Loading questions...
Updated
Want a break from the ads?
Become a Supporter and enjoy a completely ad-free experience, plus unlock Learn Mode, Exam Mode, AstroTutor AI, and more.
Support Examcademy
Your support keeps this platform running. Become a Supporter to remove all ads and unlock exclusive study tools.
Create a free account to unlock all questions for this exam.
Log In / Sign UpRefer to the exhibits, which show the system performance output and the default configuration of high memory usage thresholds in a FortiGate.
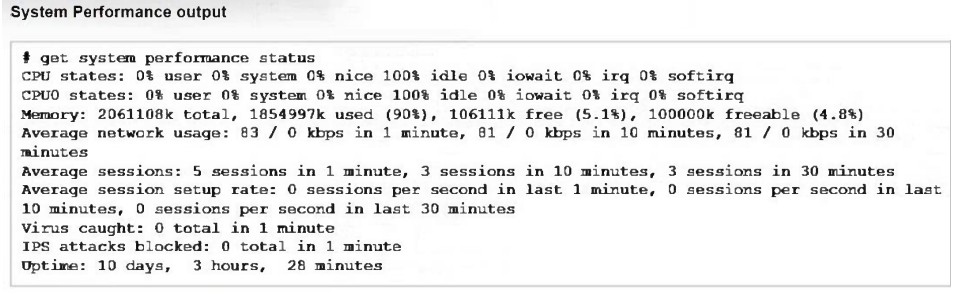
Based on the system performance output, what can be the two possible outcomes? (Choose two.)
What is the primary FortiGate election process when the HA override setting is disabled?
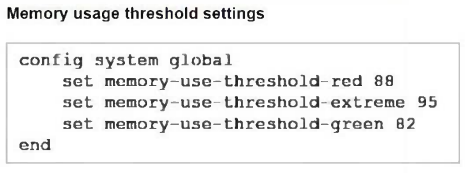
Refer to the exhibit.
Which two statements are true about the routing entries in this database table? (Choose two.)
Which three methods are used by the collector agent for AD polling? (Choose three.)
Which method allows management access to the FortiGate CLI without network connectivity?
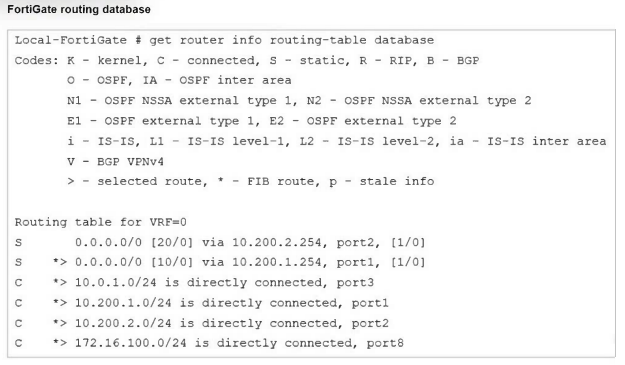
Refer to the exhibit.
In the network shown in the exhibit, the web client cannot connect to the HTTP web server. The administrator runs the FortiGate built-in sniffer and gets the output shown in the exhibit.
What should the administrator do next, to troubleshoot the problem?
Refer to the exhibits.
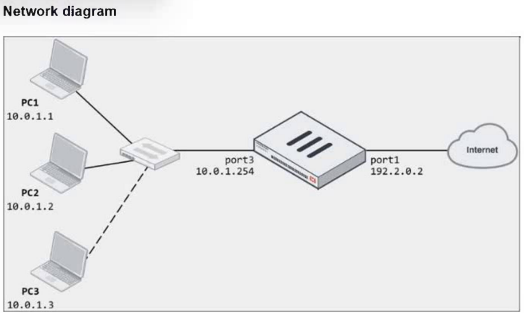
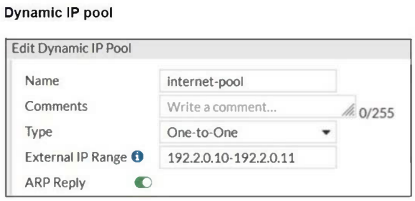
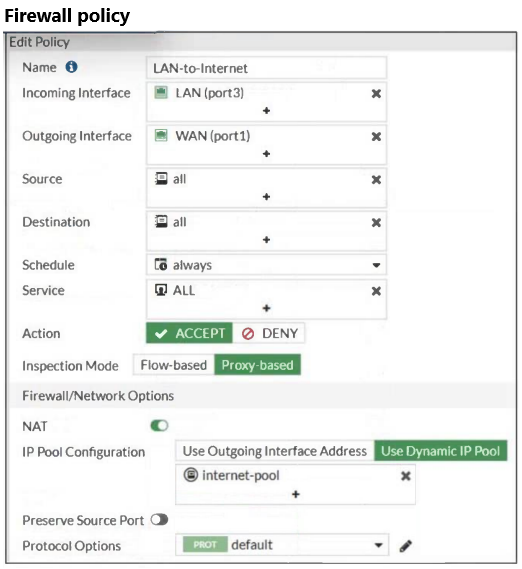
The exhibits show a diagram of a FortiGate device connected to the network, as well as the firewall policy and IP pool configuration on the FortiGate device.
Two PCs, PC1 and PC2, are connected behind FortiGate and can access the internet successfully. However, when the administrator adds a third PC to the network (PC3), the PC cannot connect to the internet.
Based on the information shown in the exhibit, which two configuration options can the administrator use to fix the connectivity issue for PC3? (Choose two.)
Refer to the exhibits.
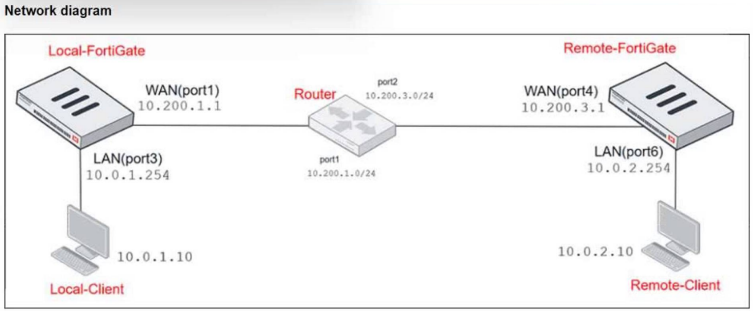
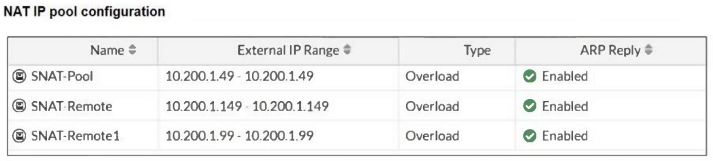

The exhibits show a diagram of a FortiGate device connected to the network, as well as the IP pool configuration and firewall policy objects.
The WAN (port1) interface has the IP address 10.200.1.1/24. The LAN (port3) interface has the IPaddress 10.0.1.254/24.
Which IP address will be used to source NAT (SNAT) the traffic, if the user on Local-Client (10.0.1.10) pings the IP address of Remote-FortiGate (10.200.3.1)?
Refer to the exhibit.
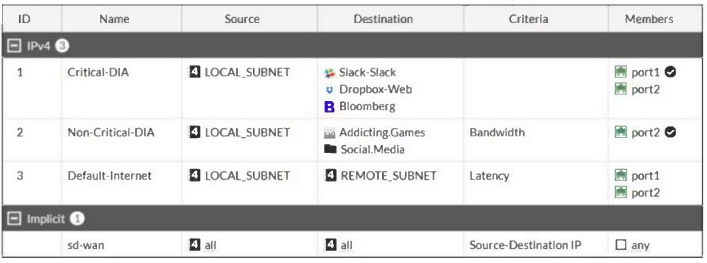
Which algorithm does SD-WAN use to distribute traffic that does not match any of the SD-WAN rules?
Which three pieces of information does FortiGate use to identify the hostname of the SSL server when SSL certificate inspection is enabled? (Choose three.)
A network administrator is configuring an IPsec VPN tunnel for a sales employee travelling abroad.
Which IPsec Wizard template must the administrator apply?
When FortiGate performs SSL/SSH full inspection, you can decide how it should react when it detects an invalid certificate.
Which three actions are valid actions that FortiGate can perform when it detects an invalid certificate? (Choose three.)
Refer to the exhibit.

The exhibit shows the FortiGuard Category Based Filter section of a corporate web filter profile.
An administrator must block access to download.com, which belongs to the Freeware and Software Downloads category. The administrator must also allow other websites in the same category.
What are two solutions for satisfying the requirement? (Choose two.)
Which three strategies are valid SD-WAN rule strategies for member selection? (Choose three.)
Which two statements are true regarding FortiGate HA configuration synchronization? (Choose two.)
Which inspection mode does FortiGate use for application profiles if it is configured as a profile-based next-generation firewall (NGFW)?
FortiGate is integrated with FortiAnalyzer and FortiManager.
When a firewall policy is created, which attribute is added to the policy to improve functionality and to support recording logs to FortiAnalyzer or FortiManager?
An administrator manages a FortiGate model that supports NTurbo.
How does NTurbo enhance performance for flow-based inspection?