must run on all client computers.
✑ The application executable must reside on each client computer.
You need to manage application compatibility to meet the requirements.
What should you do?
Your company has 1,000 client computers that run Windows XP Professional x64.
You are planning to deploy Windows 7 Enterprise x64.
The company uses an application that is incompatible with Windows 7 Enterprise x64.
You have the following requirements:
✑ Provide all users with access to the application.
✑ Deploy and manage the application by using a centralized solution.
You need to design a solution that meets the requirements.
What should you do?
Your company has 1,000 Windows XP computers. You plan to migrate these computers to Windows 7.
You need to detect compatibility issues that can occur during the installation and configuration process for a specific application.
Which tool should you use?
Your companys network has client computers that run Windows 7. Multiple users share the computers in the shipping department. These computers reside in the
Shipping Computers organizational unit (OU).
The network design is shown in the following diagram.
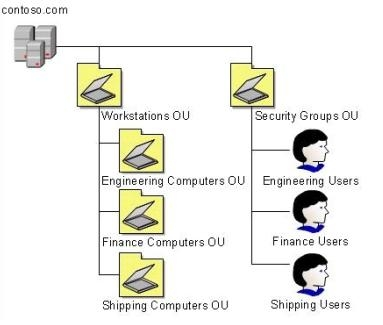
You are planning to deploy an application. The application is packaged as a Microsoft Windows Installer package (MSI).
You need to deploy the application only to computers in the shipping department.
Which two actions should you perform? (Each correct answer presents part of the solution. Choose two.)
Your companys network has client computers that run Windows 7.
When a user attempts to log on to the domain from a computer named Client1, she receives the following message: The system cannot log you on to this domain because the system's computer account in its primary domain is missing or the password on that account is incorrect.
You need to ensure that the user can log on to the domain from Client1.
What should you do?
Your company has two Active Directory Domain Services (AD DS) domains, Domain1 and Domain2. A two-way trust relationship exists between the domains.
Users in both domains can log on to client computers in only their own domains. System logs on the domain controllers display the error message Clock skew too great when users in Domain1 attempt to log on to client computers in Domain2.
You need to ensure that users can log on to client computers in both domains.
What should you do?
Your company has an Active Directory Domain Services (AD DS) forest with a single domain named contoso.com. The design of the organizational units (OUs) and Group Policy objects (GPOs) is shown in the following diagram.
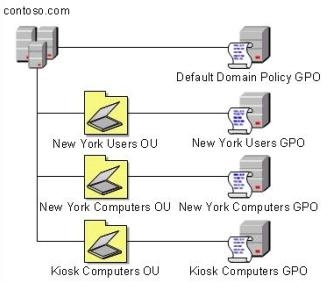
Multiple computer configuration settings and user configuration settings are defined in the Kiosk Computers GPO.
A security audit indicates that user configuration settings that are defined in the Kiosk Computers GPO are not applied when users log on to client computers that are in the Kiosk Computers OU.
You need to ensure that the user configuration settings are correctly applied.
What should you do?
You have a single Active Directory Domain Services (AD DS) site. All client computers run Windows 7. Users in the marketing department use a custom application.
You create a new Group Policy object (GPO) and link it to the site. Users in the marketing department then report that they are unable to use the custom application.
You need to ensure that all users in the marketing department are able to use the custom application. You need to ensure that all other users continue to receive the new GPO.
What should you do?
Your companys network includes client computers that run Windows 7.
You design a wireless network to use Extensible Authentication ProtocolCTransport Level Security (EAP-TLS). The Network Policy Server has a certificate installed.
Client computers are unable to connect to the wireless access points.
You need to enable client computers to connect to the wireless network.
What should you do?
Your company infrastructure includes a Windows Server 2008 R2 file server and 1,000 Windows 7 Enterprise client computers.
The company wants to require a secure connection between client computers and the file server.
You need to create and deploy a Group Policy object (GPO) that includes a rule for Windows Firewall with Advanced Security.
What should you do?
You deploy Windows 7 to the computers that are used by your companys Web developers. All Web developer user accounts are in a single organizational unit
(OU).
Internet Explorer is blocking pop-up windows for multiple internal Web applications that are hosted on different servers.
You need to use Group Policy to ensure that Internet Explorer does not block pop-up windows for internal Web applications.
What should you do?
Your network has client computers that run Windows 7 Enterprise. You plan to deploy new administrative template policy settings by using custom ADMX files.
You create the custom ADMX files, and you save them on a network share. You start Group Policy Object Editor (GPO Editor). The custom ADMX files are not available in the Group Policy editing session. You need to ensure that the ADMX files are available to the GPO Editor. What should you do?
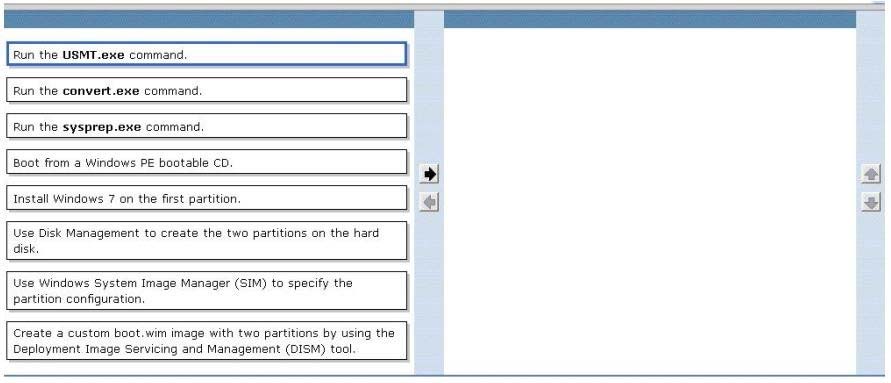
DRAG DROP -
You are planning to deploy Windows 7 Enterprise to all of your company's client computers.
You have the following requirements:
"¢ Create two custom partitions on each client computer's hard disk, one for the operating system and the other for data.
"¢ Automatically create the partitions during Windows Setup.
You need to design an image that meets the requirements.
Which two actions should you perform in sequence? (To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order)
Select and Place:
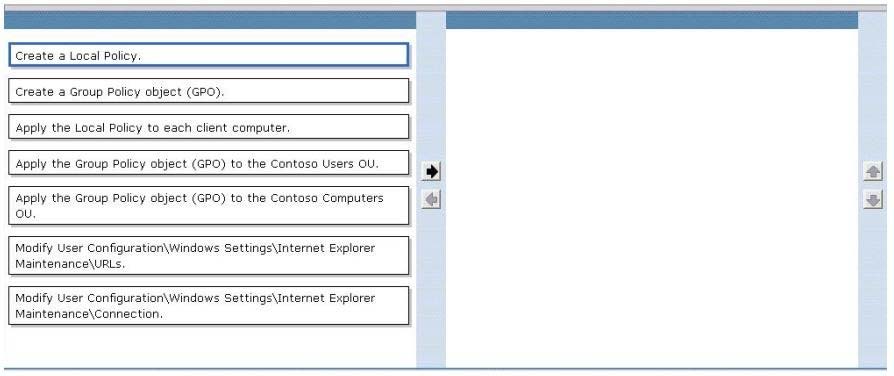
DRAG DROP -
All client computers in an organization run Windows 7 and are joined to an Active Directory Domain Services (AD DS) domain. All user objects are stored in an
Organizational Unit (OU) named Contoso Users. All computer objects are stored in an OU named Contoso Computers.
You need to add a proxy server to the Microsoft Internet Explorer 9 configuration on all client computers by using the least administrative effort.
Which three actions should you perform? (To answer, move the appropriate action from the list of actions to the answer area and arrange them in the correct order.)
Select and Place:
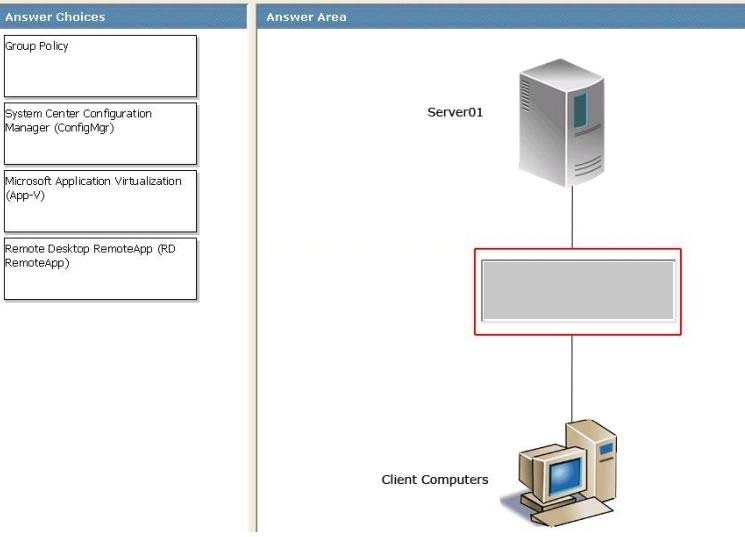
DRAG DROP -
You are designing an application deployment strategy.
Application deployments must meet the following requirements:
"¢ They must be able to use Setup.exe.
"¢ They must not require Active Directory.
"¢ They must not require a constant network connection.
"¢ The application installation schedule must be easy to set up and implement.
You need to recommend a method that meets the requirements.
What should you recommend? (To answer, drag the appropriate deployment method from the list of deployment methods to the correct location or locations in the work area.)
Select and Place:
When a user attempts to connect to a server named Server1 by using Remote Desktop Connection (RDC), he receives the following error message.
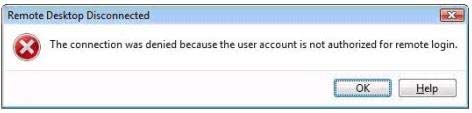
You need to assign the least amount of privilege to the user to ensure that he can connect to Server1 by using RDC.
To which group should you add the user?
A company has an Active Directory Domain Services (AD DS) forest with a single domain.
Domain controllers are located in the companys offices in New York and Boston.
You deploy a group policy at the domain level that includes security filtering.
You discover that Group Policy object (GPO) settings are being applied to computers in the New York office, but not to computers in the Boston office.
You suspect there might be replication problems with the policies. What should you do?
Your companys network has client computers that run Windows 7.
A software vendor releases version 2 of an application that your company uses.
Your company currently uses version 1. Version 1 and version 2 are not compatible.
You plan to deploy version 2 of the application.
You have the following requirements:
✑ Users must be able to run both versions of the application on their computers.
✑ Version 2 must be available when a client computer is not connected to the network.
You need to plan a software deployment process that meets the requirements. What should you do? (Choose all that apply.)
A company uses Microsoft Deployment Toolkit (MDT) 2010 to deploy Windows 7 Enterprise and Microsoft Office 2010. The company is replacing existing computers with new 64-bit computers.
You have the following requirements:
✑ You need to include Office 2010 with the deployment.
✑ You need to automate the deployment where possible.
✑ Some employees have accessibility requirements that require specialized hardware.
✑ The hardware must continue to be used after the deployment.
✑ The specialized hardware is compatible with Windows 7 but only 32-bit drivers are available from the manufacturer.
You need to create an image that meets these requirements.
What should you do? (Choose all that apply.)
Your company's network includes a main office and several branch offices. The branch offices are connected to the main office by high-latency links. All client computers run Windows 7 Enterprise, and all servers run Windows Server 2008 R2. Servers are located in each of the branch offices.
Client computers in the branch offices frequently access a specific group of files on a file server named Server1. These access requests consume significant amounts of bandwidth and reduce the speed of higher-priority traffic.
You need to reduce the bandwidth that is consumed by requests for frequently accessed files.
What should you do?
A Windows Server 2008 R2 server named SERVER01 has the Windows Deployment Services (WDS) role installed. SERVER02 is running DHCP services. You prestage computer objects in Active Directory. You plan to use WDS to deploy Windows 7 to the prestaged computers. When you try to deploy an image by using
PXE, the process fails. You need to ensure that SERVER01 responds to prestaged client computers only. From WDS, what should you do? (Choose all that apply.)
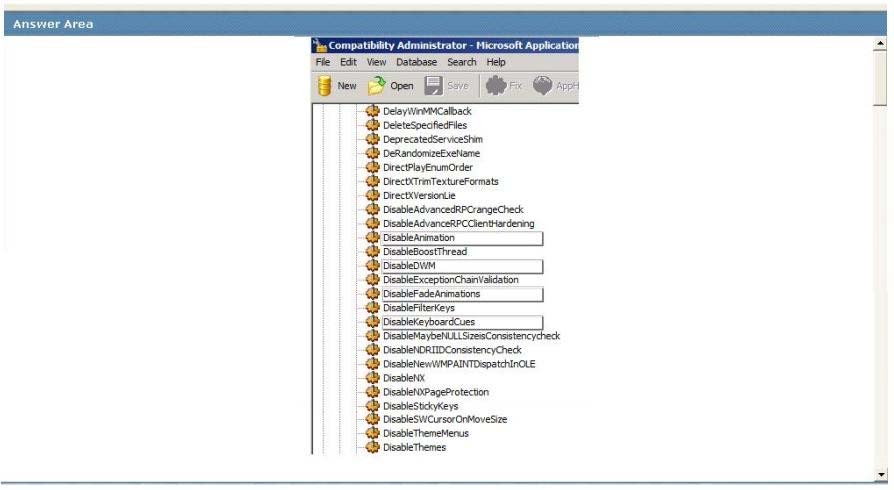
HOTSPOT -
You are preparing to install a 32-bit legacy application on all client computers in an organization.
The application requires specific compatibility settings in order to function in Windows 7. You run the 32-bit version of Compatibility Administrator and create a new application fix.
You need to create a shim database that includes a compatibility fix for applications that have known issues with the Desktop Window Manager.
Which compatibility modes should you select? To answer, select the appropriate setting in the work area.
Hot Area:
Your company has a custom Web application that uses a self-signed SSL certificate. The company has an internal certification authority (CA) and uses autoenrollment. When external users attempt to start the Web application, Internet Explorer displays an error message that recommends closing the Web page rather than continuing to the application. You need to ensure that Internet Explorer does not display the error message. What should you do?