Loading provider exams...
Sign Up & unlock 100% of Exam Questions
No Strings Attached!
Updated
A network administrator is in charge of a Mobility Master (MM) – Mobility Controller (MC) based WLAN. The administrator has deployed an Airwave Management Platform (AMP) server in order to improve the monitoring capabilities and generate reports and alerts.
The administrator has configured SNMPv3 and Admin credentials on both the MMs and MCs and has created Groups and Folders in the AMP server.
What two additional steps must the administrator do in order to let Airwave monitor the network devices? (Choose two.)
This exam has 54 community-verified practice questions. Create a free account to access all questions, comments, and explanations.
A customer wants a WLAN solution that permits Aps to terminate WPA-2 encrypted traffic from different SSIDs to different geographic locations where non-related IT departments will take care of enforcing security policies. A key requirement is to minimize network congestion, overhead, and delay while providing data privacy from the client to the security policy enforcement point. Therefore, the solution must use the shortest path from source to destination.
Which Aruba feature best accommodates this scenario?
Refer to the exhibit.
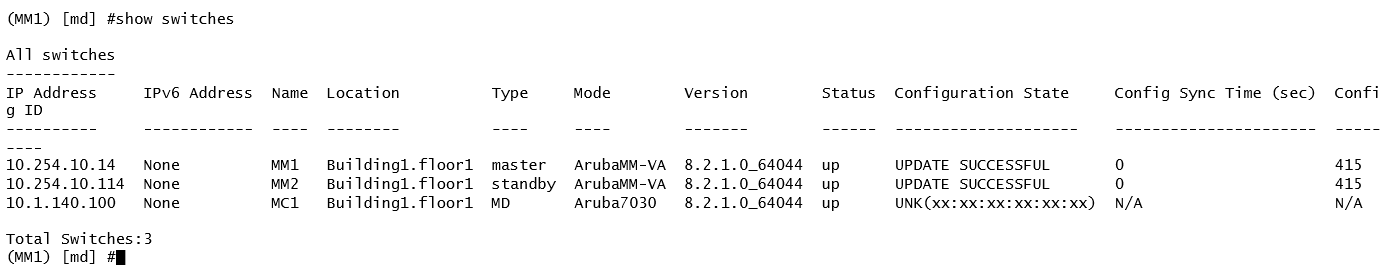
A network administrator adds a Mobility Controller (MC) in the /mm level and notices that the device does not show up in the managed networks hierarchy. The network administrator accesses the CLI. executes the show switches command, and obtains the output shown in the exhibit.
What is the reason that the MC does not appear as a managed device in the hierarchy?
Refer to the exhibits.
Exhibit 1 -
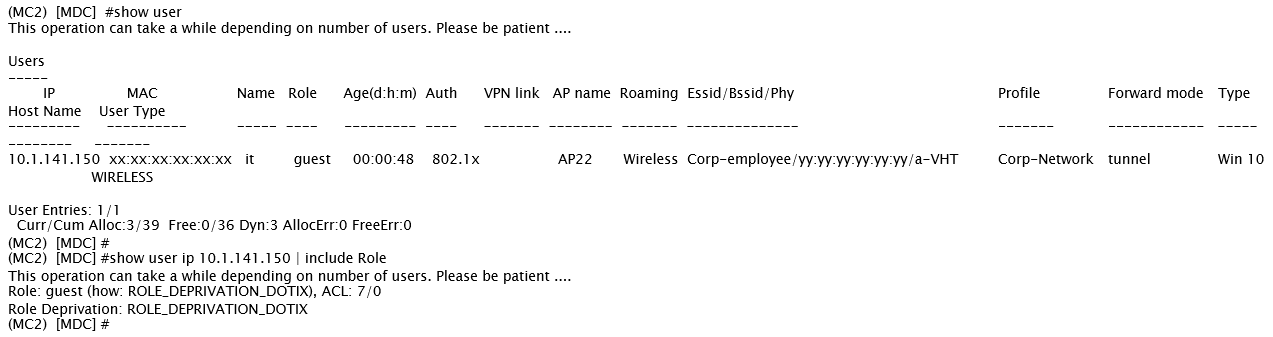
Exhibit 2 -
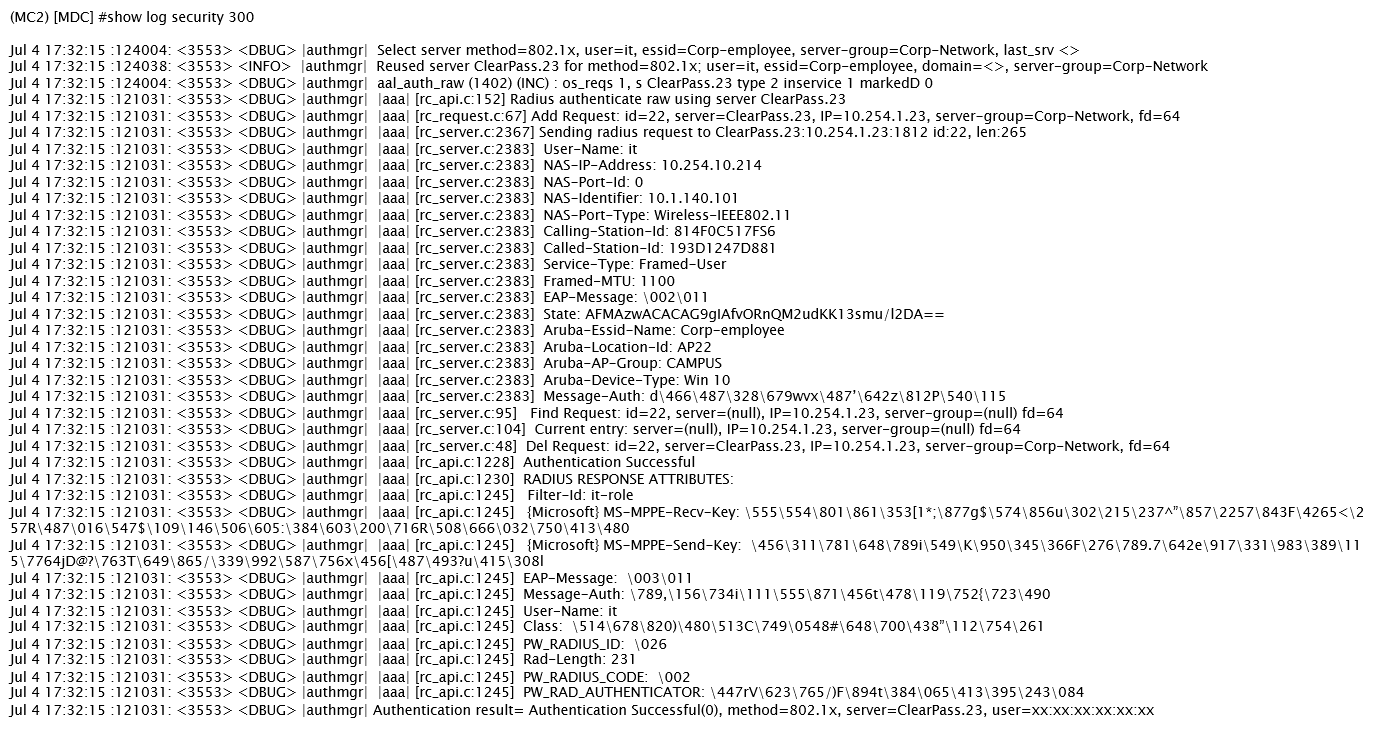
A network administrator integrates a current Mobility Master (MM) - Mobility Controller (MC) deployment with a RADIUS server to authenticate a wireless user, the network administrator realizes that the client machine is not failing into the it_department role, as shown the exhibits.
Which configuration is required to map the users into the proper role, based on standard attributes returned by the RADIUS server in the Access Accept message?
Refer to the exhibits -
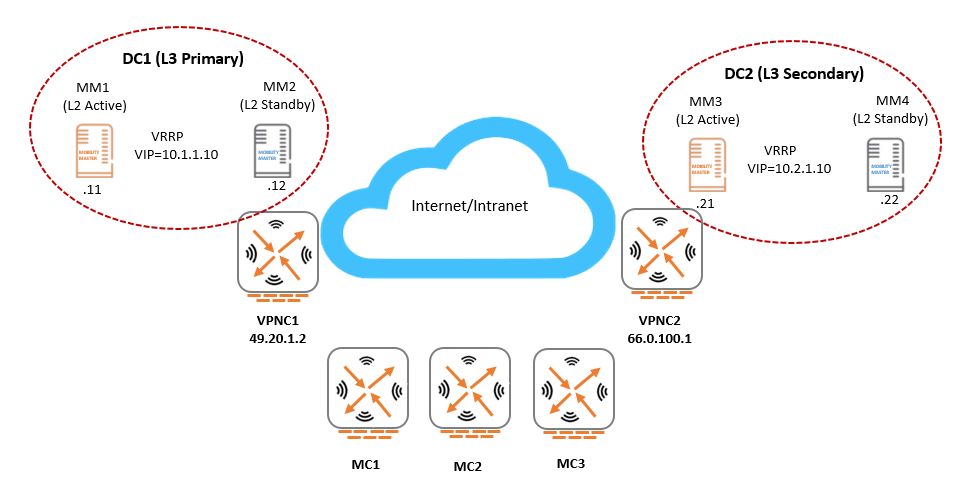
An Aruba network is deployed with L2 and L3 Mobility Master (MM) redundancy across two datacenters, as shown in the exhibit. The network administrator confirms that all Mobility Controllers (MC) are currently communicating with MM1, which is the L2 Active and, L3 Primary.
Which MM IP will MCs communicate with if MM1 fails?
Want a break from the ads?
Become a Supporter and enjoy a completely ad-free experience, plus unlock Learn Mode, Exam Mode, AstroTutor AI, and more.
An organization owns a fully functional multi-controller Aruba network with a Virtual Mobility Master (VMM) in VLAN20. They have asked a network consultant to deploy a redundant MM on a different server. The solution must offer the lowest convergence time and require no human interaction in case of failure.
The servers host other virtual machines and are connected to different switches that implement ACLs to protect them. The organization grants the network consultant access to the servers only, and appoints a network administrator to assist with the deployment.
What must the network administrator do so the network consultant can successfully deploy the solution? (Choose two.)
Refer to the exhibit.
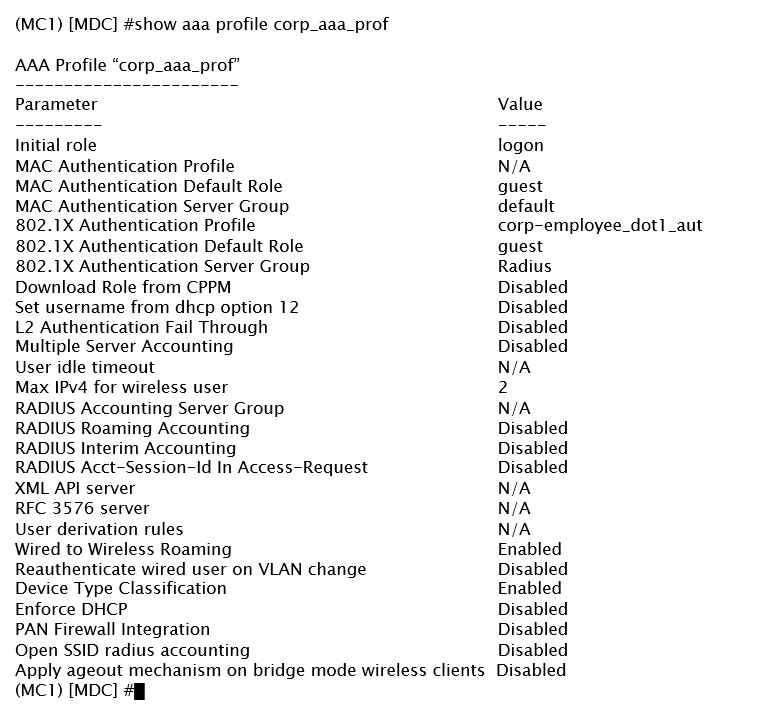
A network administrator has created AAA profile for the corporate VAP. In addition to the regular Radius based authentication, the administrator needs to be able to disconnect the users from either of the two servers that are part of the “Radius” server group.
What must the administrator do next in order to achieve this goal?
A network administrator has racked up a 7210 Mobility Controller (MC) that will be terminating 200+ Aps on a medium-size branch office. Next, the technician cabled the appliance with 4SPF+ Direct Attached Cables (DACs) distributed between two-member switching stack and powered it up.
What must the administrator do next in the MCs to assure maximum wired bandwidth utilization?
Refer to the exhibit.
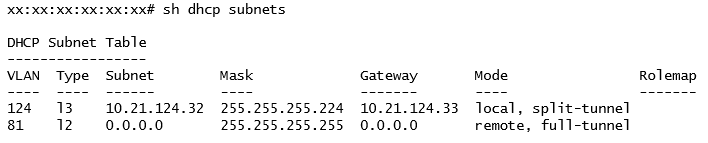
A network engineer deploys two different DHCP pools in an Instant AP (IAP) cluster for WLANs that will have connectivity to a remote site using Aruba IPSec.
Based on the output shown in the exhibit, which IAP-VPN DHCP modes are being used?
Refer to the exhibit.
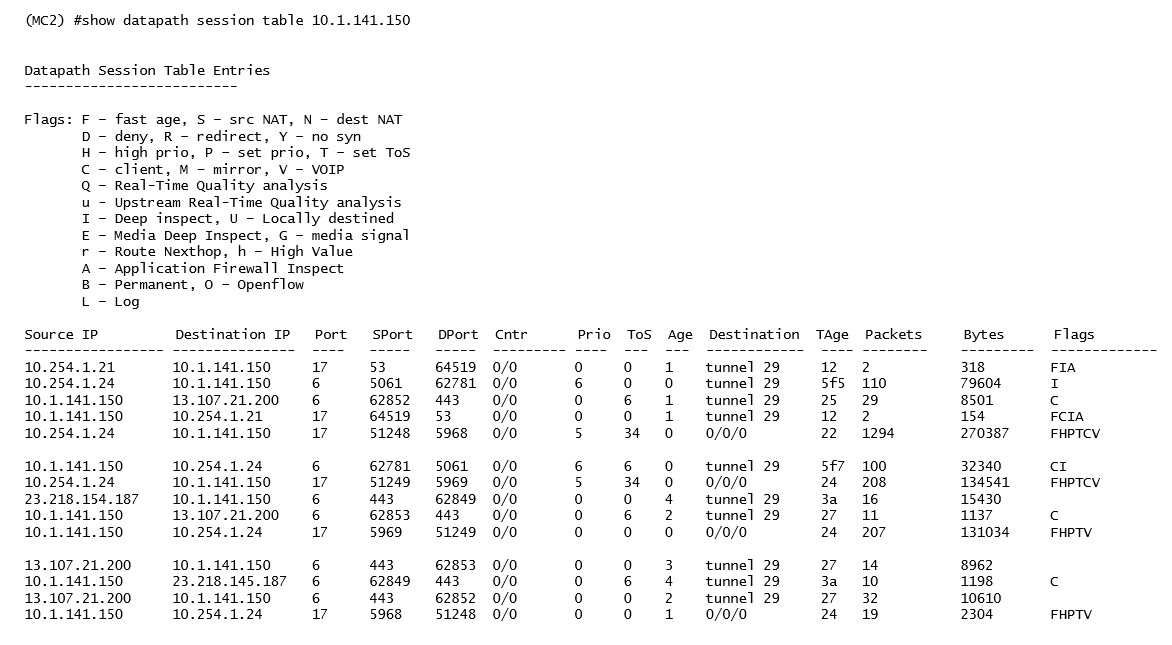
A network administrator deploys DSCP based prioritization in the entire wired network to improve voice quality for a SIP-based IP telephony system used by the company. However, users report that calls they make from WLAN have poor audio quality, while desktop phones do not experience the same problem. The network administrator makes a test call and looks in the datapath session table.
Based on the output shown in the exhibit, what is one area that the network administrator should focus on?
Refer to the exhibit.
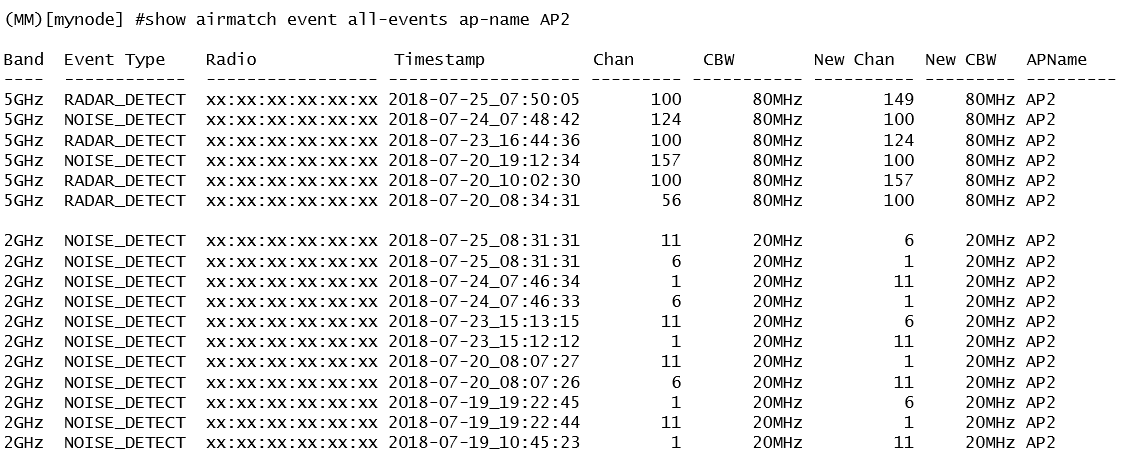
A network administrator deploys a Mobility Master (MM) - Mobility Controller (MC) network with Aps in different locations. Users in one of the locations report that the WiFi network works fine for several hours, and then they are suddenly disconnected. This symptom may happen at any time, up to three times every day, and lasts no more than two minutes.
After some research, the network administrator logs into the MM and reviews the output shown in the exhibit.
Based on this information, what is the most likely reason users get disconnected?
Refer to the exhibit.
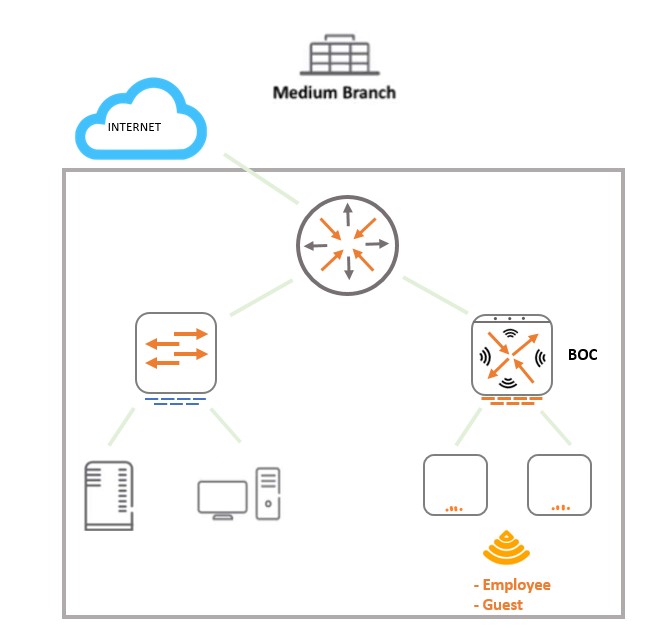
A 7008 Branch Office Controller (BOC) is deployed in a remote office behind a core router. This core does not support 802.1q encapsulation. The Mobility Controller (MC) is the gateway for two tunneling mode SSIDs, as shown in the exhibit.
Which two different configuration options ensure that wireless users are able to reach the branch network through the router? (Choose two.)
An Aruba Mobility Master (MM) - Mobility Controller (MC) solution is connected to a wired network that is ready to prioritize DSCP marked traffic. A group of WMM-enabled clients sends traffic marked at L2 only.
What must the network administrator do to map those markings to DSCP equivalent values when traffic is received by the APs?
A company with 50 small coffee shops in a single country requires a single mobility solution that solves connectivity needs at both the main office and branch locations. Coffee shops must be provisioned with local WiFi internet access for customers.
The shops must also have a private WLAN that offers communication to resources at the main office to upload sales, request supplies through a computer system, and make phone calls if needed. In order to simplify network operations, network devices at the coffee shops should be cloud managed.
Which technologies best meet the company needs at the lowest cost?
Refer to the exhibit.
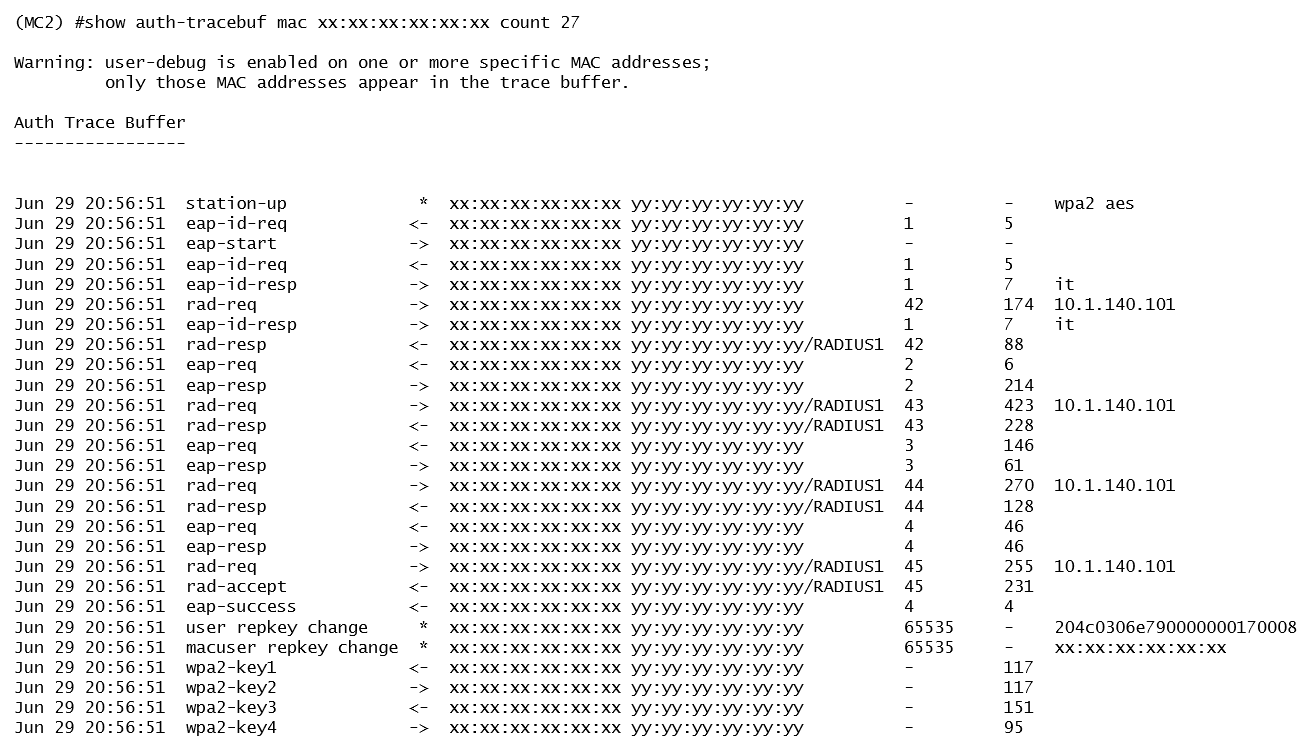
Based on the output shown in the exhibit, which wireless connection phase has just completed?
Refer to the exhibit.
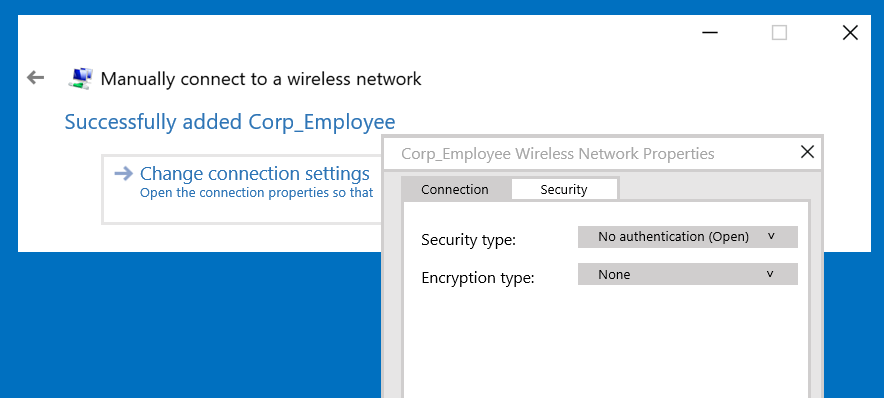
A network administrator wants to configure an 802.1x supplicant for a wireless network that includes the following:
• AES encryption
• EAP-MSCHAP v2-based user and machine authentication
• Validation of server certificate in Microsoft Windows 10
The network administrator creates a WLAN profile and selects the change connection settings option. Then the network administrator changes the security type to Microsoft: Protected EAP (PEAP), and enables user and machine authentication under Additional Settings.
What must the network administrator do next to accomplish the task?
Refer to the exhibits.
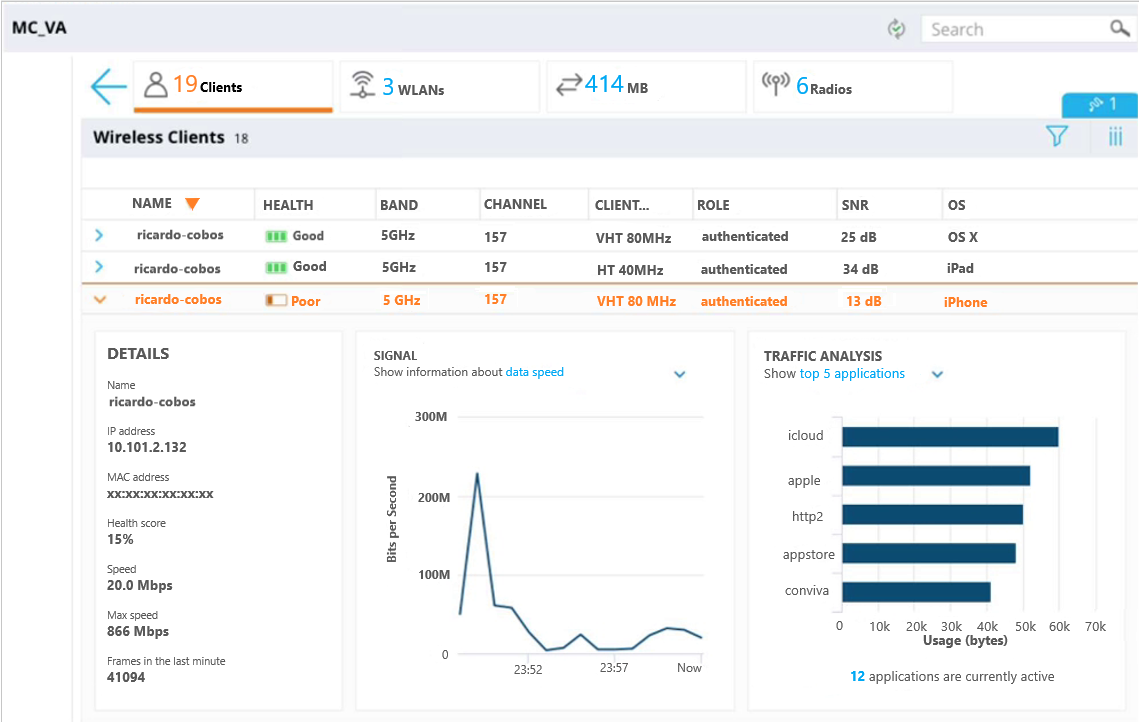
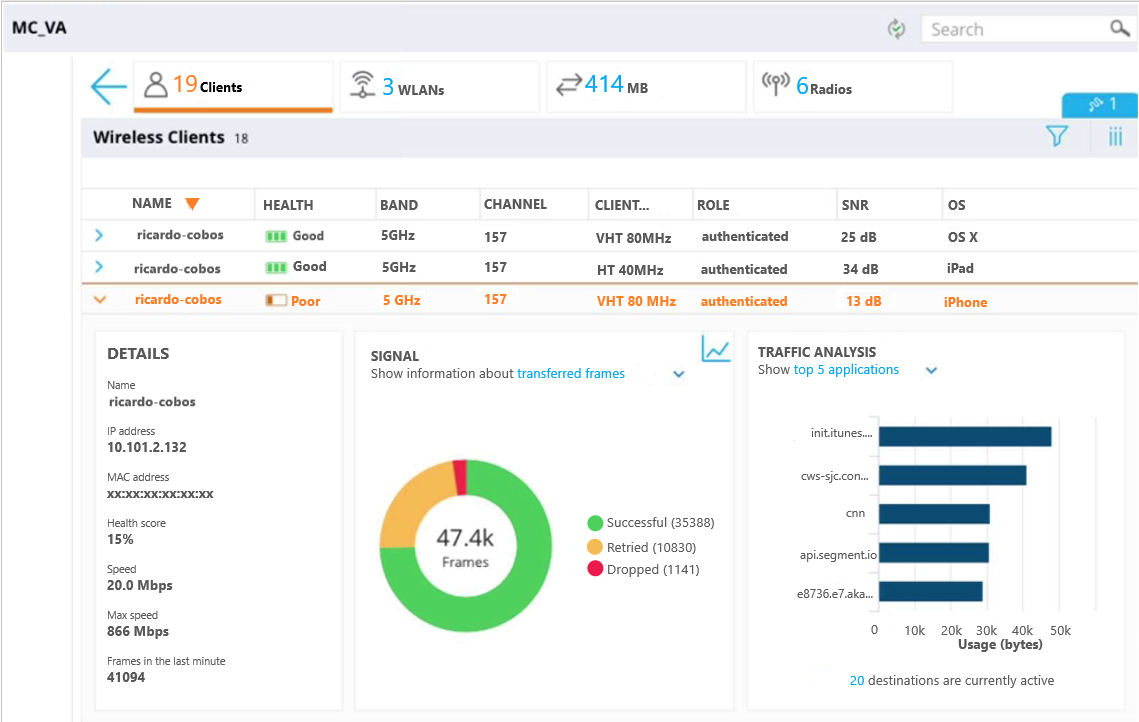
A user reports slow response time to a network administrator and suggests that there might be a problem with the WLAN. The user’s phone supports 802.11ac in the 5 GHz band. The network administrator finds the user in the Mobility Master (MM) and reviews the output shown in the exhibit.
What can the network administrator conclude after analyzing the data?
Refer to the exhibits.
Exhibit 1 -
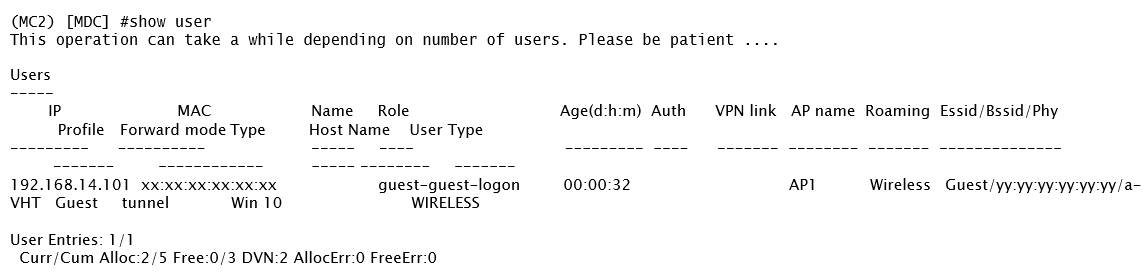
Exhibit 2 -
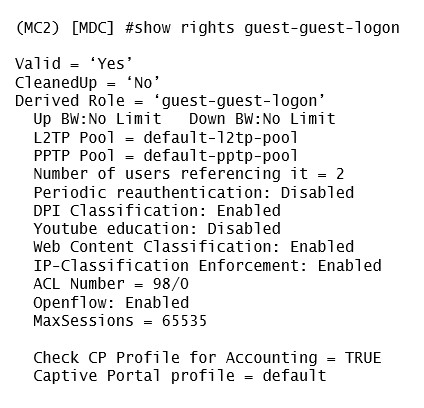
Exhibit 3 -
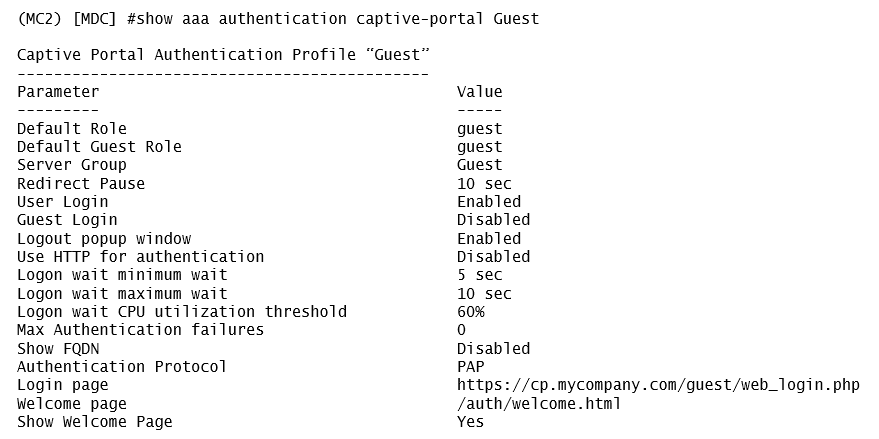
Exhibit 4 -
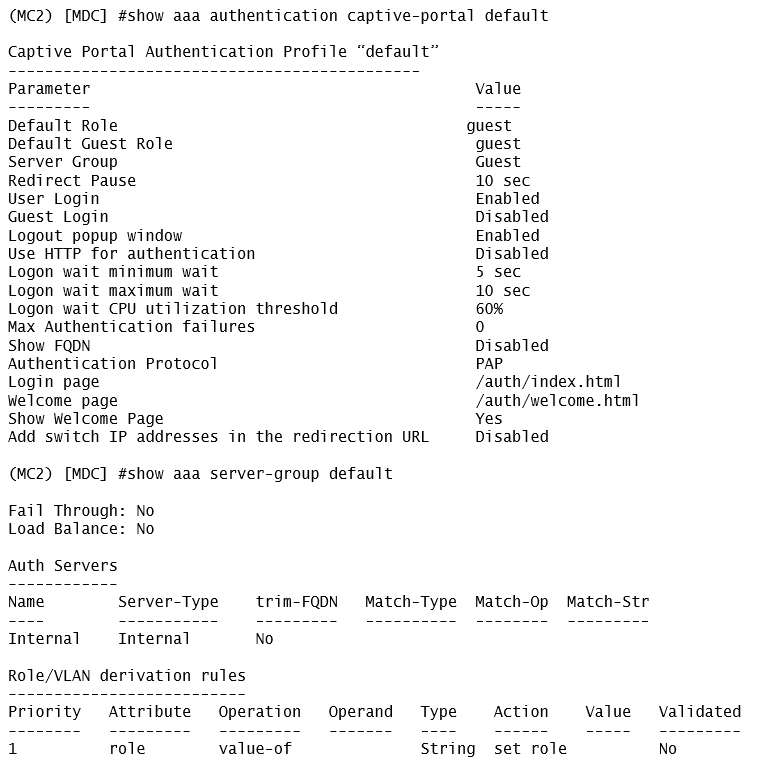
A captive portal-based solution is deployed in a Mobility Master (MM) - Mobility Controller (MC) network. A wireless station connects to the network and attempts the authentication process. The outputs are shown in the exhibits.
Which names correlate with the authentication and captive portal servers?
Refer to the exhibits.
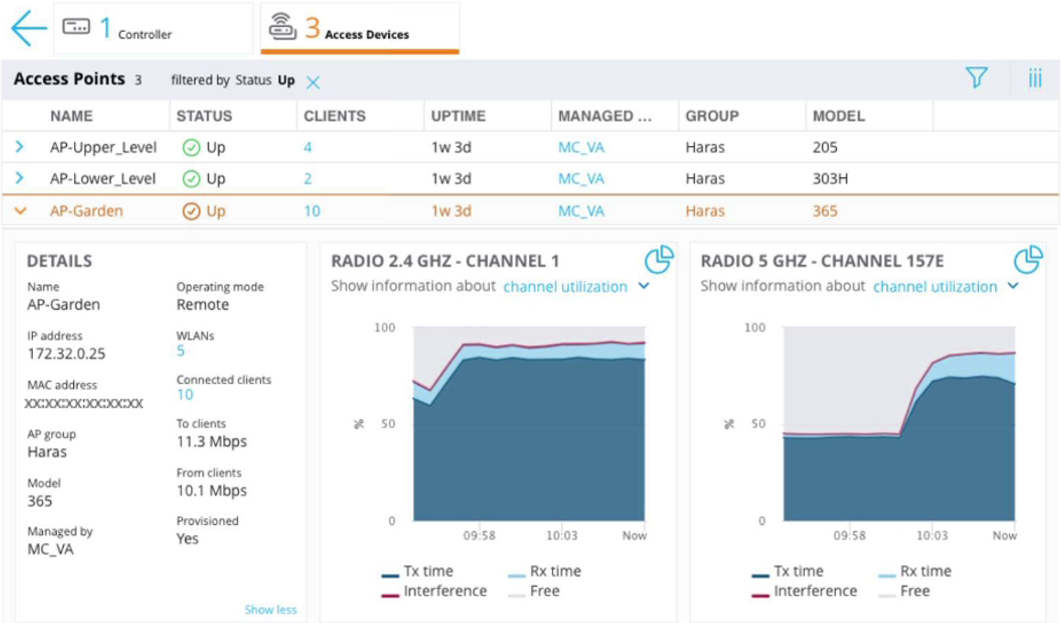
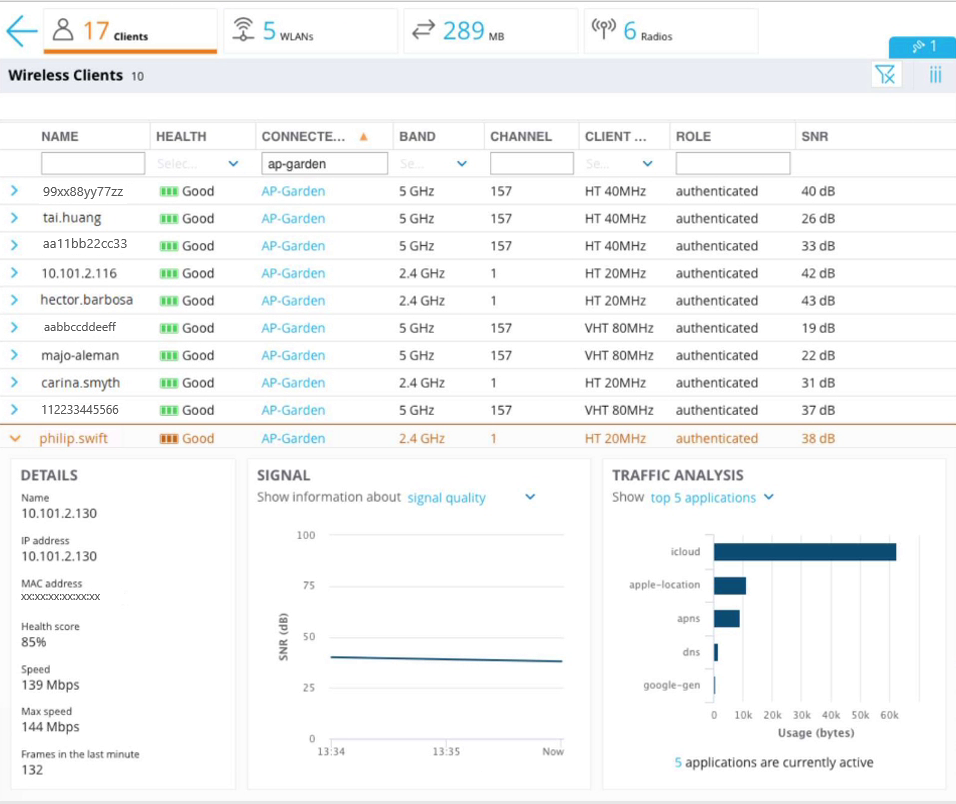
A user reports slow connectivity to a network administrator when connecting to AP-Garden and suggests that there might be a problem with the WLAN. The user’s device supports 802.11n in the 2.4 GHz band. The network administrator finds the user in the Mobility Master (MM) and reviews the output shown in the exhibit.
What can the network administrator conclude after analyzing the data?
A network administrator is in charge of a Mobility Master (MM) – Mobility Controller (MC) based network security. Recently the Air Monitors detected a Rogue AP in the network and the administrator wants to enable “Tarpit” based wireless containment.
What profile must the administrator enable “tarpit” wireless containment on?
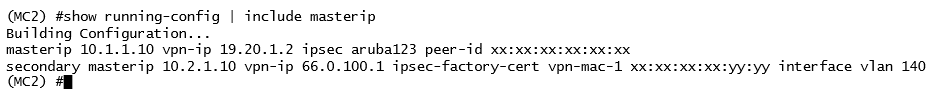
Refer to the exhibits.
Exhibit 1 -
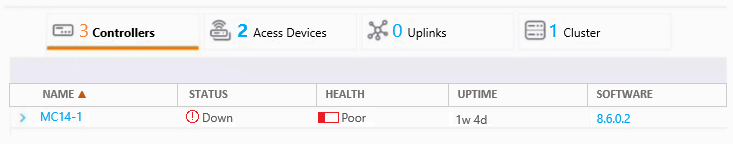
Exhibit 2 -
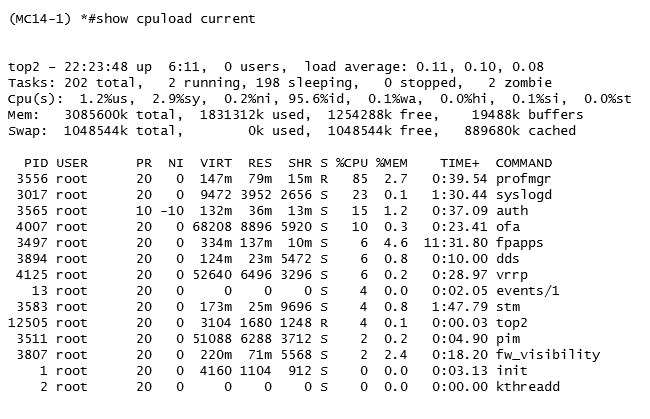
A network administrator adds a new Mobility Controller (MC) to the production Mobility Master (MM) and deploys APs that start broadcasting the employee SSID in the West wing of the building. Suddenly, the employees report client disconnects. When accessing the MM the network administrator notices that the MC is unreachable, then proceeds to access the MC’s console and obtains the outputs shown in the exhibits.
What should the network administrator do next to solve the current problem?
Refer to the exhibit.
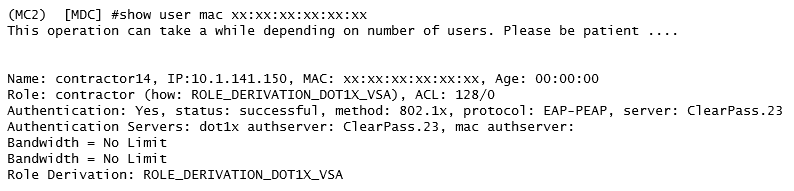
A network administrator is evaluating a deployment to validate that a user is assigned the proper role and reviews the output in the exhibit. How is the role assigned to user?