Loading provider exams...
Sign Up & unlock 100% of Exam Questions
No Strings Attached!
Updated
How many layers are present in the TCP/IP model?
Which of the following statements are true about a wireless network?
Each correct answer represents a complete solution. Choose all that apply.
In which of the following conditions does the system enter ROM monitor mode? Each correct answer represents a complete solution. Choose all that apply.
Which of the following types of information can be obtained through network sniffing? (Choose all that apply.)
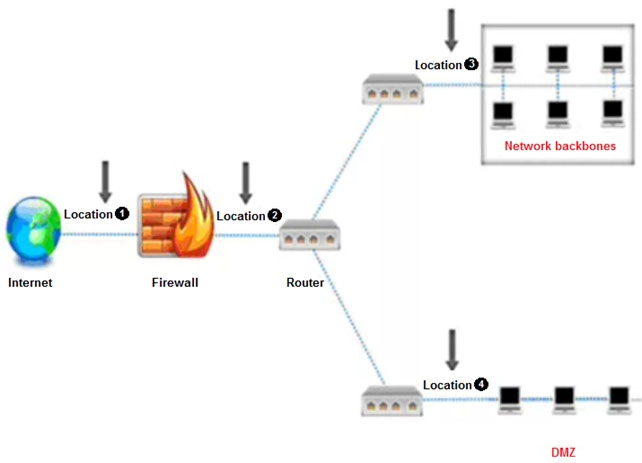
An administrator wants to monitor and inspect large amounts of traffic and detect unauthorized attempts from inside the organization, with the help of an IDS. They are not able to recognize the exact location to deploy the IDS sensor. Can you help him spot the location where the IDS sensor should be placed?
Want a break from the ads?
Become a Supporter and enjoy a completely ad-free experience, plus unlock Learn Mode, Exam Mode, AstroTutor AI, and more.
Alex is administering the firewall in the organization's network. What command will he use to check all the remote addresses and ports in numerical form?
Which of the following interfaces uses hot plugging technique to replace computer components without the need to shut down the system?
During the recovery process, RTO and RPO should be the main parameters of your disaster recovery plan. What does RPO refer to?
Assume that you are a network administrator and the company has asked you to draft an Acceptable Use Policy (AUP) for employees. Under which category of an information security policy does AUP fall into?
Management asked their network administrator to suggest an appropriate backup medium for their backup plan that best suits their organization's need. Which of the following factors will the administrator consider when deciding on the appropriate backup medium? (Choose all that apply.)
John wants to implement a firewall service that works at the session layer of the OSI model. The firewall must also have the ability to hide the private network information. Which type of firewall service is John thinking of implementing?
Which of the following attack signature analysis techniques are implemented to examine the header information and conclude that a packet has been altered?
Which of the following VPN topologies establishes a persistent connection between an organization's main office and its branch offices using a third-party network or the Internet?
Assume that you are working as a network administrator in the head office of a bank. One day a bank employee informed you that she is unable to log in to her system. At the same time, you get a call from another network administrator informing you that there is a problem connecting to the main server. How will you prioritize these two incidents?
The SOC manager is reviewing logs in AlienVault USM to investigate an intrusion on the network. Which CND approach is being used?
Which VPN QoS model guarantees the traffic from one customer edge (CE) to another?
Heather has been tasked with setting up and implementing VPN tunnels to remote offices. She will most likely be implementing IPsec VPN tunnels to connect the offices. At what layer of the OSI model does an IPsec tunnel function on?
Which phase of vulnerability management deals with the actions taken for correcting the discovered vulnerability?
Which of the following router configuration modes to change the terminal settings temporarily, perform basic tests, and lists the system information?
Which of the following is a compatible network device that converts various communication protocols and are used to connect different network technologies?
Which of the following refers to the clues, artifacts, or evidence that indicate a potential intrusion or malicious activity in an organization’s infrastructure?
The agency Jacob works for stores and transmits vast amounts of sensitive government data that cannot be compromised. Jacob has implemented Encapsulating
Security Payload (ESP) to encrypt IP traffic. Jacob wants to encrypt the IP traffic by inserting the ESP header in the IP datagram before the transport layer protocol header. What mode of ESP does Jacob need to use to encrypt the IP traffic?
Identify the spread spectrum technique that multiplies the original data signal with a pseudo random noise spreading code.
A newly joined network administrator wants to assess the organization against possible risk. He notices the organization doesn't have a __________ identified which helps measure how risky an activity is.
A network designer needs to submit a proposal for a company, which has just published a web portal for its clients on the internet. Such a server needs to be isolated from the internal network, placing itself in a DMZ. Faced with this need, the designer will present a proposal for a firewall with three interfaces, one for the internet network, another for the DMZ server farm and another for the internal network. What kind of topology will the designer propose?