Loading questions...
Updated
Want a break from the ads?
Become a Supporter and enjoy a completely ad-free experience, plus unlock Learn Mode, Exam Mode, AstroTutor AI, and more.
Create a free account to unlock all questions for this exam.
Log In / Sign UpWhich three end user logs does FortiAnalyzer use to identify possible IOC compromised hosts? (Choose three.)
Refer to the exhibit.
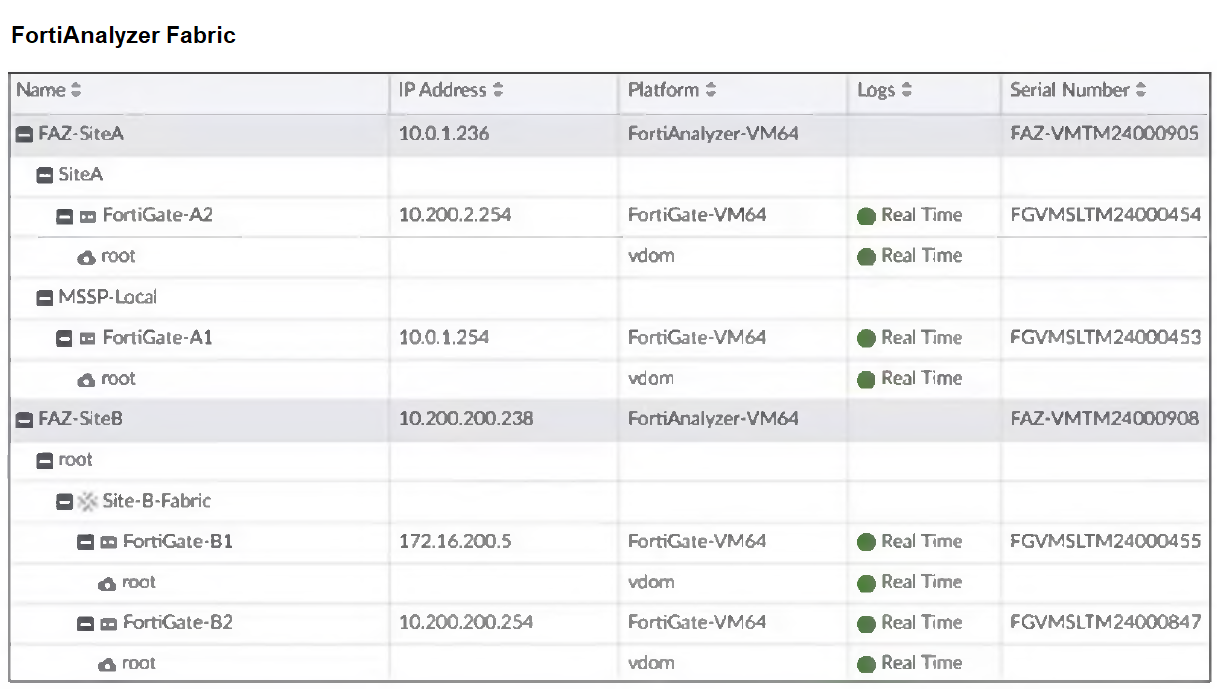
Assume that all devices in the FortiAnalyzer Fabric are shown in the image.
Which two statements about the FortiAnalyzer Fabric deployment are true? (Choose two.)
Which two statements about the FortiAnalyzer Fabric topology are true? (Choose two.)
Which two ways can you create an incident on FortiAnalyzer? (Choose two.)
According to the National Institute of Standards and Technology (NIST) cybersecurity framework, incident handling activities can be divided into phases.
In which incident handling phase do you quarantine a compromised host in order to prevent an adversary from using it as a stepping stone to the next phase of an attack?
Refer to the exhibit.
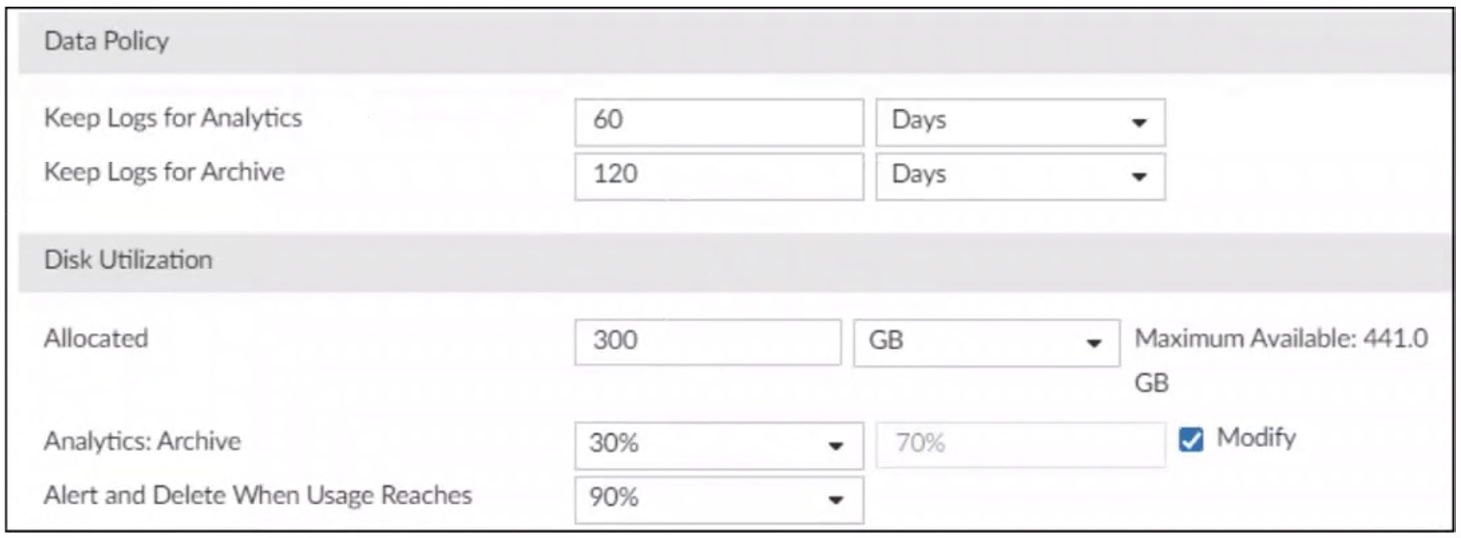
You are tasked with reviewing a new FortiAnalyzer deployment in a network with multiple registered logging devices. There is only one FortiAnalyzer in the topology.
Which potential problem do you observe?