Loading provider exams...
Sign Up & unlock 100% of Exam Questions
No Strings Attached!
Updated
A security administrator is performing a gap assessment against a specific OS benchmark. The benchmark requires the following configurations be applied to endpoints:
• Full disk encryption
• Host-based firewall
• Time synchronization
• Password policies
• Application allow listing
• Zero Trust application access
Which of the following solutions best addresses the requirements? (Choose two.)
A financial technology firm works collaboratively with business partners in the industry to share threat intelligence within a central platform. This collaboration gives partner organizations the ability to obtain and share data associated with emerging threats from a variety of adversaries. Which of the following should the organization most likely leverage to facilitate this activity? (Choose two.)
A company plans to implement a research facility with intellectual property data that should be protected. The following is the security diagram proposed by the security architect:
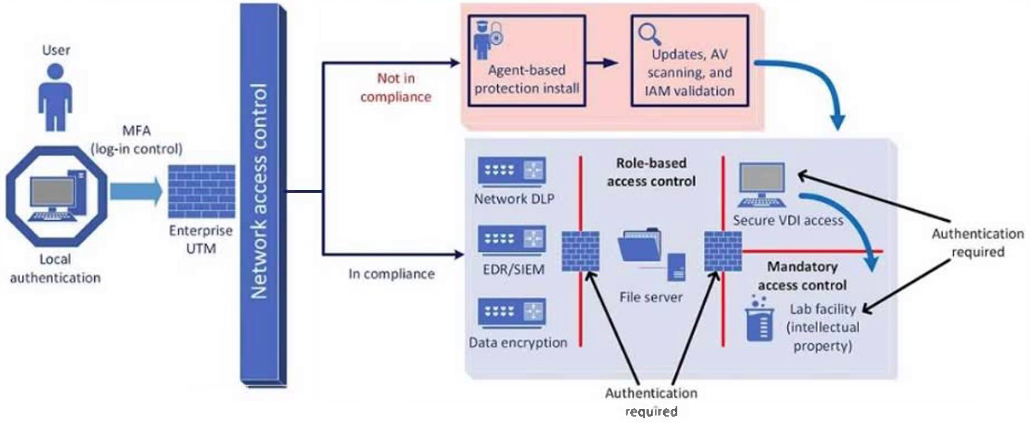
Which of the following security architect models is illustrated by the diagram?
During a gap assessment, an organization notes that BYOD usage is a significant risk. The organization implemented administrative policies prohibiting BYOD usage. However, the organization has not implemented technical controls to prevent the unauthorized use of BYOD assets when accessing the organization's resources. Which of the following solutions should the organization implement to best reduce the risk of BYOD devices? (Choose two.)
A systems administrator needs to address risks associated with corporate brand impersonation via email. The systems administrator wants a method that permits recipient servers to validate the source authenticity of emails received. Which of the following is the most appropriate?
Want a break from the ads?
Become a Supporter and enjoy a completely ad-free experience, plus unlock Learn Mode, Exam Mode, AstroTutor AI, and more.
A security analyst is reviewing the following log:
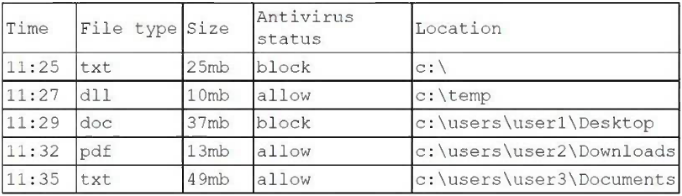
Which of the following possible events should the security analyst investigate further?
A global organization is reviewing potential vendors to outsource a critical payroll function. Each vendor's plan includes using local resources in multiple regions to ensure compliance with all regulations. The organization's Chief Information Security Officer is conducting a risk assessment on the potential outsourcing vendors' subprocessors. Which of the following best explains the need for this risk assessment?
A manufacturing plant is updating its IT services. During discussions, the senior management team created the following list of considerations:
• Staff turnover is high and seasonal.
• Extreme conditions often damage endpoints.
• Losses from downtime must be minimized.
• Regulatory data retention requirements exist.
Which of the following best addresses the considerations?
A company runs a DAST scan on a web application. The tool outputs the following recommendations:
• Use Cookie prefixes.
• Content Security Policy - SameSite=strict is not set.
Which of the following vulnerabilities has the tool identified?
After a company discovered a zero-day vulnerability in its VPN solution, the company plans to deploy cloud-hosted resources to replace its current on-premises systems. An engineer must find an appropriate solution to facilitate trusted connectivity. Which of the following capabilities is the most relevant?
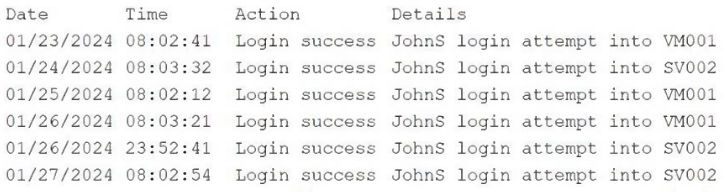
A security analyst wants to use lessons learned from a prior incident response to reduce dwell time in the future. The analyst is using the following data points:
Which of the following would the analyst most likely recommend?
An organization recently implemented a policy that requires all passwords to be rotated every 90 days. An administrator sees a large volume of failed sign-on logs from multiple servers that are often accessed by users. The administrator determines users are disconnecting from the RDP session but not logging off. Which of the following should the administrator do to prevent account lockouts?
SIMULATION -
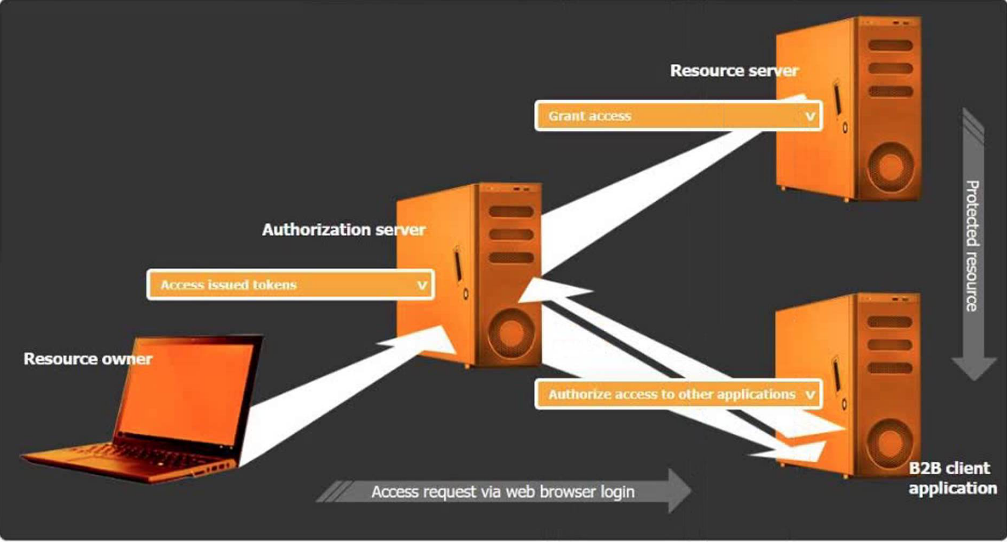
You are tasked with integrating a new B2B client application with an existing OAuth workflow that must meet the following requirements:
• The application does not need to know the users' credentials.
• An approval interaction between the users and the HTTP service must be orchestrated.
• The application must have limited access to users' data.
INSTRUCTIONS -
Use the drop-down menus to select the action items for the appropriate locations. All placeholders must be filled.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
A security analyst is reviewing the following code in the public repository for potential risk concerns:
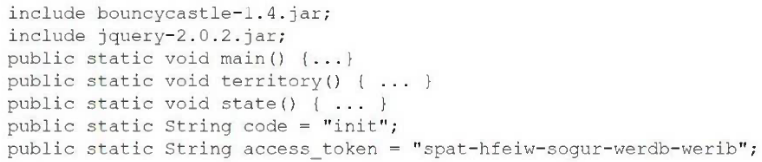
Which of the following should the security analyst recommend first to remediate the vulnerability?
The material findings from a recent compliance audit indicate a company has an issue with excessive permissions. The findings show that employees changing roles or departments results in privilege creep. Which of the following solutions are the best ways to mitigate this issue? (Choose two.)
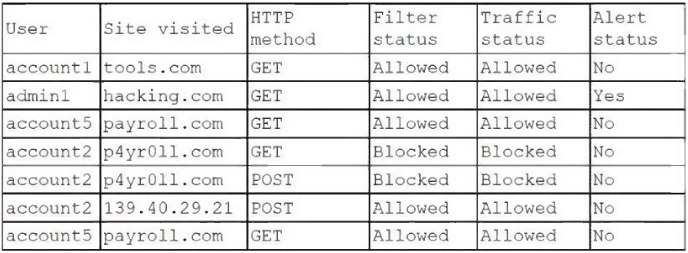
During a recent assessment, a security analyst observed the following:
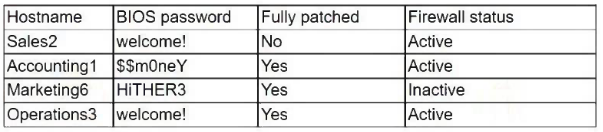
Which of the following should the analyst use to address the vulnerabilities in the future?
During a recent audit, a company's systems were assessed. Given the following information:
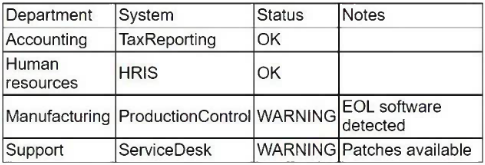
Which of the following is the best way to reduce the attack surface?
A company implemented a new NAC solution based on 802.1X. However, the IT support team notices that some devices are not being enrolled in the new policies, causing access disruptions for key users. Which of the following solutions will most likely solve this issue and prevent reoccurrence?
The security team is receiving escalated support tickets stating that one of the company's publicly available websites is not loading as expected. Given the following observations:

Which of the following is most likely the root cause?
An organization's load balancers have reached EOL and are scheduled to be replaced. The organization identified a new, critical vulnerability that affects an unused function of the load balancers. Which of the following are the best ways to address the risk to the organization? (Choose two.)
After an increase in adversarial activity, a company wants to implement security measures to mitigate the risk of a threat actor using compromised accounts to mask unauthorized activity. Which of the following is the best way to mitigate the issue?
A security engineer receives an alert from the SIEM platform indicating a possible malicious action on the internal network. The engineer generates a report that outputs the logs associated with the incident:
Which of the following actions best enables the engineer to investigate further?
Which of the following best describes the advantage of homomorphic encryption when compared to other encryption methodologies?
A compliance officer is reviewing the data sovereignty laws in several countries where the organization has no presence. Which of the following is the most likely reason for reviewing these laws?
An organization receives OSINT reports about an increase in ransomware targeting fileshares at peer companies. The organization wants to deploy hardening policies to its servers and workstations in order to contain potential ransomware. Which of the following should an engineer do to best achieve this goal?