Loading provider exams...
Sign Up & unlock 100% of Exam Questions
No Strings Attached!
Updated
Which of the following is an intentional act of sending multiple copies of the identical content to the same recipient?
This exam has 50 community-verified practice questions. Create a free account to access all questions, comments, and explanations.
VPN technology is structured on the basis of tunneling. It requires the setting up and upholding of a logical network connection. The packets built in a particular VPN protocol design are put in a nutshell inside another base or carrier protocol. They are then transmitted between the VPN client and the server and deencapsulated finally on the receiving side. Which of the following statements best describes the function of voluntary tunneling?
A security strategy in which several protection layers are placed throughout an information system helps to prevent direct attacks against an information system and data because a break in one layer only leads the attacker to the next layer. What is this security strategy called?
Which of the following attack allows attackers to bypass client-ID security mechanisms and gain access privileges, and then inject malicious scripts into specific web pages?
The security of the network can be increased in a number of ways, for instance, by installing a special kind of web server and through packet filtering. What type of server is implemented as an intermediary server between a client and a server to act as a shield and protect and hide the computer from the outside network?
Want a break from the ads?
Become a Supporter and enjoy a completely ad-free experience, plus unlock Learn Mode, Exam Mode, AstroTutor AI, and more.
An algorithm which is a part of the U.S. government's long-term project to develop a set of standards for publicly available cryptography as authorized by the Computer Security Act of 1987 accepts a message of 264 bits in length and a 160-bit message output digest is produced to complicate text searching. Which of the following algorithms is a family of two similar hash functions, with different block sizes, and uses 32-bit words and 64-bit words?
Kelly is taking backups of the organization’s data. Currently, he is taking backups of only those files which are created or modified after the last backup. What type of backup is Kelly using?
WEP is a component of the IEEE 802.11 WLAN standards. Its primary purpose is to provide for the confidentiality of data on wireless networks at a level equivalent to that of the wired LANs. In a wireless LAN, the network can be accessed without physically connecting to the LAN. On what layer of the OSI model, WEP utilizes an encryption mechanism for minimizing unauthorized access on the WLAN?
A DoS attack is an incident in which a user or organization is deprived of the services of a resource they would normally expect to have. At the data link layer, DoS attacks can be done easily. DoS attacks at the application and transport layers are primarily the same, but the interaction between the network, data-link, and physical layers which increase the risk of a DoS attack on a wireless network is different. An attacker can create a device that will saturate the 802.11 frequency bands with noise. If the attacker can create enough RF noise to reduce the signal-to-noise ratio to an unusable level, then the devices within the range of the noise will be effectively taken offline to block the communication. What type of DoS attack is being discussed here?
Timothy works as a network administrator in a multinational organization. He decides to implement a dedicated network for sharing storage resources. He uses a _______ as it separates the storage units from the servers and the user network.
Firewall protection is provided by different types of firewalls. One of the firewall types works at the session layer of the OSI model, or the TCP layer of TCP/IP, and monitors TCP handshaking between packets to determine whether a requested session is legitimate. This level hides information about the private networks they protect, but they do not filter individual packets. Identify the type of firewall described above.
Which of the following contains extra material that is referred to in the report?
ARP is Address Resolution Protocol which is used to map network layer IP addresses to data link layer MAC addresses.
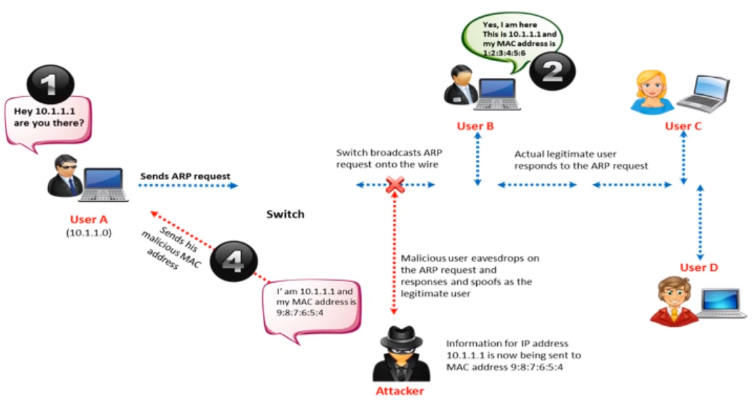
Using the diagram above, choose the appropriate option that justifies ARP spoofing:
Which of the following is a Linux journaling file system?
Each firm, such as a law firm or a computer forensics firm dealing with report writing has its own established report format. An investigative report format has basically four sections. Which section of investigative report format is dedicated to the background and summary?
VPNs provide a secure means of communication between hosts over an insecure medium. A VPN makes use of the Internet as the transport backbone. A VPN can be deployed in two ways, Internal LAN VPNs and Remote Access VPNs. Which of the following statements is true for a Remote Access VPN?
Blake is working on the company’s updated disaster and business continuity plan. The last section of the plan covers computer and data incidence response. Blake is outlining the level of severity for each type of incident in the plan. Unsuccessful scans and probes are at what severity level?
Among different types of proxy servers, which type allows the client system to connect to the server without its knowledge, making it difficult to automatically detect the FTP or HTTPs connection?
Ciphers are algorithms used to encrypt or decrypt the data. Which of the following is a 128-bit block size symmetric-key encryption standard adopted by the U.S. government and is an iterated block cipher, which works by repeating the same defined steps multiple times?
Networks are vulnerable to an attack, which occurs due to overextension of bandwidth, bottlenecks, network data interception, etc.
Which of the following network attack refers to a process in which an attacker changes his or her IP address so that he or she appears to be someone else?