Loading questions...
Updated
What is the limitation of using a URL list and application control on the same firewall policy, in NGFW policy-based mode?
Refer to the exhibit.
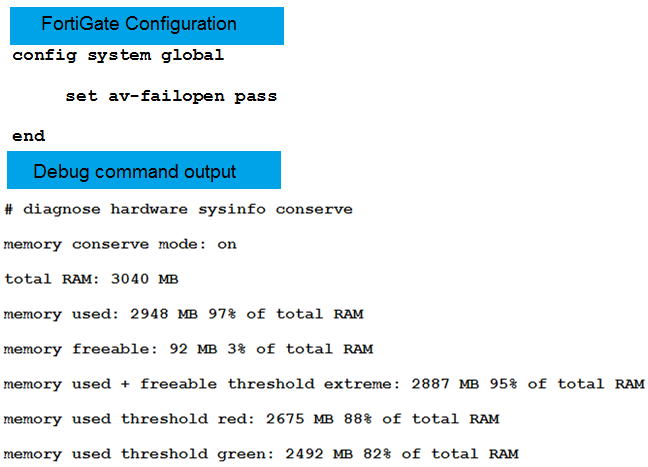
The exhibit shows FortiGate configuration and the output of the debug command.
Based on the diagnostic output, how is the FortiGate handling the traffic for new sessions that require proxy based inspection?
Refer to the exhibits.
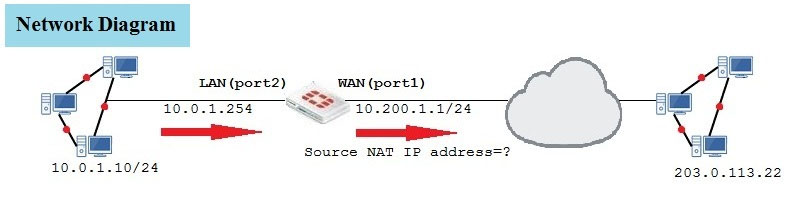
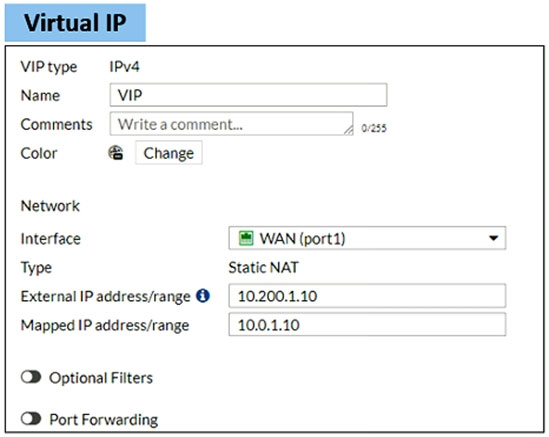
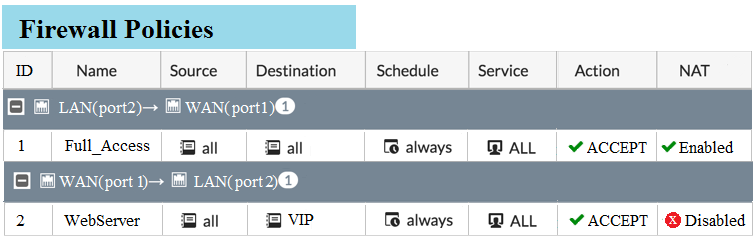
The exhibits contain a network diagram and virtual IP and firewall policy configuration.
The WAN (port1) interface has the IP address 10.200.1.1/24. The LAN (port2) interface has the IP address 10.0.1.254/24.
The first firewall policy has NAT enabled on the outgoing interface address. The second firewall policy is configured with a VIP as the destination address.
Which IP address will be used to source NAT the Internet traffic coming from a workstation with the IP address 10.0.1.10/32?
Want a break from the ads?
Become a Supporter and enjoy a completely ad-free experience, plus unlock Learn Mode, Exam Mode, AstroTutor AI, and more.
During the digital verification process, comparing the original and fresh hash results satisfies which security requirement?
Refer to the exhibits.
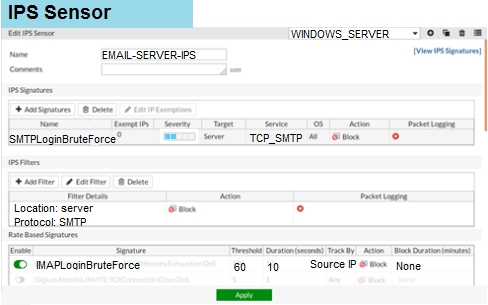
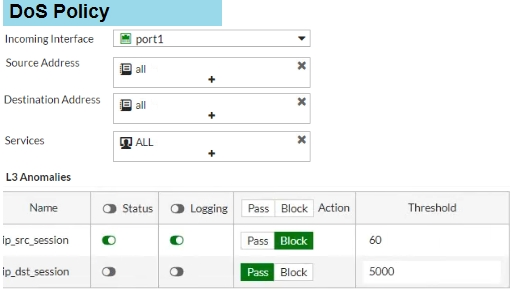
The exhibits show the IPS sensor and DoS policy configuration.
When detecting attacks, which anomaly, signature, or filter will FortiGate evaluate first?
Examine the FortiGate configuration:
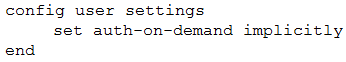
What will happen to unauthenticated users when an active authentication policy is followed by a fall through policy without authentication?
NGFW mode allows policy-based configuration for most inspection rules.
Which security profile configuration does not change when you enable policy-based inspection?
How do you format the FortiGate flash disk?
Which certificate value can FortiGate use to determine the relationship between the issuer and the certificate?
Refer to the exhibit.
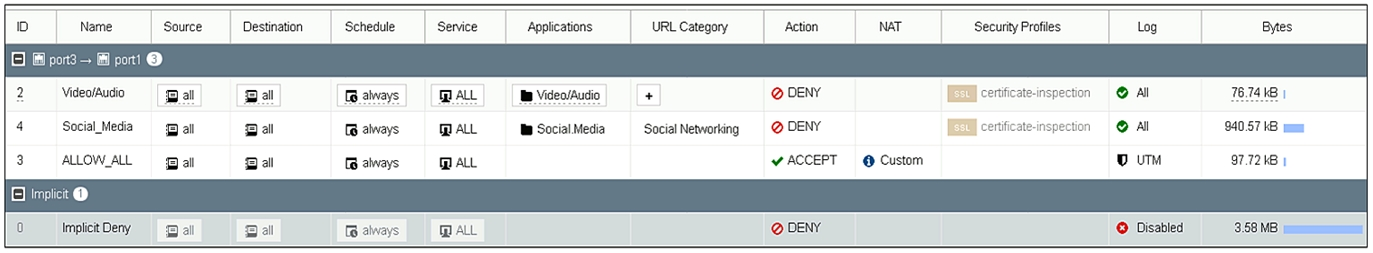
Based on the firewall configuration shown in the exhibit, which two statements about application control behavior are true? (Choose two.)
Which two statements correctly describe how FortiGate performs route lookup, when searching for a suitable gateway? (Choose two.)
Support Examcademy
Your support keeps this platform running. Become a Supporter to remove all ads and unlock exclusive study tools.
Which two statements about central NAT are true? (Choose two.)
Which two statements describe WMI polling mode for the FSSO collector agent? (Choose two.)
To complete the final step of a Security Fabric configuration, an administrator must authorize all the devices on which device?
Refer to the exhibit.
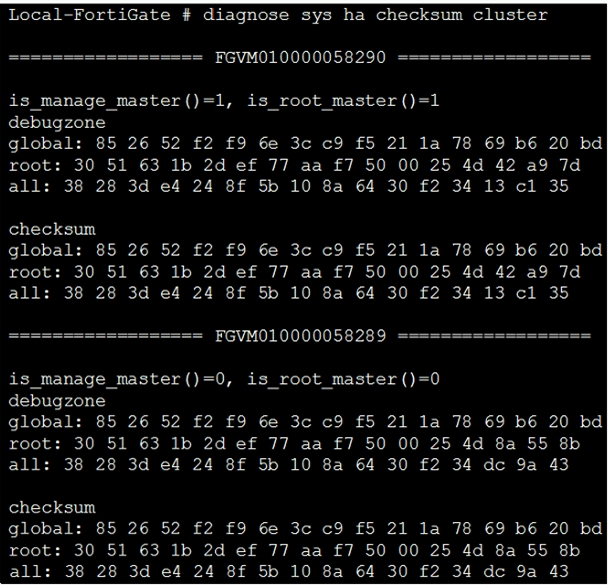
Given the output of the # diagnose sys ha checksum cluster command shown in the exhibit, which two statements are correct? (Choose two.)
The FSSO collector agent set to advanced access mode for the Windows Active Directory uses which convention?
Which two conditions are required for establishing an IPsec VPN between two FortiGate devices? (Choose two.)
An administrator has configured central DNAT and virtual IPs.
Which object can be selected in the firewall policy Destination field?
An administrator wants to throttle the total volume of SMTP sessions to their email server.
Which DoS sensor can the administrator use to achieve this?
Study without distractions
Supporters get zero ads, spaced-repetition Learn Mode, timed Exam Mode, and AI-powered explanations from AstroTutor.
What is required to create an inter-VDOM link between two VDOMs?
When browsing to an internal web server using a web-mode SSL VPN bookmark, which IP address is used as the source of the HTTP request?
When override is enabled, which option shows the process and selection criteria that is used to elect the primary FortiGate in an HA cluster?
Create a free account to unlock all questions for this exam.
Log In / Sign UpWhich two static routes are not maintained in the routing table? (Choose two.)
Which two actions are valid for a FortiGuard category-based filter, in a web filter profile, for a firewall policy in proxy-based inspection mode? (Choose two.)