Loading provider exams...
Sign Up & unlock 100% of Exam Questions
No Strings Attached!
Updated
John works as a professional Ethical Hacker. He has been assigned the project of testing the security of www.we-are-secure.com. He receives the following e- mail:
The e-mail that John has received is an example of __________.
Which utility enables you to access files from a Windows .CAB file?
Adam works as a Computer Hacking Forensic Investigator for a garment company in the United States. A project has been assigned to him to investigate a case of a disloyal employee who is suspected of stealing design of the garments, which belongs to the company and selling those garments of the same design under different brand name. Adam investigated that the company does not have any policy related to the copy of design of the garments. He also investigated that the trademark under which the employee is selling the garments is almost identical to the original trademark of the company. On the grounds of which of the following laws can the employee be prosecuted?
You work as a Network Administrator for Perfect Solutions Inc. You install Windows 98 on a computer. By default, which of the following folders does Windows 98 setup use to keep the registry tools?
Which of the following tools can be used to perform tasks such as Windows password cracking, Windows enumeration, and VoIP session sniffing?
Want a break from the ads?
Become a Supporter and enjoy a completely ad-free experience, plus unlock Learn Mode, Exam Mode, AstroTutor AI, and more.
Which of the following modules of OS X kernel (XNU) provides the primary system program interface?
Which of the following Acts enacted in United States allows the FBI to issue National Security Letters (NSLs) to Internet service providers (ISPs) ordering them to disclose records about their customers?
TCP FIN scanning is a type of stealth scanning through which the attacker sends a FIN packet to the target port. If the port is closed, the victim assumes that this packet was sent mistakenly by the attacker and sends the RST packet to the attacker. If the port is open, the FIN packet will be ignored and the port will drop the packet. Which of the following operating systems can be easily identified with the help of TCP FIN scanning?
Which of the following encryption methods uses AES technology?
Which of the following is the first computer virus that was used to infect the boot sector of storage media formatted with the DOS File Allocation Table (FAT) file system?
Which of the following file systems contains hardware settings of a Linux computer?
Which of the following is a set of exclusive rights granted by a state to an inventor or his assignee for a fixed period of time in exchange for the disclosure of an invention?
Which of the following tools are used for footprinting?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following switches of the XCOPY command copies attributes while copying files?
Mark works as a Network Administrator for Net Perfect Inc. The company has a Linux-based network. Mark installs a Checkpoint Firewall NGX on a
SecurePlatform device. He performs a scheduled backup of his system settings and products configuration. Where are these backup files stored?
Each correct answer represents a complete solution. Choose all that apply.
John works for an Internet Service Provider (ISP) in the United States. He discovered child pornography material on a Web site hosted by the ISP. John immediately informed law enforcement authorities about this issue. Under which of the following Acts is John bound to take such an action?
Nathan works as a professional Ethical Hacker. He wants to see all open TCP/IP and UDP ports of his computer. Nathan uses the netstat command for this purpose but he is still unable to map open ports to the running process with PID, process name, and path. Which of the following commands will Nathan use to accomplish the task?
You are the Network Administrator and your company has recently implemented encryption for all emails. You want to check to make sure that the email packages are being encrypted. What tool would you use to accomplish this?
Adam works as a professional Computer Hacking Forensic Investigator. A project has been assigned to him to investigate the main server of SecureEnet Inc. The server runs on Debian Linux operating system. Adam wants to investigate and review the GRUB configuration file of the server system.
Which of the following files will Adam investigate to accomplish the task?
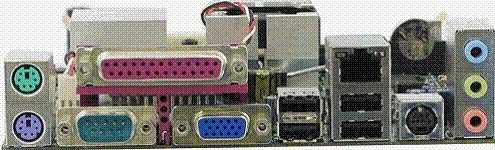
HOTSPOT -
Identify the port in the image given below, which can be connected to the hub to extend the number of ports, and up to 127 devices can be connected to it?
Hot Area:
Which of the following type of file systems is not supported by Linux kernel?
You work as a Network Administrator for Blue Bell Inc. You want to install Windows XP Professional on your computer, which already has Windows Me installed.
You want to configure your computer to dual boot between Windows Me and Windows XP Professional. You have a single 40GB hard disk.
Which of the following file systems will you choose to dual-boot between the two operating systems?
Mark works as a security manager for SofTech Inc. He is using a technique for monitoring what the employees are doing with corporate resources. Which of the following techniques is being used by Mark to gather evidence of an ongoing computer crime if a member of the staff is e-mailing company's secrets to an opponent?
Which of the following attacks saturates network resources and disrupts services to a specific computer?
Peter works as a Technical Representative in a CSIRT for SecureEnet Inc. His team is called to investigate the computer of an employee, who is suspected for classified data theft. Suspect's computer runs on Windows operating system. Peter wants to collect data and evidences for further analysis. He knows that in
Windows operating system, the data is searched in pre-defined steps for proper and efficient analysis. Which of the following is the correct order for searching data on a Windows based system?