Loading provider exams...
Sign Up & unlock 100% of Exam Questions
No Strings Attached!
Updated
What are three key routing principles of SD-WAN? (Choose three.)
This exam has 35 community-verified practice questions. Create a free account to access all questions, comments, and explanations.
Refer to the exhibit.
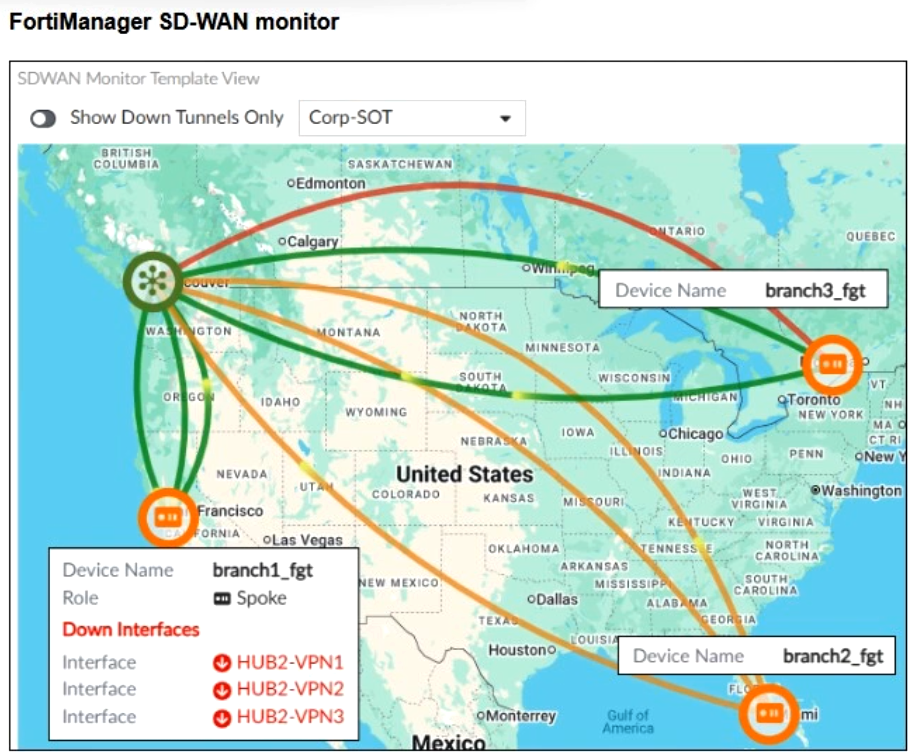
To check the status of an SD-WAN topology using the FortiManager SD-WAN monitor menus, you place your mouse next to branch1_fgt and receive the output shown in the exhibit.
Which conclusion can you draw from the output shown in the exhibit?
Refer to the exhibit.
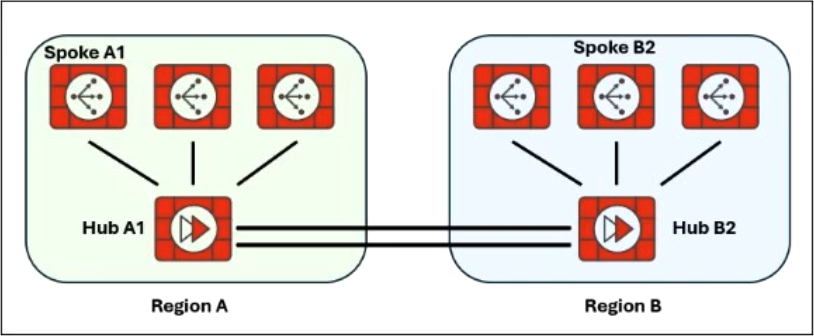
Two hub-and-spoke groups are connected through redundant site-to-site IPsec VPNs between Hub 1 and Hub 2.
Which two configuration settings are required for spoke A1 to establish an auto-discovery VPN (ADVPN) shortcut with spoke B2? (Choose two.)
In the context of SD-WAN, the terms underlay and overlay are commonly used to categorize links.
Which two statements about underlay and overlay links are correct? (Choose two.)
Refer to the exhibit.
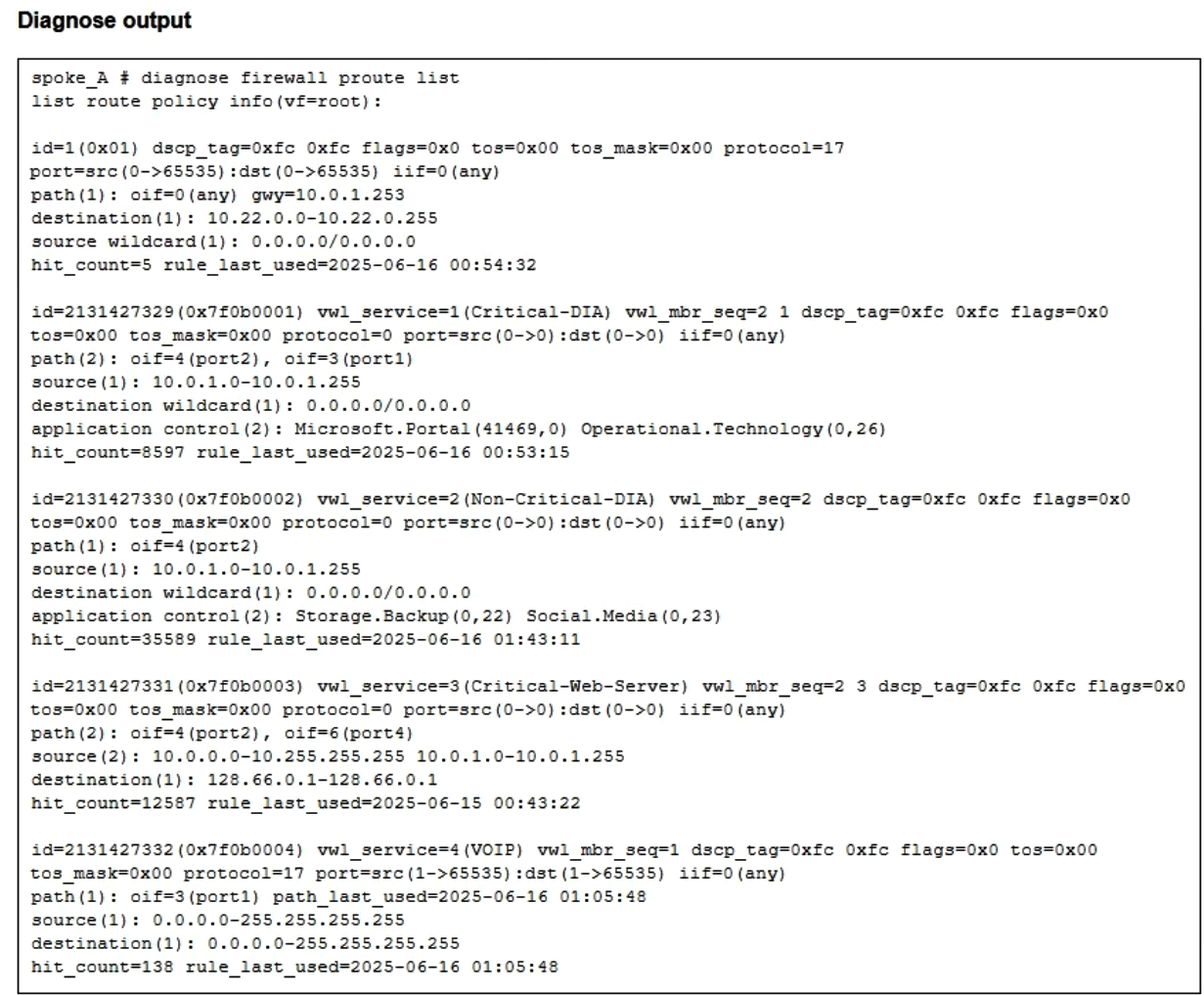
Which two conclusions can you draw from the output shown? (Choose two.)
Want a break from the ads?
Become a Supporter and enjoy a completely ad-free experience, plus unlock Learn Mode, Exam Mode, AstroTutor AI, and more.
You are configuring SD-WAN to load balance network traffic and you want to take into account the link quality.
Which two facts should you consider? (Choose two.)
You configure the overlay tunnels for an SD-WAN hub-and-spoke topology defined with IPsec tunnels, BGP on loopback and dynamic BGP.
Which are two recommended IPsec settings for this topology? (Choose two.)
An SD-WAN member is no longer used to steer SD-WAN traffic. The administrator updated the SD-WAN configuration and deleted the unused member. After the configuration update, users report that some destinations are unreachable. You confirm that the affected flow does not match an SD-WAN rule.
What could be a possible cause of the traffic interruption?
Refer to the exhibits.
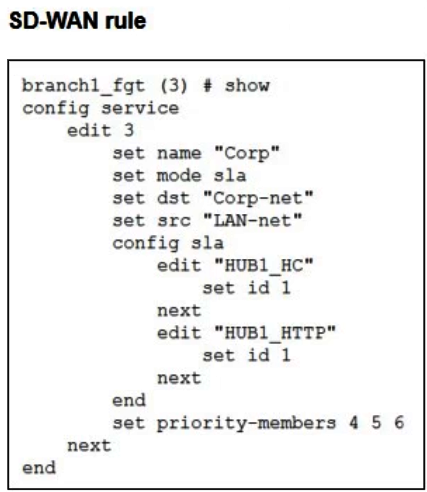
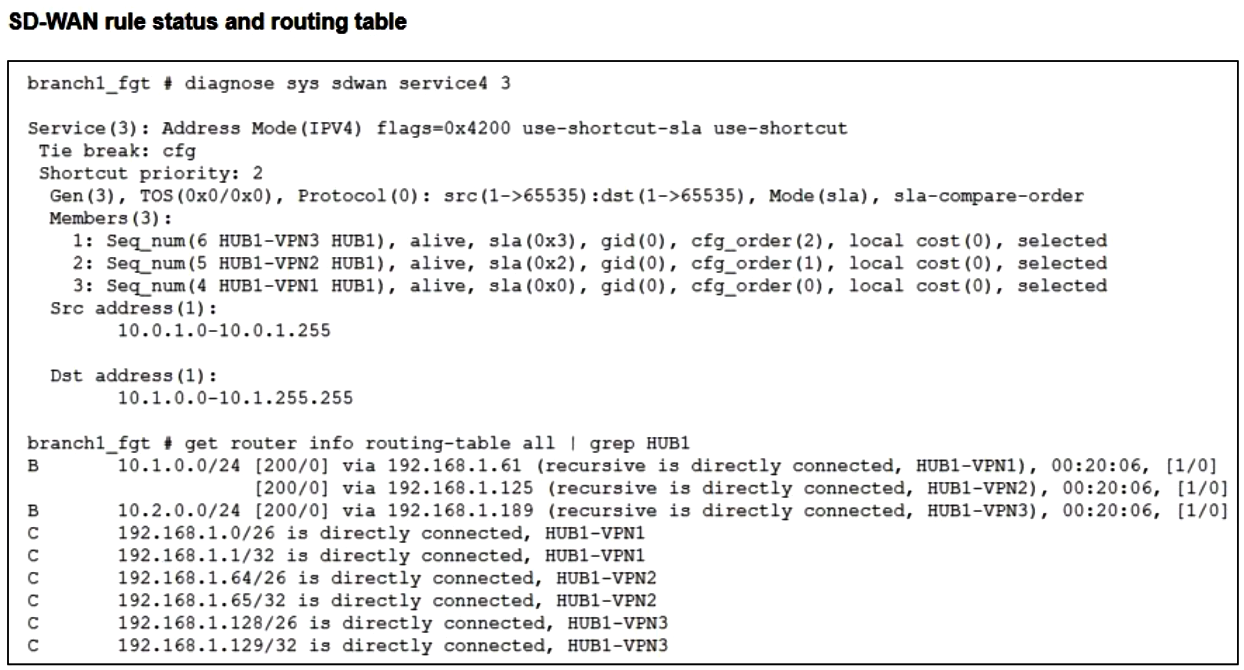
The configuration of an SD-WAN rule and the corresponding rule status and routing table are shown.
You want to understand the expected behavior for traffic that matches the SD-WAN rule, at the time the output was collected.
Based on the exhibits, which behavior can you expect for traffic that matches the SD-WAN rule?
Refer to the exhibits.
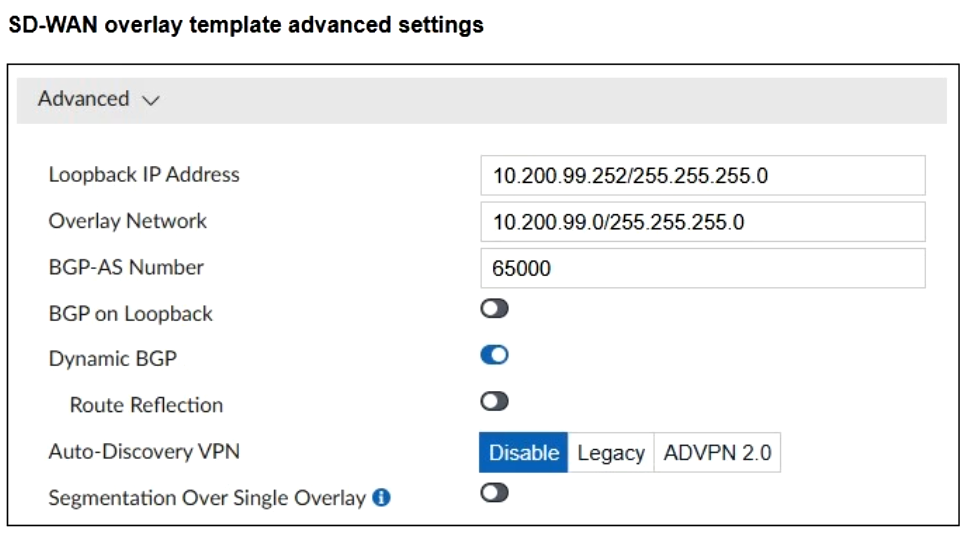
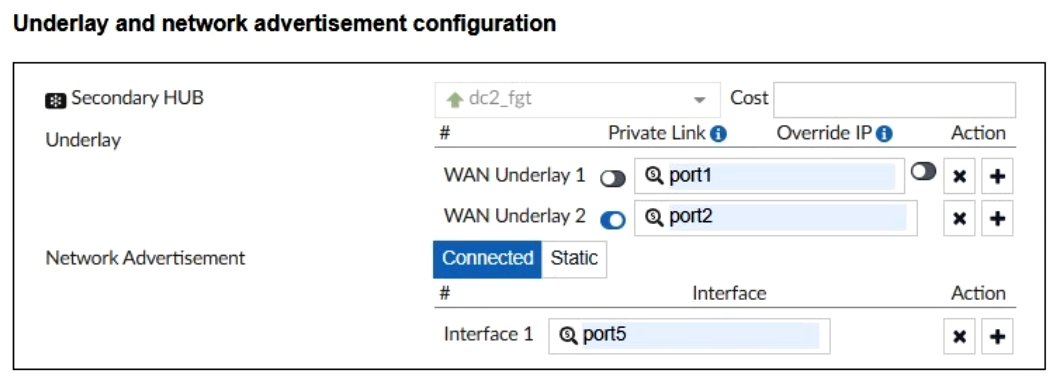
The SD-WAN overlay template, advanced settings, and the underlay and network advertisement settings are shown.
These are the configurations for the secondary hub of a dual-hub SD-WAN topology created with the FortiManager SD-WAN overlay orchestrator.
Which two conclusions can you draw from the information shown in the exhibits? (Choose two.)
You manage an SD-WAN topology and you will soon deploy 50 new branches.
Which two tasks can you do in advance to simplify this deployment? (Choose two.)
Refer to the exhibit.
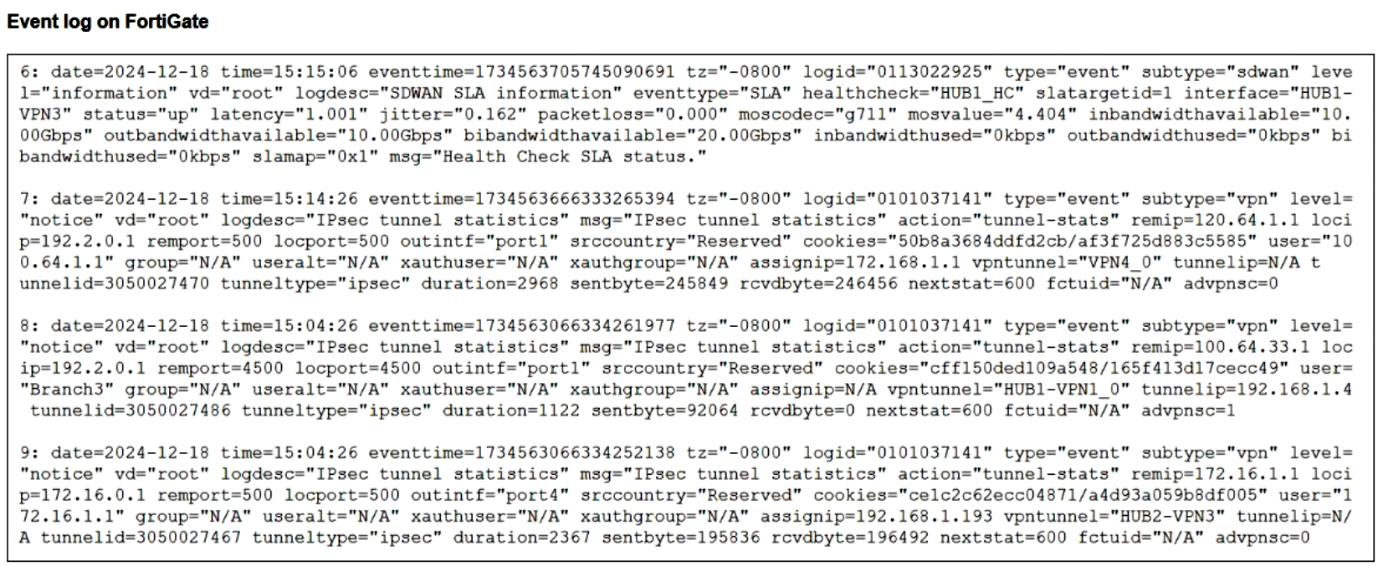
The event log on a FortiGate device is shown.
Based on the output shown in the exhibit, what can you conclude about the tunnels on this device?
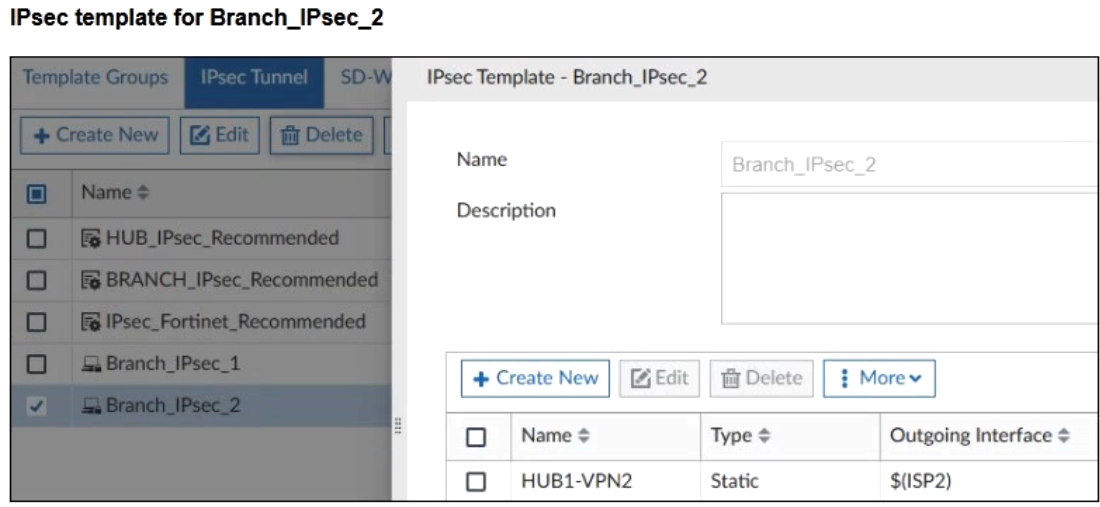
Refer to the exhibits.
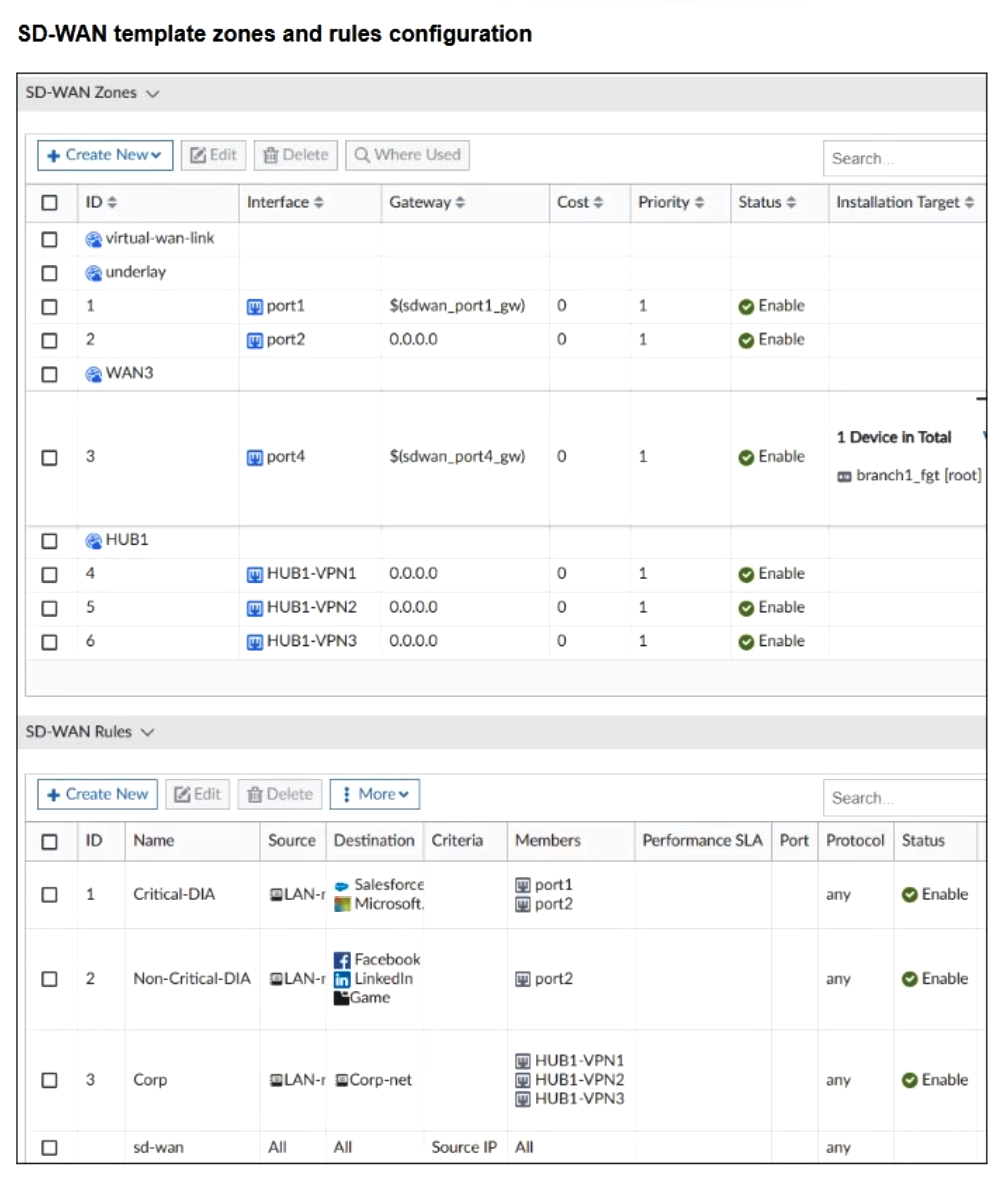
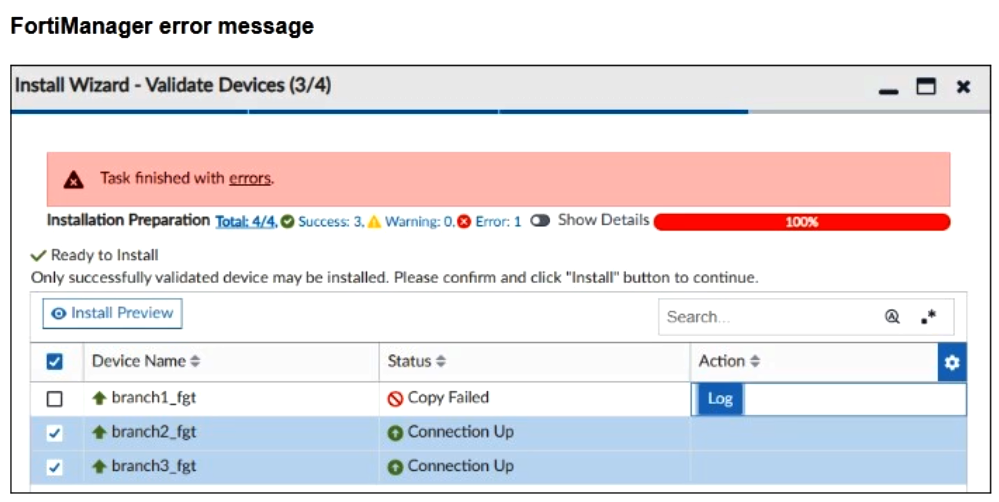
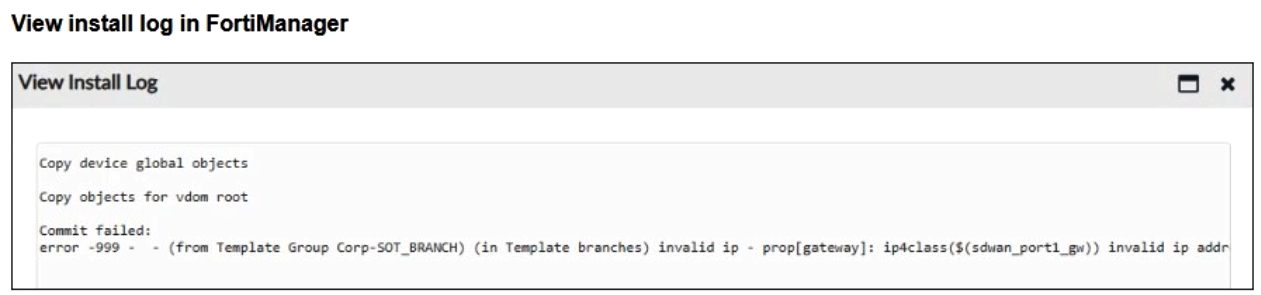
You use FortiManager to configure SD-WAN on three branch devices.
When you install the device settings, FortiManager prompts you with the error “Copy Failed” for the device branch1_fgt. When you click Log, FortiManager displays the message shown in the exhibit.
Based on the exhibits, which statement best describes the root cause of the issue?
Refer to the exhibits.
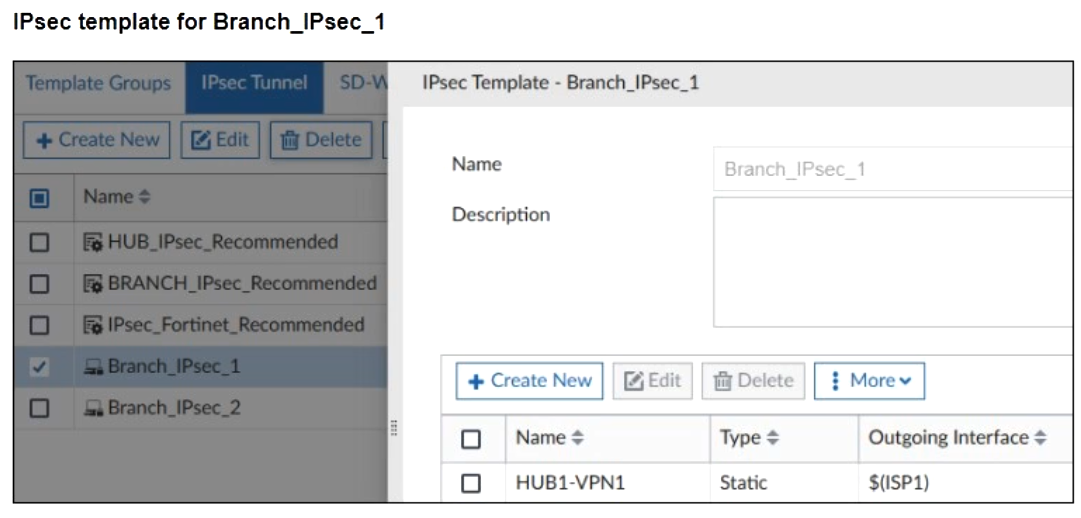
Two IPsec templates to define Branch_IPsec_1 and Branch_IPsec_2 are shown.
Each template defines a VPN tunnel. When the administrator tried to assign the second template to the FortiGate device, the FortiManager displayed the below error message:
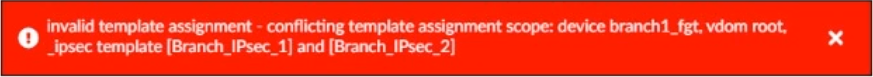
Which statement best describes the cause of the issue?