Loading provider exams...
Sign Up & unlock 100% of Exam Questions
No Strings Attached!
Updated
A FortiMail device is configured with the protected domain example.com.
If none of the senders is authenticated, which two envelope addresses will require an access receive rule? (Choose two.)
This exam has 30 community-verified practice questions. Create a free account to access all questions, comments, and explanations.
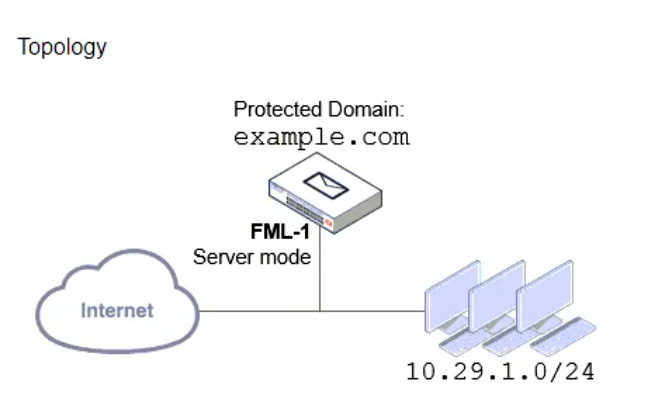
Refer to the exhibit, which shows a topology diagram of two separate email domains.
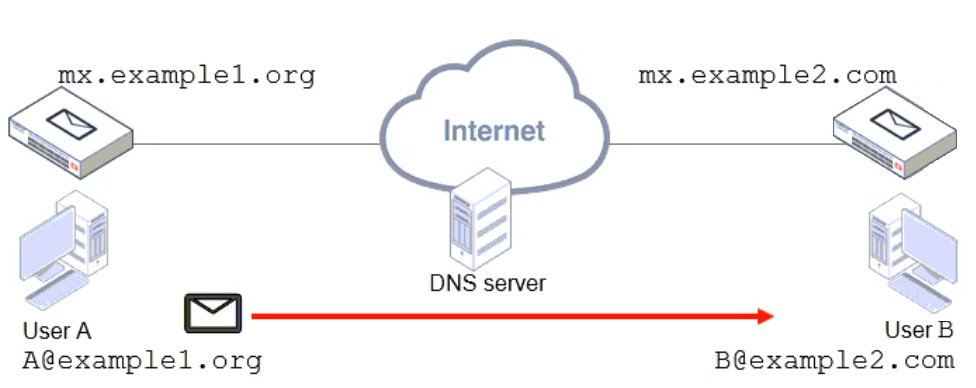
Which two statements correctly describe how an email message is delivered from User A to User B? (Choose two.)
Which two features are available when you enable HA centralized monitoring on FortiMail? (Choose two.)
Refer to the exhibit which shows the output of an email transmission using a telnet session.
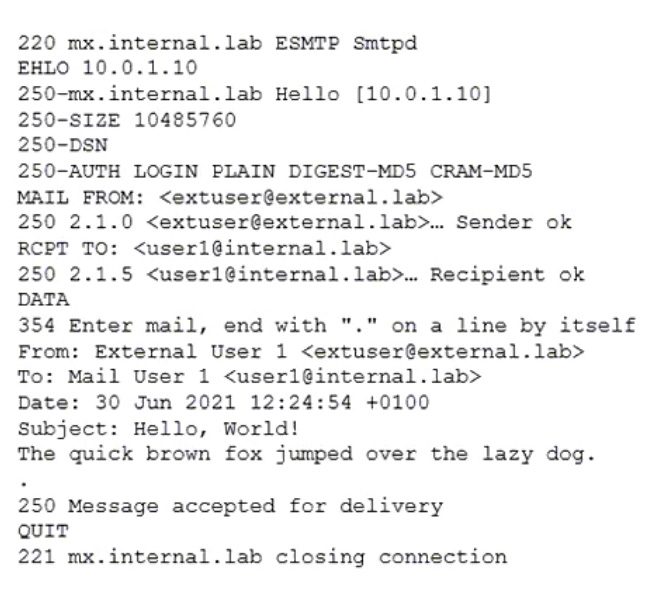
What are two correct observations about this SMTP session? (Choose two.)
A FortiMail administrator is concerned about cyber criminals attempting to get sensitive information from employees using whaling phishing attacks. What option can the administrator configure to prevent these types of attacks?
Refer to the exhibits showing SMTP limits (Session Profile — SMTP Limits), and domain settings (Domain Settings, and Domain Settings — Other) of a FortiMail device.
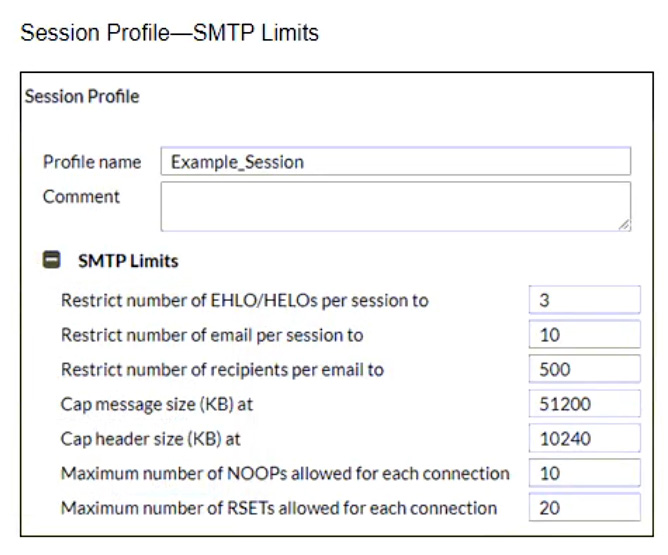
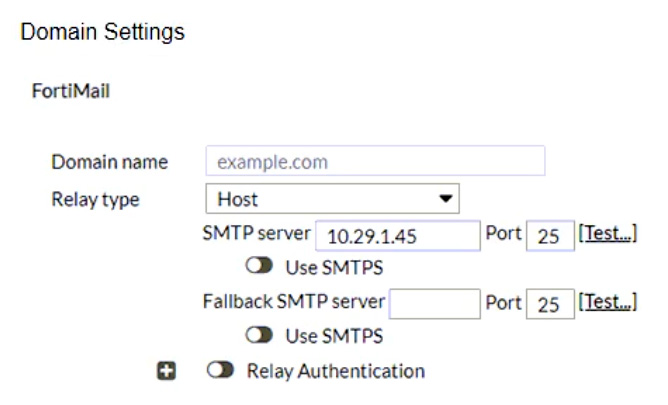
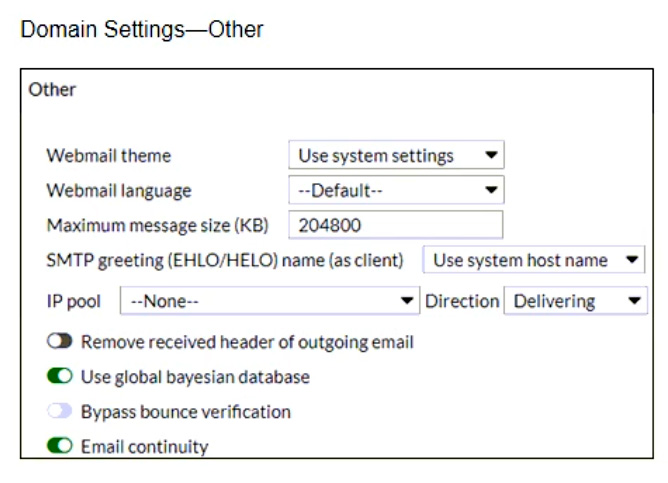
Which message size limit in KB will the FortiMail apply to outbound email?
Refer to the exhibit which shows a command prompt output of a telnet command.
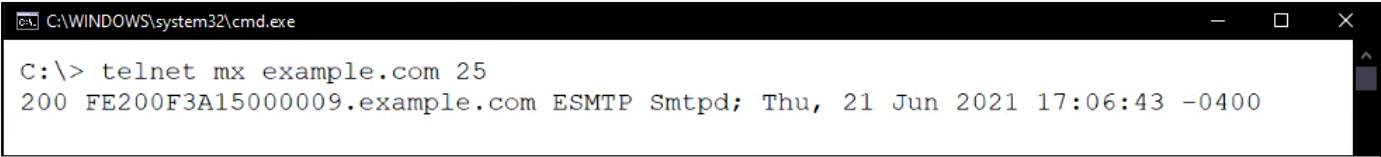
Which configuration change must you make to prevent the banner from displaying the FortiMail serial number?
Refer to the exhibits which shows a DLP scan profile configuration (DLP Scan Rule 1 and DLP Scan Rule 2) from a FortiMail device.
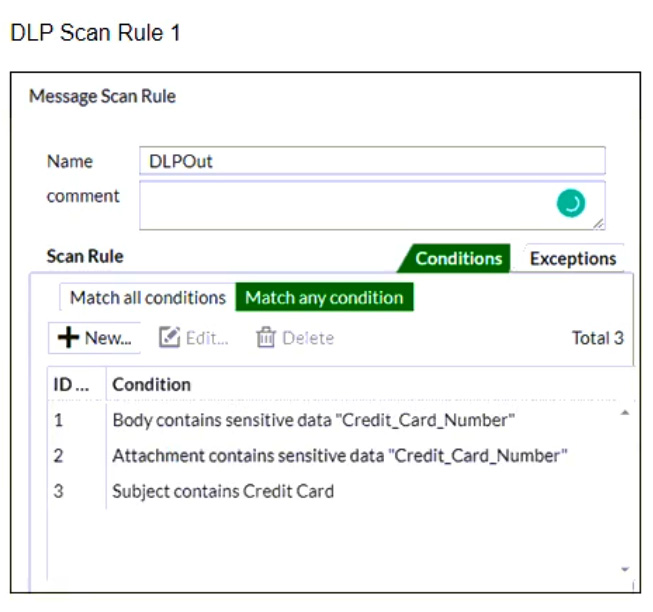
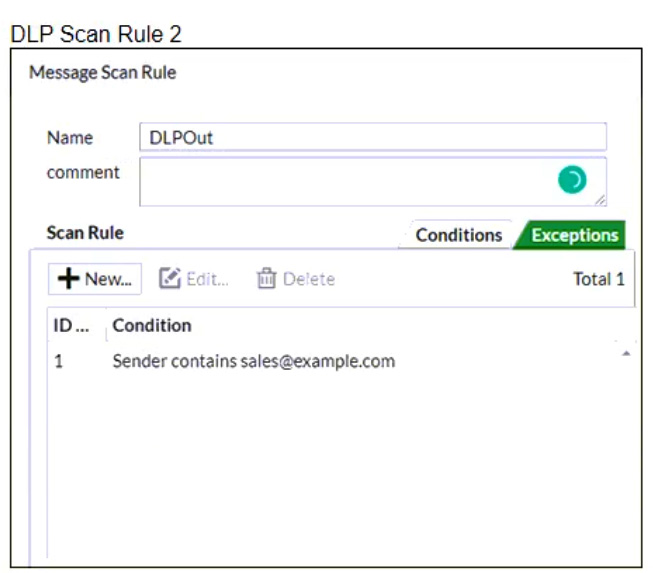
Which two message types will trigger this DLP scan rule? (Choose two.)
Refer to the exhibit which displays a topology diagram.
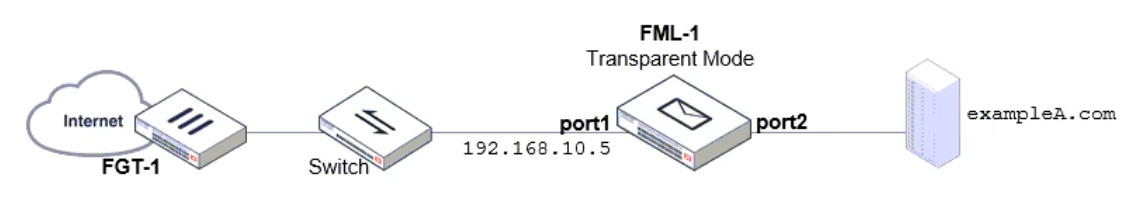
Which two statements describe the built-in bridge functionality on a transparent mode FortiMail? (Choose two.)
Refer to the exhibit which displays the domain configuration of a transparent mode FortiMail device.
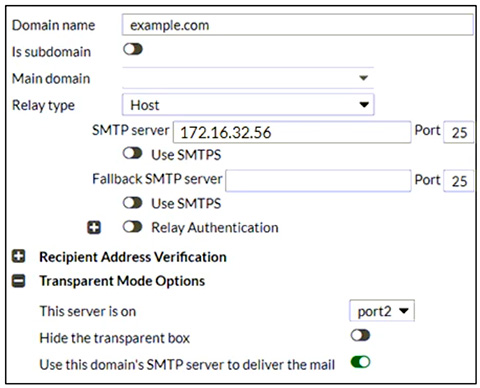
Based on the exhibit, which two sessions are considered incoming sessions? (Choose two.)
Refer to the exhibits which show a topology diagram (Topology), and a configuration element (Access Control Rule).
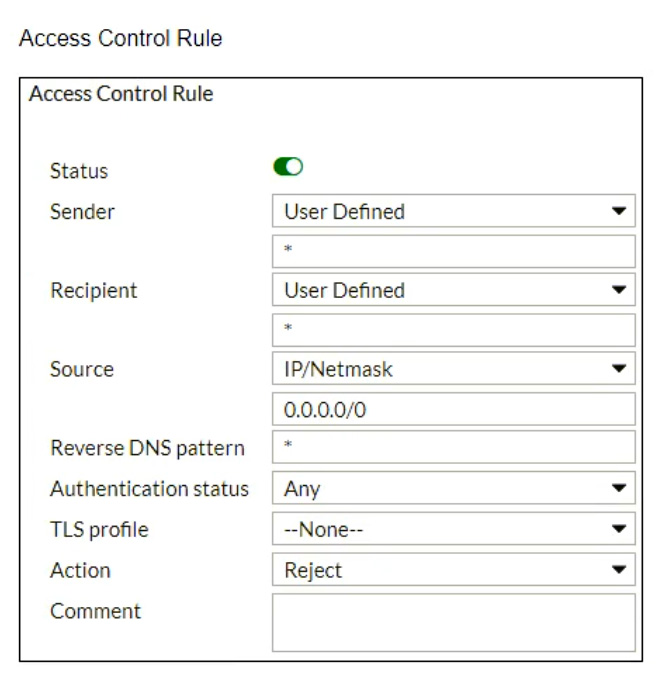
An administrator must enforce authentication on FML-1 for all outbound email from the example.com domain.
Which two settings should be used to configure the access receive rule? (Choose two.)
In which two places can the maximum email size be overridden on FortiMail? (Choose two.)