Loading provider exams...
Sign Up & unlock 100% of Exam Questions
No Strings Attached!
Updated
A software engineer needs to transfer data over the internet using programmatic access while also being able to query the data. Which of the following will best help the engineer to complete this task?
A company’s content management system (CMS) service runs on an IaaS cluster on a public cloud. The CMS service is frequently targeted by a malicious threat actor using DDoS.
Which of the following should a cloud engineer monitor to identify attacks?
Which of the following is the most cost-effective way to store data that is infrequently accessed?
Which of the following vulnerability management concepts is best defined as the process of discovering vulnerabilities?
A company’s engineering department is conducting a month-long test on the scalability of an in-house-developed software that requires a cluster of 100 or more servers. Which of the following models is the best to use?
Want a break from the ads?
Become a Supporter and enjoy a completely ad-free experience, plus unlock Learn Mode, Exam Mode, AstroTutor AI, and more.
Once a change has been made to templates, which of the following commands should a cloud architect use next to deploy an IaaS platform?
A cloud networking engineer is troubleshooting the corporate office’s network configuration. Employees in the IT and operations departments are unable to resolve IP addresses on all devices, and the IT department cannot establish a connection to other departments’ subnets. The engineer identifies the following configuration currently in place to support the office network:
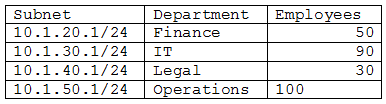
Each employee needs to connect to the network with a maximum of three hosts. Each subnet must be segregated, but the IT department must have the ability to communicate with all subnets. Which of the following meet the IP addressing and routing requirements? (Choose two.)
An organization’s critical data was exfiltrated from a computer system in a cyberattack. A cloud analyst wants to identify the root cause and is reviewing the following security logs of a software web application:
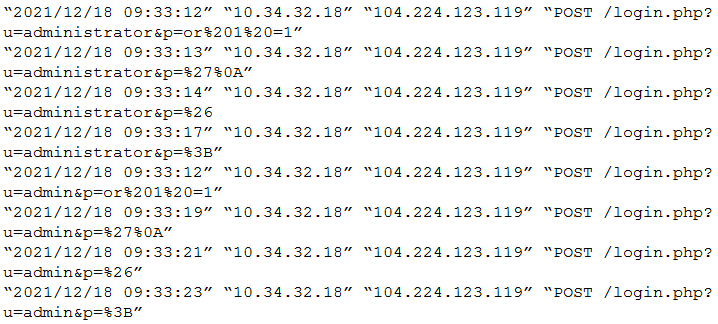
Which of the following types of attacks occurred?
Which of the following is a field of computer science that enables computers to identify and understand objects and people in images and videos?
A network administrator is building a site-to-site VPN tunnel from the company’s headquarters office to the company’s public cloud development network. The network administrator confirms the following:
The VPN tunnel is established on the headquarters office firewall.
While inside the office, developers report that they cannot connect to the development network resources.
While outside the office on a client VPN, developers report that they can connect to the development network resources.
The office and the client VPN have different IP subnet ranges.
The firewall flow logs show that traffic is reaching the development network from the office.
Which of the following is the next step the network administrator should take to troubleshoot the VPN tunnel?
A developer sends multiple requests to a SaaS application in a short amount of time. The developer realizes that the entire server and all other users can no longer send requests to the application. Which of the following best describes the issue?
A cross-site request forgery vulnerability exploited a web application that was hosted in a public IaaS network. A security engineer determined that deploying a WAF in blocking mode at a CDN would prevent the application from being exploited again. However, a week after implementing the WAF, the application was exploited again. Which of the following should the security engineer do to make the WAF control effective?
A new application that will be deployed to cloud VMs has the following requirements:
• Low inter-VM latency
• Horizontal scaling support
• 98.5% availability
• 8vCPU and 16GB
• Ability to split jobs across VMs
Which of the following will best meet these requirements?
Which of the following strategies requires the development of new code before an application can be successfully migrated to a cloud provider?
A company needs to deploy its own code directly in the cloud without provisioning additional infrastructure. Which of the following is the best cloud service model for the company to use?
Which of the following is a difference between a SAN and a NAS?
A cloud engineer is troubleshooting an application that consumes multiple third-party REST APIs. The application is randomly experiencing high latency. Which of the following would best help determine the source of the latency?
A group of cloud administrators frequently uses the same deployment template to recreate a cloud-based development environment. The administrators are unable to go back and review the history of changes they have made to the template. Which of the following cloud resource deployment concepts should the administrator start using?
A government agency in the public sector is considering a migration from on premises to the cloud. Which of the following are the most important considerations for this cloud migration? (Choose two.)
Which of the following migration types is best to use when migrating a highly available application, which is normally hosted on a local VM cluster, for usage with an external user population?
An engineer made a change to an application and needs to select a deployment strategy that meets the following requirements:
Is simple and fast -
Can be performed on two identical platforms
Which of the following strategies should the engineer use?
A developer is testing code that will be used to deploy a web farm in a public cloud. The main code block is a function to create a load balancer and a loop to create 1,000 web servers, as shown below:
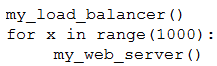
The developer runs the code against the company’s cloud account and observes that the load balancer is successfully created, but only 100 web servers have been created. Which of the following should the developer do to fix this issue?
Which of the following vulnerability management phases includes the process of discovering newly introduced security vulnerabilities?
A cloud engineer needs to integrate a new payment processor with an existing e-commerce website. Which of the following technologies is the best fit for this integration?
Five thousand employees always access the company’s public cloud-hosted web application on a daily basis during the same time frame. Some users have been reporting performance issues while attempting to connect to the web application. Which of the following is the best configuration approach to resolve this issue?