Loading provider exams...
Sign Up & unlock 100% of Exam Questions
No Strings Attached!
Updated
You are designing a network management solution that provides automation for Junos devices. Your customer wants to know which solutions would require additional software to be deployed to existing Junos devices.
Which two solutions satisfy this scenario? (Choose two.)
You are implementing Routing Engine protection, and packets are processed in a specific order.
In this scenario, which function processed a received packet last?
You are deploying Security Director with the logging and reporting functionality for VMs that use SSDs. You expect to have approximately 20,000 events per second of logging in your network.
In this scenario, what is the minimum number of logging and reporting devices that should be used?
You are using SRX Series devices to secure your network and you require sandboxing for malicious file detonation. However, per company policy, you cannot send potentially malicious files outside your network for sandboxing.
Which feature should you use in this situation?
You are creating a security design proposal for an enterprise customer. As part of the design, you are implementing 802.1x authentication on your EX Series devices.
In this scenario, which two statements are correct? (Choose two.)
Want a break from the ads?
Become a Supporter and enjoy a completely ad-free experience, plus unlock Learn Mode, Exam Mode, AstroTutor AI, and more.
You are asked to install a mechanism to protect an ISP network from denial-of-service attacks from a small number of sources.
Which mechanism will satisfy this requirement?
You are responding to an RFP for securing a large enterprise. The RFP requires an onsite security solution which can use logs from third-party sources to prevent threats. The solution should also have the capability to detect and stop zero-day attacks.
Which Juniper Networks solution satisfies this requirement?
You are designing an SDSN security solution for a new campus network. The network will consist of Juniper Networks Policy Enforcer, Juniper Networks switches, third-party switches, and SRX Series devices. The switches and the SRX Series devices will be used as security enforcement points.
Which component supports the SRX Series devices in this scenario?
Your company has outgrown its existing secure enterprise WAN that is configured to use OSPF, AutoVPN, and IKE version 1. You are asked if it is possible to make a design change to improve the WAN performance without purchasing new hardware.
Which two design changes satisfy these requirements? (Choose two.)
You are concerned about malicious attachments being transferred to your e-mail server at work through encrypted channels. You want to block these malicious files using your SRX Series device.
Which two features should you use in this scenario? (Choose two.)
Click the Exhibit button.
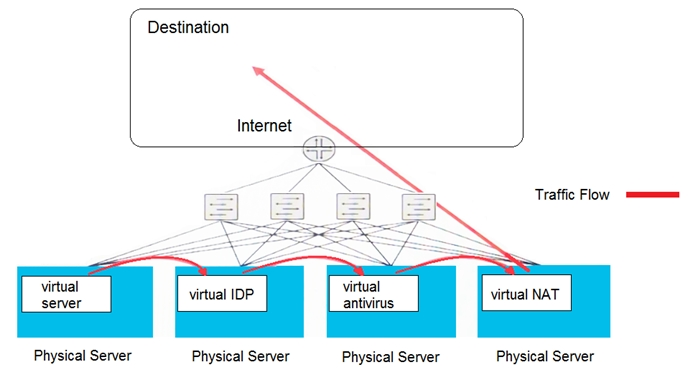
Which type of security solution is shown in this exhibit?
You are designing an Internet security gateway (ISG) for your company and are considering a centralized versus a distributed model for ISGs.
Which two statements are correct in this scenario? (Choose two.)
You are creating a data center security design. Virtual security functions must be performed on east-west traffic. Security functions must be commissioned and decommissioned frequently, and the least resource-intensive architecture must be used.
In this scenario, what will accomplish this task?
What are two reasons for using cSRX over vSRX? (Choose two.)
You will be managing 1000 SRX Series devices. Each SRX Series device requires basic source NAT to access the Internet.
Which product should you use to manage these NAT rules on the SRX Series devices?
Which two features are used to stop IP spoofing in and out of your network? (Choose two.)
What are two benefits of the vSRX in a virtualized private or public cloud multitenant environment? (Choose two.)
You are designing a new network for your organization with the characteristics shown below.
✑ All traffic must pass inspection by a security device.
✑ A center-positioned segmentation gateway must provide deep inspection of each packet using 10 Gbps interfaces.
✑ Policy enforcement must be centrally managed.
Which security model should you choose for your network design?
A hosting company is migrating to cloud-based solutions. Their customers share a physical firewall cluster, subdivided into individual logical firewalls for each customer. Projection data shows that the cloud service will soon deplete all the resources within the physical firewall. As a consultant, you must propose a scalable solution that continues to protect all the cloud customers while still securing the existing physical network.
In this scenario, which solution would you propose?
You are working on a network design that will use EX Series devices as Layer 2 access switches in a campus environment. You must include Junos Space in your design. You want to take advantage of security features supported on the devices.
Which two security features would satisfy this requirement? (Choose two.)
You are designing a data center interconnect between two sites across a service provider Layer 2 leased line. The sites require Layer 2 connectivity between hosts, and the connection must be secure.
In this scenario, what will accomplish this task?
You are designing a new campus Internet access service that implements dynamic NAT for customer IP addressing. The customer requires services that allow peer-to-peer networking and online gaming.
In this scenario, what will accomplish this task?
You are asked to virtualize numerous stateful firewalls in your customer's data center. The customer wants the solution to use the existing Kubernetes- orchestrated architecture.
Which Juniper Networks product would satisfy this requirement?
Your customer is getting ready to deploy a new WAN architecture. It must be simple to set up, address hub scaling concerns, and allow the automatic addition of new sites without requiring changes to the hub site. They want to deploy either AutoVPN or Auto Discovery VPN.
In this scenario, why would you propose Auto Discovery VPN as a solution?
You are designing a solution to protect a service provider network against volumetric denial-of-service attacks. Your main concern is to protect the network devices.
Which two solutions accomplish this task? (Choose two.)