Loading provider exams...
Sign Up & unlock 100% of Exam Questions
No Strings Attached!
Updated
While troubleshooting a VoIP handset connection, a technician's laptop is able to successfully connect to network resources using the same port. The technician needs to identify the port on the switch. Which of the following should the technician use to determine the switch and port?
Which of the following steps of the troubleshooting methodology would most likely include checking through each level of the OSI model after the problem has been identified?
A network administrator needs to set up a file server to allow user access. The organization uses DHCP to assign IP addresses. Which of the following is the best solution for the administrator to set up?
Which of the following technologies are X.509 certificates most commonly associated with?
A network administrator wants to implement an authentication process for temporary access to an organization's network. Which of the following technologies would facilitate this process?
Want a break from the ads?
Become a Supporter and enjoy a completely ad-free experience, plus unlock Learn Mode, Exam Mode, AstroTutor AI, and more.
Which of the following should be used to obtain remote access to a network appliance that has failed to start up properly?
Which of the following attacks utilizes a network packet that contains multiple network tags?
A network administrator is configuring a new switch and wants to connect two ports to the core switch to ensure redundancy. Which of the following configurations would meet this requirement?
Which of the following ports is used for secure email?
A client wants to increase overall security after a recent breach. Which of the following would be best to implement? (Choose two.)
Which of the following is a cost-effective advantage of a split-tunnel VPN?
A network technician is troubleshooting a web application's poor performance. The office has two internet links that share the traffic load. Which of the following tools should the technician use to determine which link is being used for the web application?
Which of the following attacks can cause users who are attempting to access a company website to be directed to an entirely different website?
As part of an attack, a threat actor purposefully overflows the content-addressable memory (CAM) table on a switch. Which of the following types of attacks is this scenario an example of?
A company's office has publicly accessible meeting rooms equipped with network ports. A recent audit revealed that visitors were able to access the corporate network by plugging personal laptops into open network ports. Which of the following should the company implement to prevent this in the future?
A user notifies a network administrator about losing access to a remote file server. The network administrator is able to ping the server and verifies the current firewall rules do not block access to the network fileshare. Which of the following tools would help identify which ports are open on the remote file server?
Which of the following technologies is the best choice to listen for requests and distribute user traffic across web servers?
A user is unable to navigate to a website because the provided URL is not resolving to the correct IP address. Other users are able to navigate to the intended website without issue. Which of the following is most likely causing this issue?
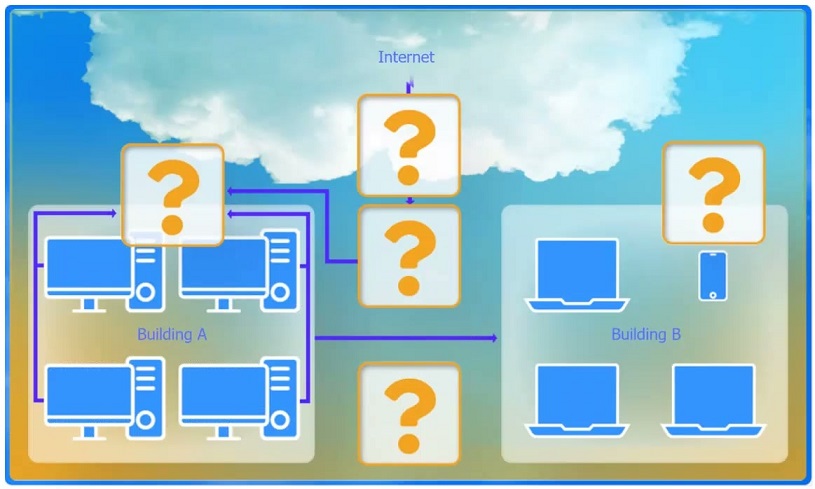
SIMULATION -
A network administrator has been tasked with configuring a network for a new corporate office. The office consists of two buildings, separated by 50 feet with no physical connectivity. The configuration must meet the following requirements:
Devices in both buildings should be able to access the Internet.
Security insists that all Internet traffic be inspected before entering the network.
Desktops should not see traffic destined for other devices.
INSTRUCTIONS -
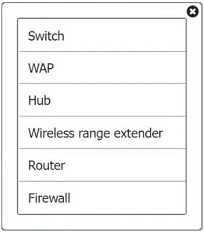
Select the appropriate network device for each location. If applicable, click on the magnifying glass next to any device which may require configuration updates and make any necessary changes.
Not all devices will be used, but all locations should be filled.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
A company is hosting a secure server that requires all connections to the server to be encrypted. A junior administrator needs to harden the web server. The following ports on the web server are open:
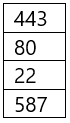
Which of the following ports should be disabled?
Which of the following is the next step to take after successfully testing a root cause theory?
A network administrator is configuring a new switch and wants to ensure that only assigned devices can connect to the switch. Which of the following should the administrator do?
A customer needs six usable IP addresses. Which of the following best meets this requirement?
Which of the following is created to illustrate the effectiveness of wireless networking coverage in a building?
Which of the following cloud deployment models is most commonly associated with multitenancy and is generally offered by a service provider?