Loading provider exams...
Sign Up & unlock 100% of Exam Questions
No Strings Attached!
Updated
As an organization grows, more people have to login onto the BIG-IP. Instead of adding more local users, a BIG-IP Administrator is asked to configure remote authentication against a central authentication server.
Which two types of remote server can be used here? (Choose two.)
This exam has 30 community-verified practice questions. Create a free account to access all questions, comments, and explanations.
Log In / Sign UpA BIG-IP Administrator uses a device group to share the workload and needs to perform service on a BIG-IP device currently active for a traffic group. The administrator needs to enable the traffic group to run on another BIG-IP device in the device group.
What should the administrator do to meet the requirement?
Which TMSH command initiates a manual configuration synchronization to the specified device group?
In the BIG-IP Configuration Utility, where can the BIG-IP Administrator check system metrics such as CPU and memory usage?
The BIG-IP system is provisioned for LTM only. The BIG-IP Administrator is tasked with provisioning ASM.
What process restarts when the BIG-IP Administrator changes the module provisioning?
In which of the following log files would log events pertaining to Pool-members being marked "UP" or "DOWN" by their Health Monitors be written?
Which log file should the BIG-IP Administrator check to determine if a specific user tried to log in to the BIG-IP Configuration Utility?
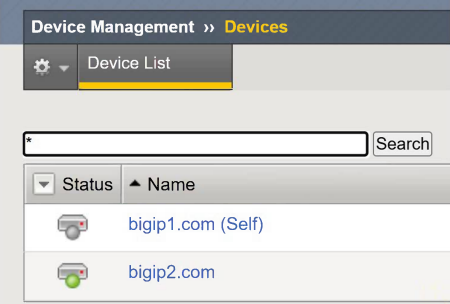
What is the status of bigip1.com?
A local user account (User1) on the BIG-IP device is assigned the User Manager role. User1 attempts to modify the properties of another account (User2), but the action fails. The BIG-IP Administrator can successfully modify the User2 account.
Assuming the principle of least privilege, what is the correct way to allow User1 to modify User2 properties?
Which command will provide the BIG-IP Administrator with the current device HA status?
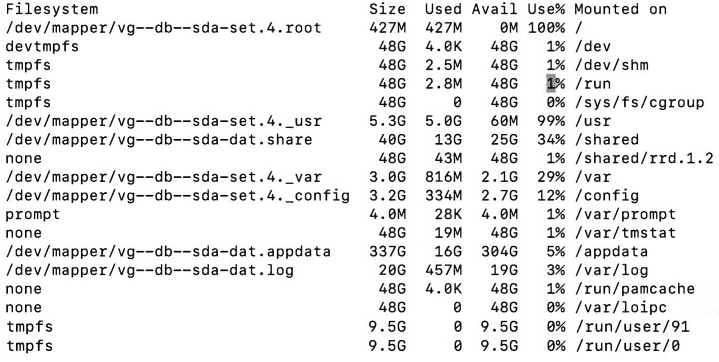
The BIG-IP Administrator is investigating disk utilization on the BIG-IP device.
What should the BIG-IP Administrator check next?
The BIG-IP Administrator suspects unauthorized SSH login attempts on the BIG-IP system.
Which log file would contain details of these attempts?