Loading provider exams...
Sign Up & unlock 100% of Exam Questions
No Strings Attached!
Updated
Dale is a network admin working in Zero Faults Inc. Recently the company's network was compromised and is experiencing very unusual traffic. Dale checks for the problem that compromised the network. He performed a penetration test on the network's IDS and identified that an attacker sent spoofed packets to a broadcast address in the network.
Which of the following attacks compromised the network?
Thomas is an attacker and he skimmed through the HTML source code of an online shopping website for the presence of any vulnerabilities that he can exploit.
He already knows that when a user makes any selection of items in the online shopping webpage, the selection is typically stored as form field values and sent to the application as an HTTP request (GET or POST) after clicking the Submit button. He also knows that some fields related to the selected items are modifiable by the user (like quantity, color, etc.) and some are not (like price). While skimming through the HTML code, he identified that the price field values of the items are present in the HTML code. He modified the price field values of certain items from $200 to $2 in the HTML code and submitted the request successfully to the application.
Identify the type of attack performed by Thomas on the online shopping website?
Peter, a disgruntled ex-employee of Zapmaky Solutions Ltd., is trying to jeopardize the company's website http://zapmaky.com. He conducted the port scan of the website by using the Nmap tool to extract the information about open ports and their corresponding services. While performing the scan, he recognized that some of his requests are being blocked by the firewall deployed by the IT personnel of Zapmaky and he wants to bypass the same. For evading the firewall, he wanted to employ the stealth scanning technique which is an incomplete TCP three-way handshake method that can effectively bypass the firewall rules and logging mechanisms.
Which if the following Nmap commands should Peter execute to perform stealth scanning?
Adam is an IT administrator for Syncan Ltd. He is designated to perform various IT tasks like setting up new user accounts, managing backup/restores, security authentications and passwords, etc. Whilst performing his tasks, he was asked to employ the latest and most secure authentication protocol to encrypt the passwords of users that are stored in the Microsoft Windows OS-based systems.
Which of the following authentication protocols should Adam employ in order to achieve the objective?
The Rhythm Networks Pvt Ltd firm is a group of ethical hackers. Rhythm Networks was asked by their client Zombie to identify how the attacker penetrated their firewall. Rhythm discovered the attacker modified the addressing information of the IP packet header and the source address bits field to bypass the firewall.
What type of firewall bypassing technique was used by the attacker?
Want a break from the ads?
Become a Supporter and enjoy a completely ad-free experience, plus unlock Learn Mode, Exam Mode, AstroTutor AI, and more.
An employee is trying to access the internal website of his company. When he opened a webpage, he received an error message notifying Proxy Authentication Required. He approached the IT department in the company and reported the issue. The IT staff explained him that this is an HTTP error indicating that the server is unable to process the request due to lack of appropriate client's authentication credentials for a proxy server that is processing the requests between the clients and the server.
Identify the HTTP error code corresponding to the above error message received by the employee?
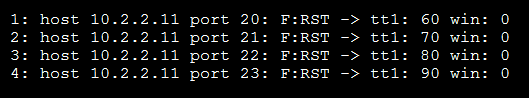
During scanning of a test network, Paul sends TCP probe packets with the ACK flag set to a remote device and then analyzes the header information (TTL and
WINDOW field) of the received RST packets to find whether the port is open or closed.
Analyze the scanning result below and identify the open port.
Irin is a newly joined penetration tester for XYZ Ltd. While joining, as a part of her training, she was instructed about various legal policies and information securities acts by her trainer. During the training, she was informed about a specific information security act related to the conducts and activities like it is illegal to perform DoS attacks on any websites or applications, it is illegal to supply and own hacking tools, it is illegal to access unauthorized computer material, etc.
To which type of information security act does the above conducts and activities best suit?
Tecty Motors Pvt. Ltd. has recently deployed RFID technology in the vehicles which allows the car owner to unlock the car with the exchange of a valid RFID signal between a reader and a tag. Jamie, on the other hand, is a hacker who decided to exploit this technology with the aim of stealing the target vehicle. To perform this attack on the target vehicle, he first used an automated tool to intercept the signals between the reader and the tag to capture a valid RFID signal and then later used the same signal to unlock and steal the victim's car.
Which of the following RFID attacks Jamie has performed in the above scenario?
James, a penetration tester, found a SQL injection vulnerability in the website http://www.xsecurity.com. He used sqlmap and extracted the website's databases from the sql server, one of them being offices. Which among the following sqlmap queries does James issue in order to extract the tables related to the database
offices?
A security analyst at Techsoft Solutions is performing penetration testing on the critical IT assets of the company. As part of this process, he is simulating the methodologies and techniques of a real attacker because he is provided with limited or zero information about the company and its assets.
Identify the type of testing performed by the security analyst?
A penetration tester at Trinity Ltd. is performing IoT device testing. As part of this process, he is checking the IoT devices for open ports using port scanners such as Nmap. After identifying the open ports, he started using automated tools to check each open port for any exploitable vulnerabilities.
Identify the IoT security issues the penetration tester is trying to uncover?
Depp Networks is a leader in providing ethical hacking services. They were tasked to examine the strength of a client network. After using a wide range of tests, they finally zeroed in on ICMP tunneling to bypass the firewall.
What factor makes ICMP tunneling appropriate to bypass the firewall?
SecGlobal Corporation hired Michael, a penetration tester. Management asked Michael to perform cloud penetration testing on the company's cloud infrastructure.
As a part of his task, he started checking all the agreements with cloud service provider and came to a conclusion that it is not possible to perform penetration testing on the cloud services that are being used by the organization due to the level of responsibilities between company and the Cloud Service Provider (CSP).
Identify the type of cloud service deployed by the organization?
Which port does DHCP use for client connections?
An attacker targeted to attack network switches of an organization to steal confidential information such as network subscriber information, passwords, etc. He started transmitting data through one switch to another by creating and sending two 802.1Q tags, one for the attacking switch and the other for victim switch. By sending these frames. The attacker is fooling the victim switch into thinking that the frame is intended for it. The target switch then forwards the frame to the victim port.
Identify the type of attack being performed by the attacker?
Michael, a Licensed Penetration Tester, wants to create an exact replica of an original website, so he can browse and spend more time analyzing it.
Which of the following tools will Michael use to perform this task?
A hacker initiates so many invalid requests to a cloud network host that the host uses all its resources responding to invalid requests and ignores the legitimate requests.
Identify the type of attack -
James is an attacker who wants to attack XYZ Inc. He has performed reconnaissance over all the publicly available resources of the company and identified the official company website http://xyz.com. He scanned all the pages of the company website to find for any potential vulnerabilities to exploit. Finally, in the user account login page of the company's website, he found a user login form which consists of several fields that accepts user inputs like username and password. He also found than any non-validated query that is requested can be directly communicated to the active directory and enable unauthorized users to obtain direct access to the databases. Since James knew an employee named Jason from XYZ Inc., he enters a valid username jason and injects jason)(&)) in the username field. In the password field, James enters blah and clicks Submit button. Since the complete URL string entered by James becomes (&(USER=jason) (&))(PASS=blah)), only the first filter is processed by the Microsoft Active Directory, that is, the query (&(USER=jason)(&)) is processed. Since this query always stands true, James successfully logs into the user account without a valid password of Jason.
In the above scenario, identify the type of attack performed by James?
Veronica, a penetration tester at a top MNC company, is trying to breach the company's database as a part of SQLi penetration testing. She began to use the
SQLi techniques to test the database security level. She inserted new database commands into the SQL statement and appended a SQL Server EXECUTE command to the vulnerable SQL statements.
Which of the following SQLi techniques was used to attack the database?
Frank is performing a wireless pen testing for an organization. Using different wireless attack techniques, he successfully cracked the WPA-PSK key. He is trying to connect to the wireless network using the WPA-PSK key. However, he is unable to connect to the WLAN as the target is using MAC filtering.
What would be the easiest way for Frank to circumvent this and connect to the WLAN?
Steven is performing a wireless network audit. As part of the engagement, he is trying to crack a WPA-PSK key. Steven has captured enough packets to run aircrack-ng and discover the key, but aircrack-ng did not yield any result, as there were no authentication packets in the capture.
Which of the following commands should Steven use to generate authentication packets?
Sam was asked to conduct penetration tests on one of the client's internal networks. As part of the testing process, Sam performed enumeration to gain information about computers belonging to a domain, list of shares on the individual hosts in the network, policies and passwords.
Identify the enumeration technique.
Jason is working on a pen testing assignment. He is sending customized ICMP packets to a host in the target network. However, the ping requests to the target failed with ICMP Time Exceeded Type = 11 error messages.
What can Jason do to overcome this error?
Joseph, a penetration tester, was hired by Xsecurity Services. Joseph was asked to perform a pen test on a client's network. He was not provided with any information about the client organization except the company name.
Identify the type of testing Joseph is going to perform for the client organization?