Loading questions...
Updated
Want a break from the ads?
Become a Supporter and enjoy a completely ad-free experience, plus unlock Learn Mode, Exam Mode, AstroTutor AI, and more.
A server administrator needs to ensure all Window-based servers within a data center have RDP disabled. There are thousands of servers performing various roles. Which of the following is the BEST way to meet this requirement?
A very old PC is running a critical, proprietary application in MS-DOS. Administrators are concerned about the stability of this computer. Installation media has been lost, and the vendor is out of business.
Which of the following would be the BEST course of action to preserve business continuity?
An administrator needs to increase the size of an existing RAID 6 array that is running out of available space. Which of the following is the BEST way the administrator can perform this task?
An administrator notices high traffic on a certain subnet and would like to identify the source of the traffic. Which of the following tools should the administrator utilize?
In which of the following media rotation schemes are daily, weekly, and monthly backup media utilized in a first-in, first-out method?
Which of the following encryption methodologies would MOST likely be used to ensure encrypted data cannot be retrieved if a device is stolen?
Users in an office lost access to a file server following a short power outage. The server administrator noticed the server was powered off. Which of the following should the administrator do to prevent this situation in the future?
A server administrator is trying to determine the cause of a slowdown on a database server. Upon investigation, the administrator determines the issue is in the storage subsystem.
Which of the following will MOST likely resolve this issue?
Which of the following should a technician verify FIRST before decommissioning and wiping a file server?
While running a local network security scan, an administrator discovers communication between clients and one of the web servers is happening in cleartext. Company policy requires all communication to be encrypted. Which of the following ports should be closed to stop the cleartext communication?
A systems administrator is attempting to install a package on a server. After downloading the package from the internet and trying to launch it, the installation is blocked by the antivirus on the server. Which of the following must be completed before launching the installation package again?
The management team has mandated the use of data-at-rest encryption on all corporate servers. Using this encryption paradigm will ensure:
A technician needs to restore data from a backup. The technician has these files in the backup inventory:
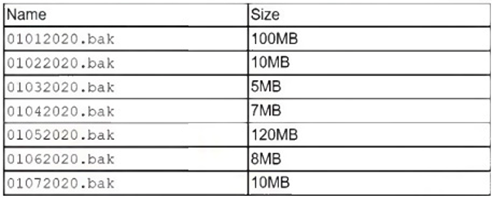
Which of the following backup types is being used if the file 01062020.bak requires another file to restore data?
Which of the following licensing models was created by software companies in response to the increasing density of processors?
Which of the following describes a configuration in which both nodes of a redundant system respond to service requests whenever possible?
A server administrator is gathering business requirements to determine how frequently backups need to be performed on an application server. Which of the following is the administrator attempting to establish?
A server technician downloaded new firmware from the manufacturer’s website. The technician then attempted to install the firmware on the server, but the installation failed, stating the file is potentially corrupt.
Which of the following should the technician have checked prior to installing the firmware?
A security technician generated a public/private key pair on a server. The technician needs to copy the key pair to another server on a different subnet.
Which of the following is the MOST secure method to copy the keys?
A technician noted the RAID hard drives were functional while troubleshooting a motherboard failure. The technician installed a spare motherboard with similar specifications and used the original components.
Which of the following should the technician do to restore operations with minimal downtime?
An administrator is designing a server for use in a factory environment that contains many pieces of large electrical equipment. Which of the following would be the BEST type of cable for the administrator to use to minimize networking issues?
A junior administrator reported that the website used for anti-malware updates is not working. The senior administrator then discovered all requests to the anti-malware site are being redirected to a malicious site. Which of the following tools should the senior administrator check FIRST to identify the potential cause of the issue?
A technician is deploying a new workstation. The workstation uses DHCP and can ping other devices on the same VLAN, but it cannot access anything on a different VLAN. Which of the following steps should the technician perform NEXT?
The network's IDS is giving multiple alerts that unauthorized traffic from a critical application server is being sent to a known-bad public IP address.
One of the alerts contains the following information:
Exploit Alert -
Attempted User Privilege Gain -
2/2/07-3:09:09 10.1.200.32 --> 208.206.12.9:80
This server application is part of a cluster in which two other servers are also servicing clients. The server administrator has verified the other servers are not sending out traffic to that public IP address. The IP address subnet of the application servers is 10.1.200.0/26. Which of the following should the administrator perform to ensure only authorized traffic is being sent from the application server and downtime is minimized? (Choose two.)
Which of the following script types would MOST likely be used on a modern Windows server OS?
A server technician arrives at a data center to troubleshoot a physical server that is not responding to remote management software. The technician discovers the servers in the data center are not connected to a KVM switch, and their out-of-band management cards have not been configured. Which of the following should the technician do to access the server for troubleshooting purposes?