Loading provider exams...
Sign Up & unlock 100% of Exam Questions
No Strings Attached!
Updated
Which of the following tools is an open source protocol analyzer that can capture traffic in real time?
John works as a professional Ethical Hacker. He is assigned a project to test the security of www.abc.com. You have searched all open ports of the ABC server. Now, you want to perform the next information-gathering step, i.e., passive OS fingerprinting.
Which of the following tools can you use to accomplish the task?
Which of the following protocols is used by TFTP as a file transfer protocol?
Which of the following steps are generally followed in computer forensic examinations?
Each correct answer represents a complete solution. (Choose three.)
Which of the following monitors program activities and modifies malicious activities on a system?
Want a break from the ads?
Become a Supporter and enjoy a completely ad-free experience, plus unlock Learn Mode, Exam Mode, AstroTutor AI, and more.
Which of the following wireless security features provides the best wireless security mechanism?
David works as the Security Manager for ABC Inc. He has been assigned a project to detect the attacks over multiple connections and sessions and to count the number of scanned ports in a defined time period.
Which of the following rulebases will he use to accomplish the task?
Which of the following terms is used to represent IPv6 addresses?
You work as a Security Administrator for ABC Inc. You have implemented and configured a web application security scanner in the company's network. It helps in the automated review of the web applications with the defined purpose of discovering security vulnerabilities. In order to perform this task, the web application security scanner examines a number of vulnerabilities.
What are these vulnerabilities?
Each correct answer represents a complete solution. (Choose three.)
Which of the following information must the fragments carry for the destination host to reassemble them back to the original unfragmented state?
Each correct answer represents a complete solution. (Choose all that apply.)
Which of the following types of IP actions are supported by an IDP rulebase? (Choose three.)
You work as a Network Administrator for ABC Inc. You want to configure Snort as an IDS for your company's wireless network, but you are concerned that Snort does not support all types of traffic.
What traffic does Snort support?
Each correct answer represents a complete solution. (Choose all that apply.)
Which of the following parts of IP header is used to specify the correct place of the fragment in the original un-fragmented datagram?
An attacker changes the address of a sub-routine in such a manner that it begins to point to the address of the malicious code. As a result, when the function has been exited, the application can be forced to shift to the malicious code. The image given below explains this phenomenon:
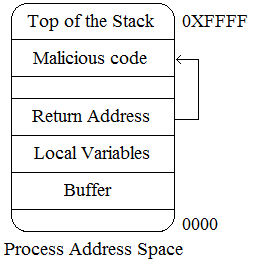
Which of the following tools can be used as a countermeasure to such an attack?
Which of the following forms on NAT maps multiple unregistered IP addresses to a single registered IP address by using different ports?
Which of the following tools is used to detect wireless LANs using the 802.11b, 802.11a, and 802.11g WLAN standards on the Windows platform?
Which of the following applications cannot proactively detect anomalies related to a computer?
You work as a Network Administrator for ABC Inc. The company has a TCP/IP-based routed network. Two routers have been configured on the network. A router receives a packet.
Which of the following actions will the router take to route the incoming packet?
Each correct answer represents a part of the solution. (Choose two.)
Which of the following techniques allows probing firewall rule-sets and finding entry points into the targeted system or network?
Which of the following honeypots is a low-interaction honeypot and is used by companies or corporations for capturing limited information about malicious hackers?
The simplest form of a firewall is a packet filtering firewall. Typically, a router works as a packet-filtering firewall and has the capability to filter on some of the contents of packets.
On which of the following layers of the Open System Interconnection (OSI) reference model do these routers filter information?
Each correct answer represents a complete solution. (Choose all that apply.)
Which of the following utilities provides an efficient way to give specific users permission to use specific system commands at the root level of a Linux operating system?
Which of the following firewalls operates at three layers - Layer3, Layer4, and Layer5?
Which of the following hexadecimal values in the boot field in the configuration register loads the first IOS file found in Flash memory?
Jain works as a professional Ethical Hacker. He has been assigned the project of testing the security of www.abc.com.
He has successfully completed the following steps of the preattack phase:
>> Information gathering
>> Determining network range
>> Identifying active machines
>> Finding open ports and applications
>> OS fingerprinting
>> Fingerprinting services
Now Jain wants to perform network mapping of the ABC network.
Which of the following tools can he use to accomplish his task?
Each correct answer represents a complete solution. (Choose all that apply.)