Loading provider exams...
Sign Up & unlock 100% of Exam Questions
No Strings Attached!
Updated
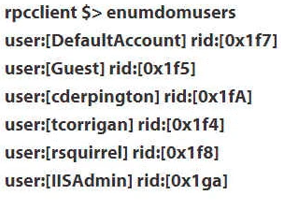
Which of the following accounts is an Administrator account?
Which of the following occurs when a penetration tester attempts to connect to a host with the following command? net use \192.168.44.213
An attacker is launching an attack against an input field in a form that is used to retrieve restricted information that is filtered dependent upon the privileges of the logged in user. This attacker inserts "' or 1=1;--" into this field. What is most likely the attacker's desired result from this insertion?
Adam works as an Incident Handler for Umbrella Inc. He has been sent to the California unit to train the members of the incident response team. As a demo project he asked members of the incident response team to perform the following actions:
✑ Remove the network cable wires.
✑ Isolate the system on a separate VLAN
✑ Use a firewall or access lists to prevent communication into or out of the system.
✑ Change DNS entries to direct traffic away from compromised system
Which of the following steps of the incident handling process includes the above actions?
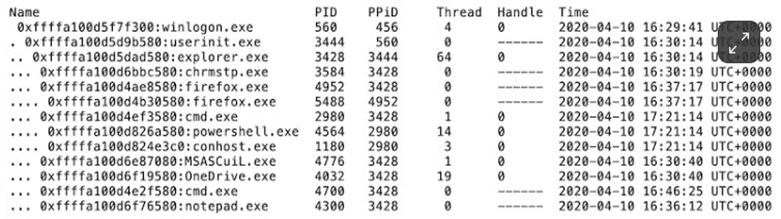
Which of the following statements describes the Volatility pstree plugin data shown in the image?
Want a break from the ads?
Become a Supporter and enjoy a completely ad-free experience, plus unlock Learn Mode, Exam Mode, AstroTutor AI, and more.
A consultant provides an organization with a report that contains their users' most popular passwords, data on password sharing, and a breakdown of password length by department. Which tool could generate this report?
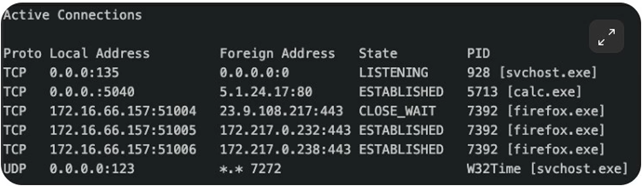
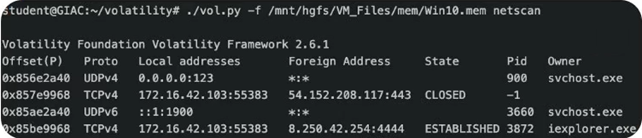
Which of the processes, shown in the output below, should be prioritized for examination during live response?
Command run: C:> netstat -naob -
Output: see screen capture (irrelevant lines of output omitted for space)
You have gained access to a Linux box. Which of the following methods would enable you to launch attacks against other systems and send the sessions back to your home PC (10.2.200.1) without altering system config files on the Linux box that might alert the sysadmin?
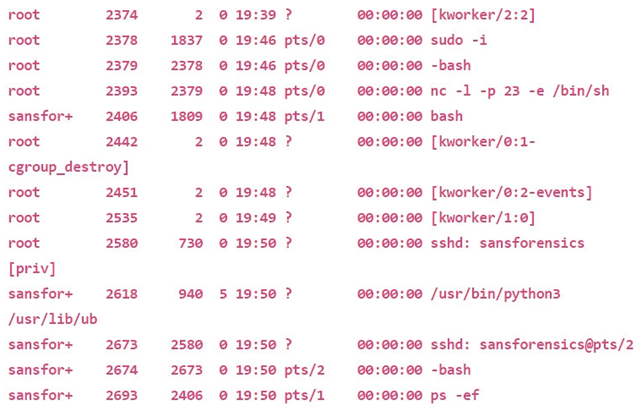
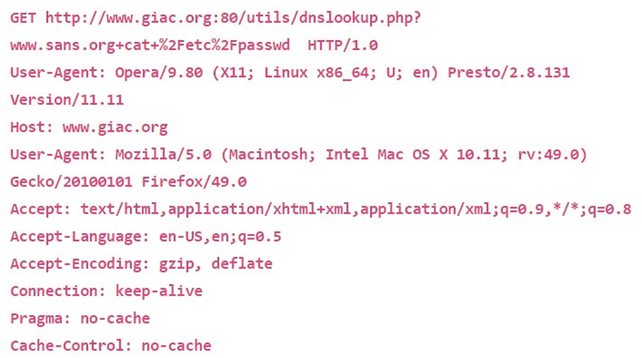
An organization has an SSH server that was compromised. Given the following evidence, what most likely occurred?
What john format should be specified to crack an 18 character Windows password?
How should an incident handler classify the following event shown in the output below?
Using the command below, to which share will the user be connected on 192.168.99.10?
C:> net use \192.168.99.10
Which of the following is a suspicious entry in the Volatility output attached?
Which of the following describes code wrapping?
Which of the following files would grow to a large size as a result of a brute force attack?
What is the destination endpoint host for the SSH session shown below?
ssh - L 1777:192.168.1.80:23 [email protected]
A security team is actively monitoring windows event IDs 4634, 4688, and 4697. Which persistence mechanism will they detect with this approach?
Which persistence mechanism will evade detection by Sysinternals AutoRuns?
What can a Linux administrator use to take advantage of RADIUS?
You are responding to an incident in which the organization's Extranet server has been compromised. The Extranet is the browser home page for most users in the organization. You have been instructed to watch the attacker, but minimize the business impact and the risk of further compromise. How can you continue providing services to the organization's users while isolating the compromised server?
As a professional hacker, you want to crack the security of secureserver.com. For this, in the information gathering step, you performed scanning with the help of nmap utility to retrieve as many different protocols as possible being used by the secureserver.com so that you could get the accurate knowledge about what services were being used by the secure server.com. Which of the following nmap switches have you used to accomplish the task?
Which of the following techniques is used when a system performs the penetration testing with the objective of accessing unauthorized information residing inside a computer?
In the DNS Zone transfer enumeration, an attacker attempts to retrieve a copy of the entire zone file for a domain from a DNS server. The information provided by the DNS zone can help an attacker gather user names, passwords, and other valuable information. To attempt a zone transfer, an attacker must be connected to a DNS server that is the authoritative server for that zone. Besides this, an attacker can launch a Denial of Service attack against the zone's DNS servers by flooding them with many requests. Which of the following tools can an attacker use to perform a DNS zone transfer?
Each correct answer represents a complete solution. (Choose all that apply.)
Which of the following types of malware can an antivirus application disable and destroy?
Each correct answer represents a complete solution. (Choose all that apply.)
You work as an Incident handling manager for a company. The public relations process of the company includes an event that responds to the e-mails queries.
But since few days, it is identified that this process is providing a way to spammers to perform different types of e-mail attacks. Which of the following phases of the Incident handling process will now be involved in resolving this process and find a solution?
Each correct answer represents a part of the solution. (Choose all that apply.)