Loading provider exams...
Sign Up & unlock 100% of Exam Questions
No Strings Attached!
Updated
SIMULATION -
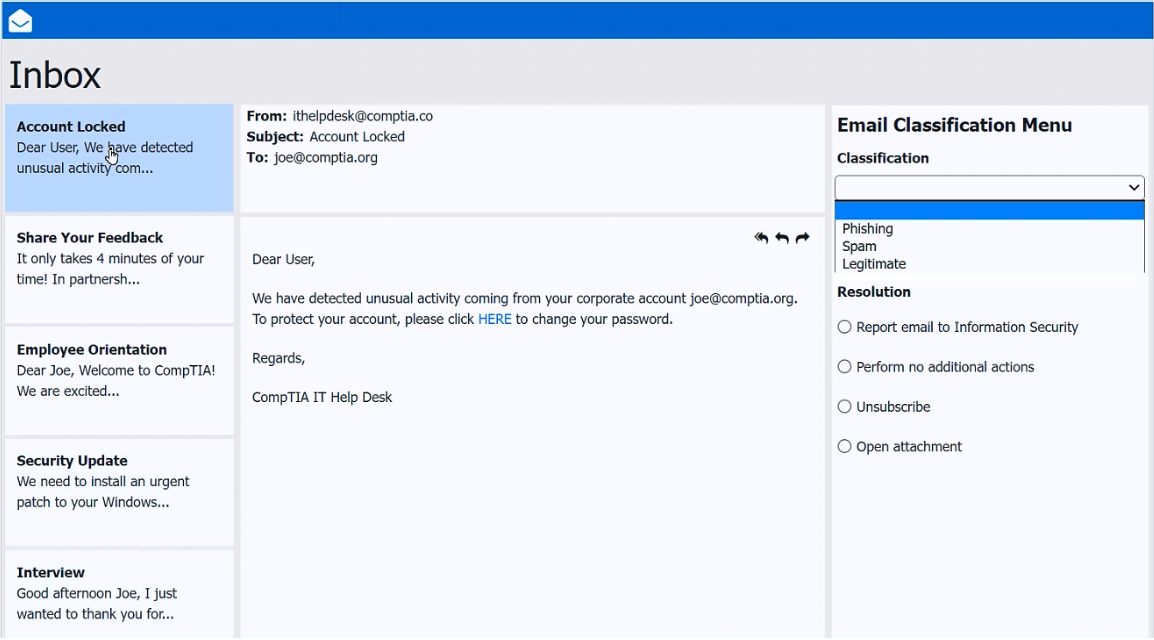
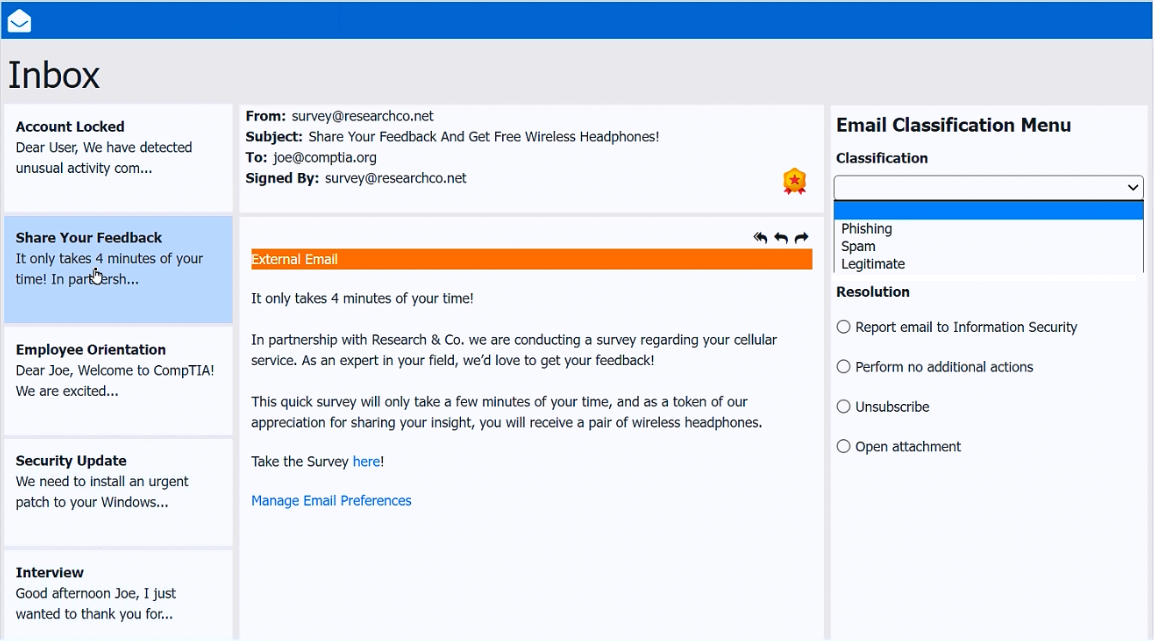
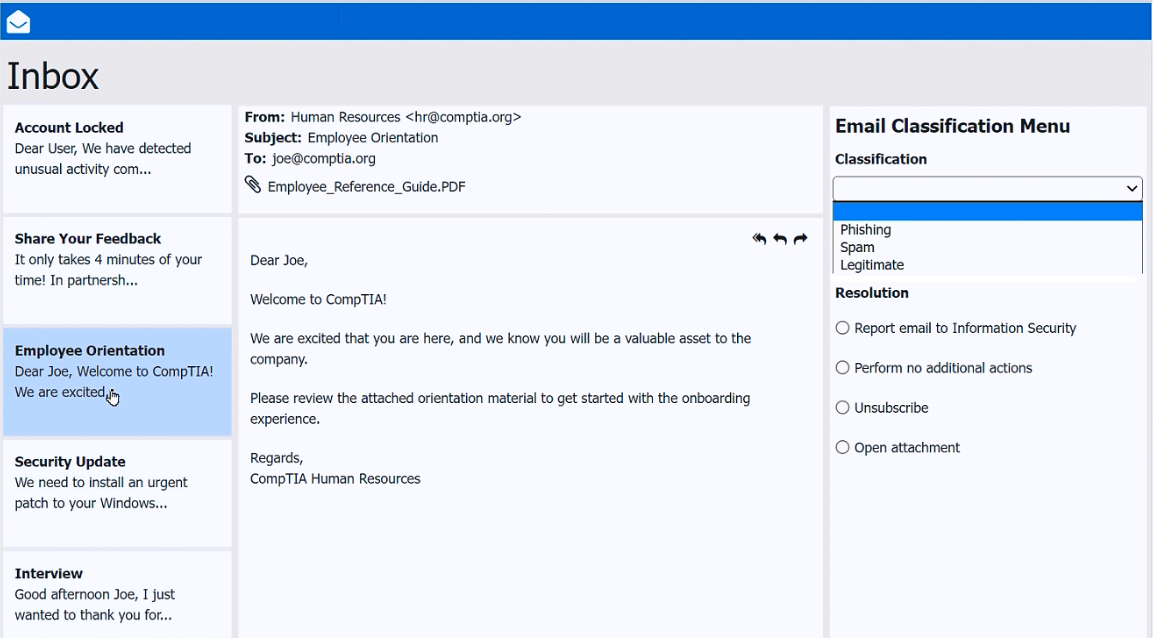
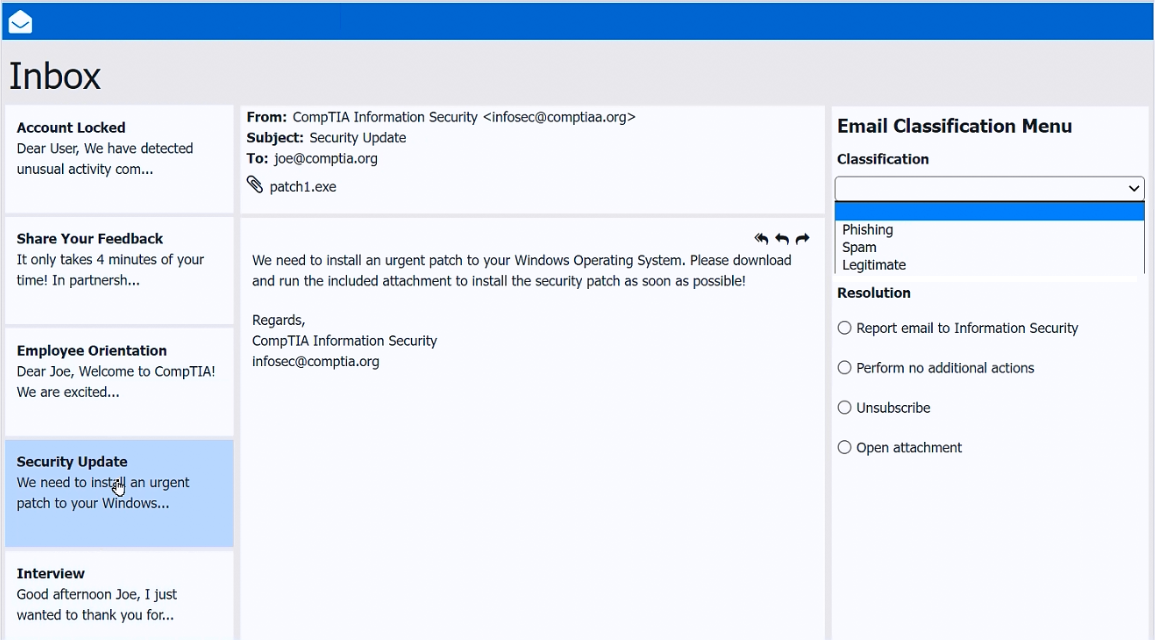
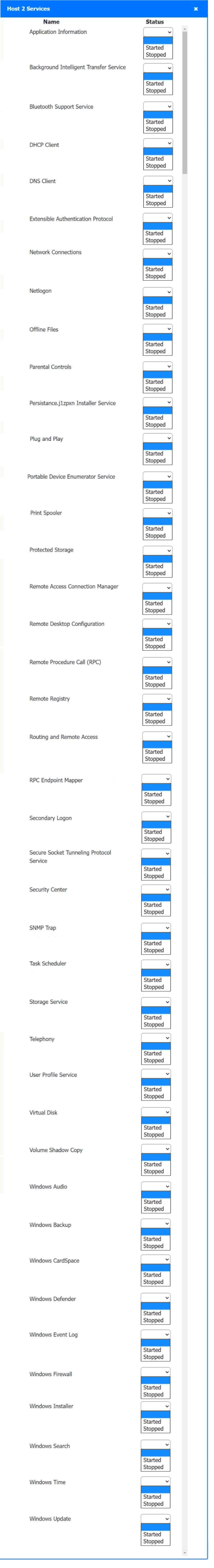
As a corporate technician, you are asked to evaluate several suspect email messages on a client's computer. Corporate policy requires the following:
All phishing attempts must be reported.
Future spam emails to users must be prevented.
INSTRUCTIONS -
Review each email and perform the following within the email:
Classify the emails -
Identify suspicious items, if applicable, in each email
Select the appropriate resolution
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
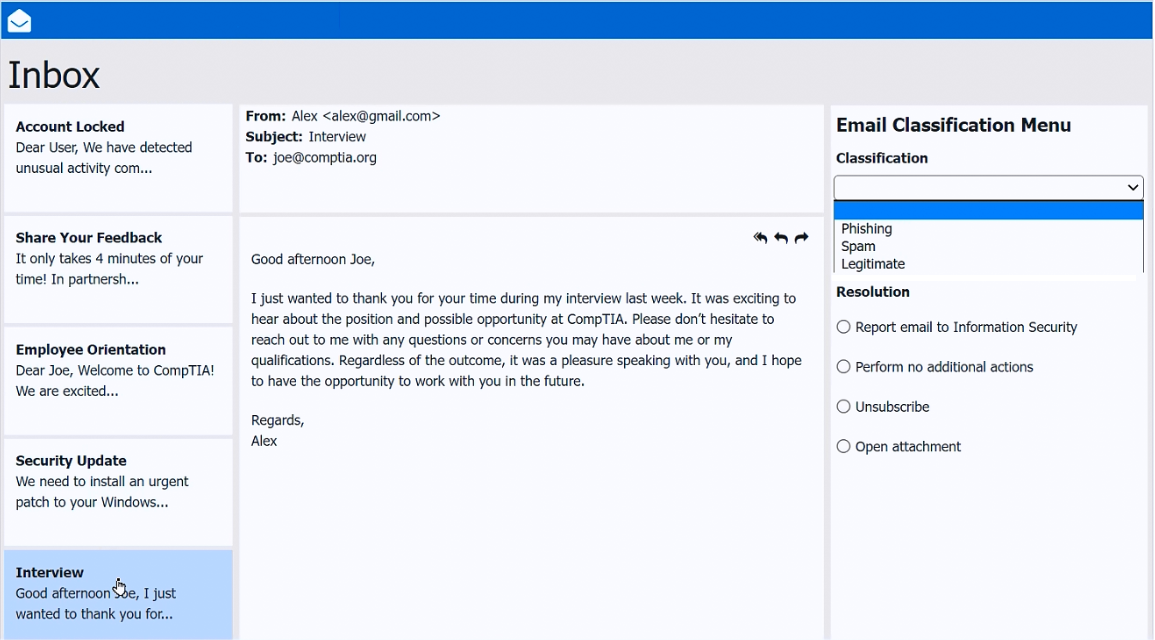
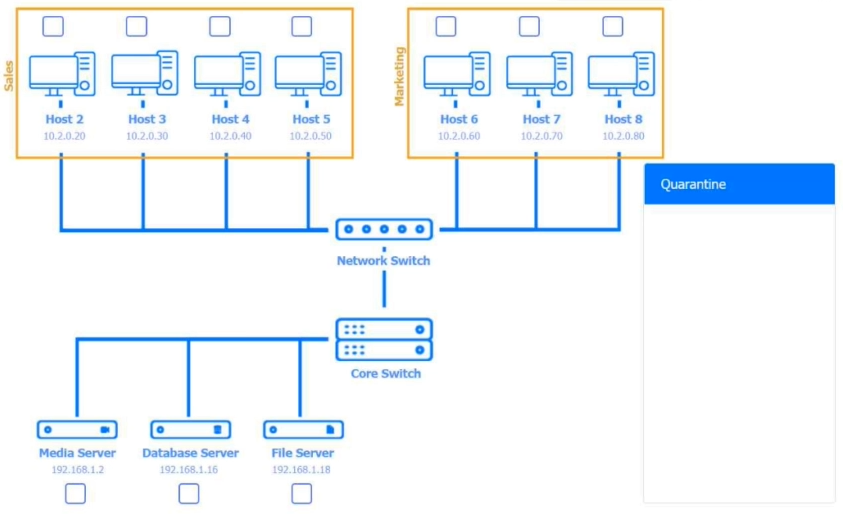
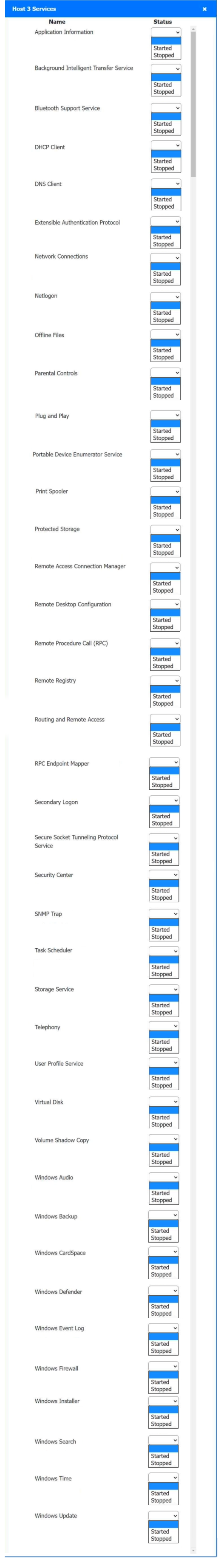
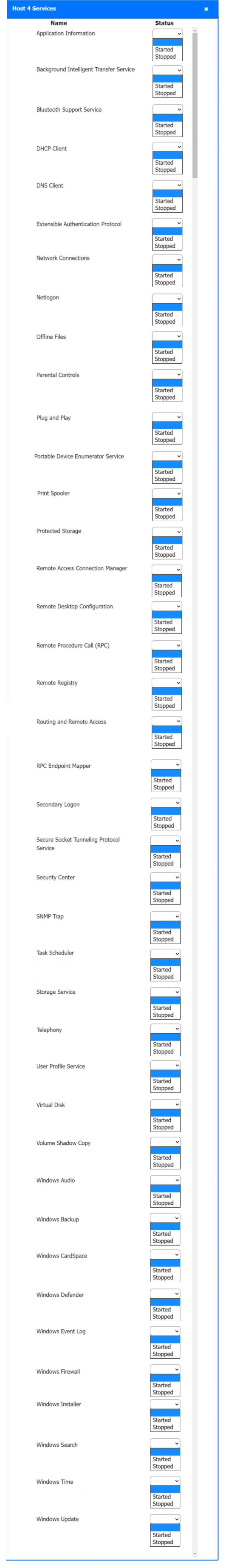
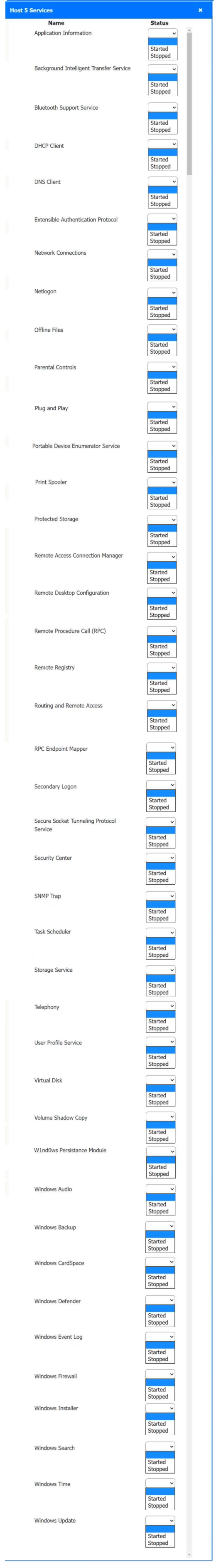
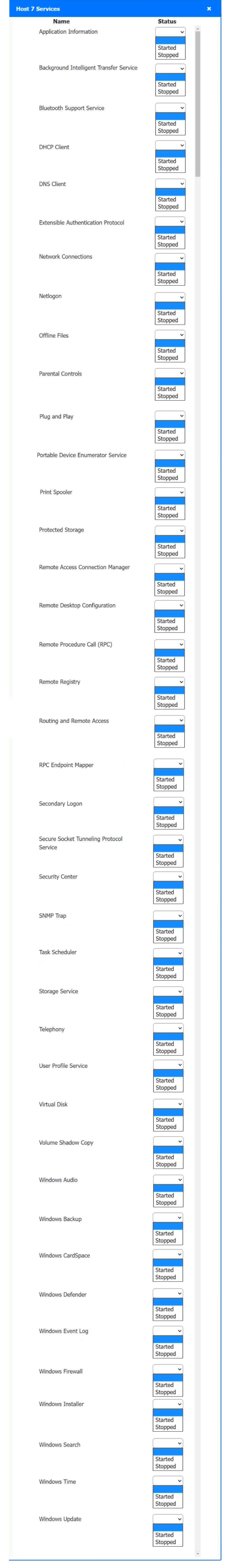
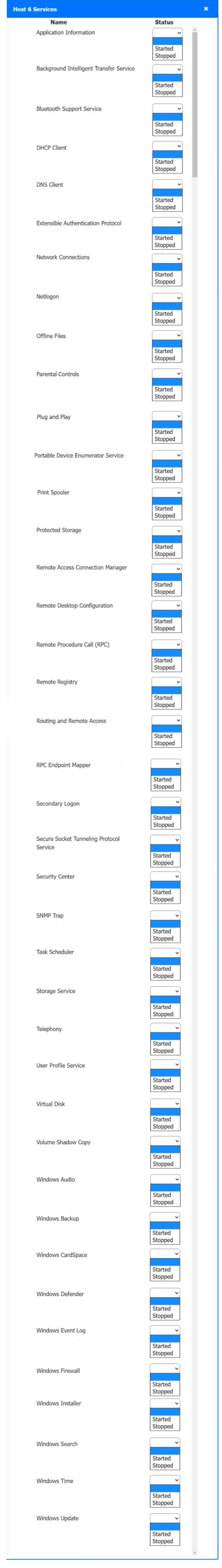
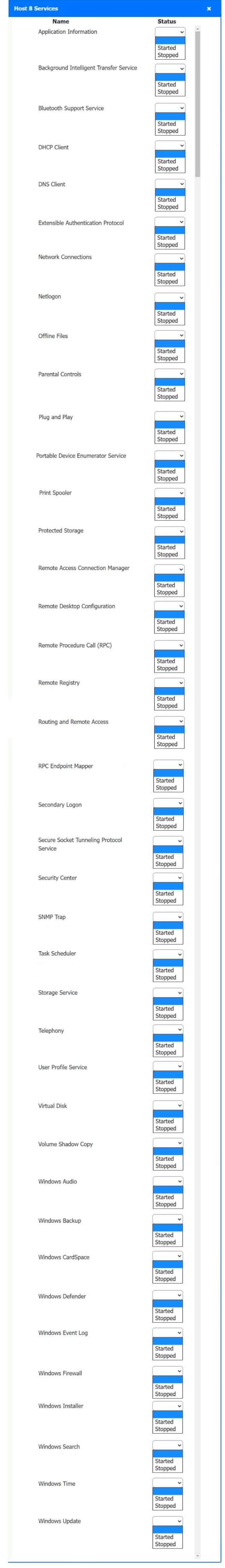
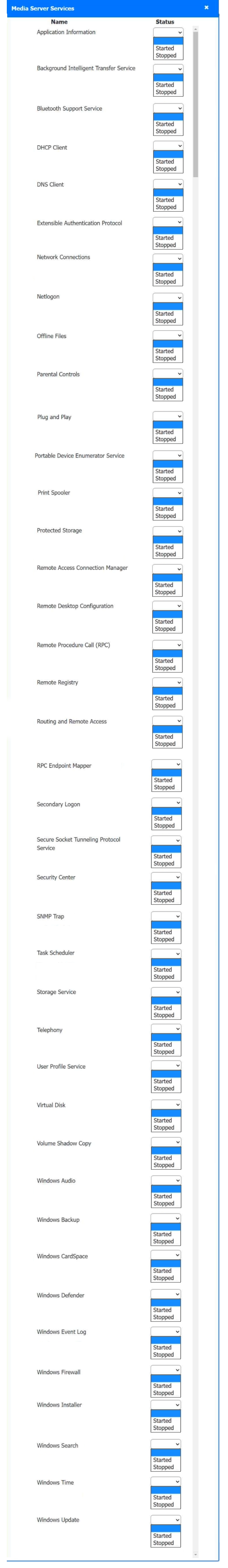
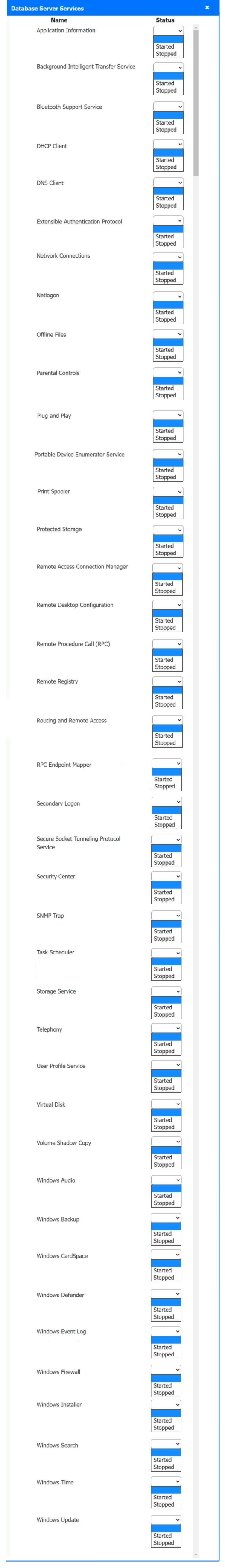
SIMULATION -
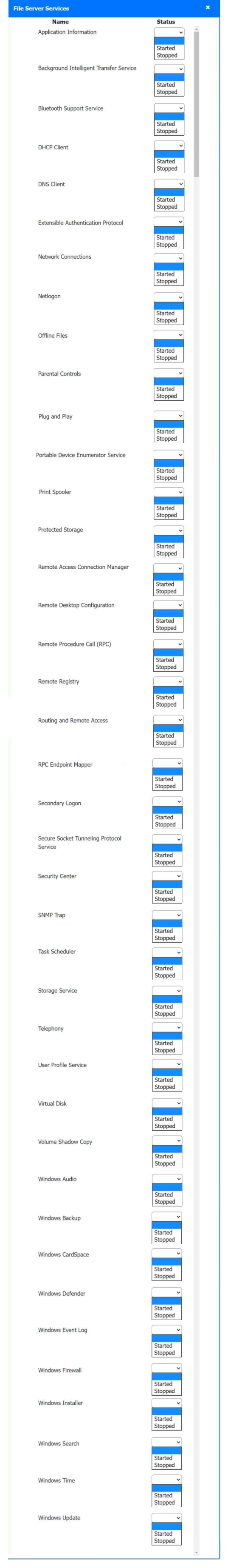
Multiple users are reporting audio issues as well as performance issues after downloading unauthorized software. You have been dispatched to identify and resolve any issues on the network using best practice procedures.
INSTRUCTIONS -
Quarantine and configure the appropriate device(s) so that the users’ audio issues are resolved using best practice procedures.
Multiple devices may be selected for quarantine.
Click on a host or server to configure services.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
MFA for a custom web application on a user's smartphone is no longer working. The last time the user remembered it working was before taking a vacation to another country. Which of the following should the technician do first?
The screen of a previously working computer repeatedly displays an OS Not Found error message when the computer is started. Only a USB drive, a keyboard, and a mouse are plugged into the computer. Which of the following should a technician do first?
A security administrator teaches all of an organization's staff members to use BitLocker To Go. Which of the following best describes the reason for this training?
Want a break from the ads?
Become a Supporter and enjoy a completely ad-free experience, plus unlock Learn Mode, Exam Mode, AstroTutor AI, and more.
An administrator received an email stating that the OS they are currently supporting will no longer be issued security updates and patches. Which of the following is most likely the reason the administrator received this message?
A user recently installed an application that accesses a database from a local server. When launching the application, it does not populate any information. Which of the following command-line tools is the best to troubleshoot the issue?
A user receives a new personal computer but is unable to run an application. An error displays saying that .NET Framework 3.5 is required and not found. Which of the following actions is the best way to resolve this issue?
A technician is deploying mobile devices and needs to prevent access to sensitive data if the devices are lost. Which of the following is the best way to prevent unauthorized access if the user is unaware that the phone is lost?
A technician is setting up a surveillance system for a customer. The customer wants access to the system's web interface on the LAN via the system’s IP address. Which of the following should the technician use to prevent external log-in attempts from the internet?
A user has been adding data to the same spreadsheet for several years. After adding a significant amount of data, they are now unable to open the file. Which of the following should a technician do to resolve the issue?
An application's performance is degrading over time. The application is slowing, but it never gives an error and does not crash. Which of the following tools should a technician use to start troubleshooting?
Which of the following is the best way to distribute custom images to 800 devices that include four device vendor classes with two types of user groups?
A network technician notices that most of the company's network switches are now end-of-life and need to be upgraded. Which of the following should the technician do first?
Which of the following is an example of an application publisher including undisclosed additional software in an installation package?
After a recent mobile OS upgrade to a smartphone, a user attempts to access their corporate email, but the application does not open. A technician restarts the smartphone, but the issue persists. Which of the following is the most likely way to resolve the issue?
A technician is attempting to join a workstation to a domain but is receiving an error message stating the domain cannot be found. However, the technician is able to ping the server and access the internet. Given the following information:
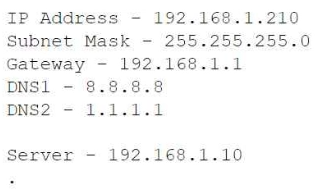
Which of the following should the technician do to fix the issue?
Which of the following filesystem types does the Linux OS use?
A user is working from home and is unable to access work files on a company laptop. Which of the following should a technician configure to fix the network access issue?
A user reports some single sign-on errors to a help desk technician. Currently, the user is able to sign in to the company's application portal but cannot access a specific SaaS-based tool. Which of the following would the technician most likely suggest as a next step?
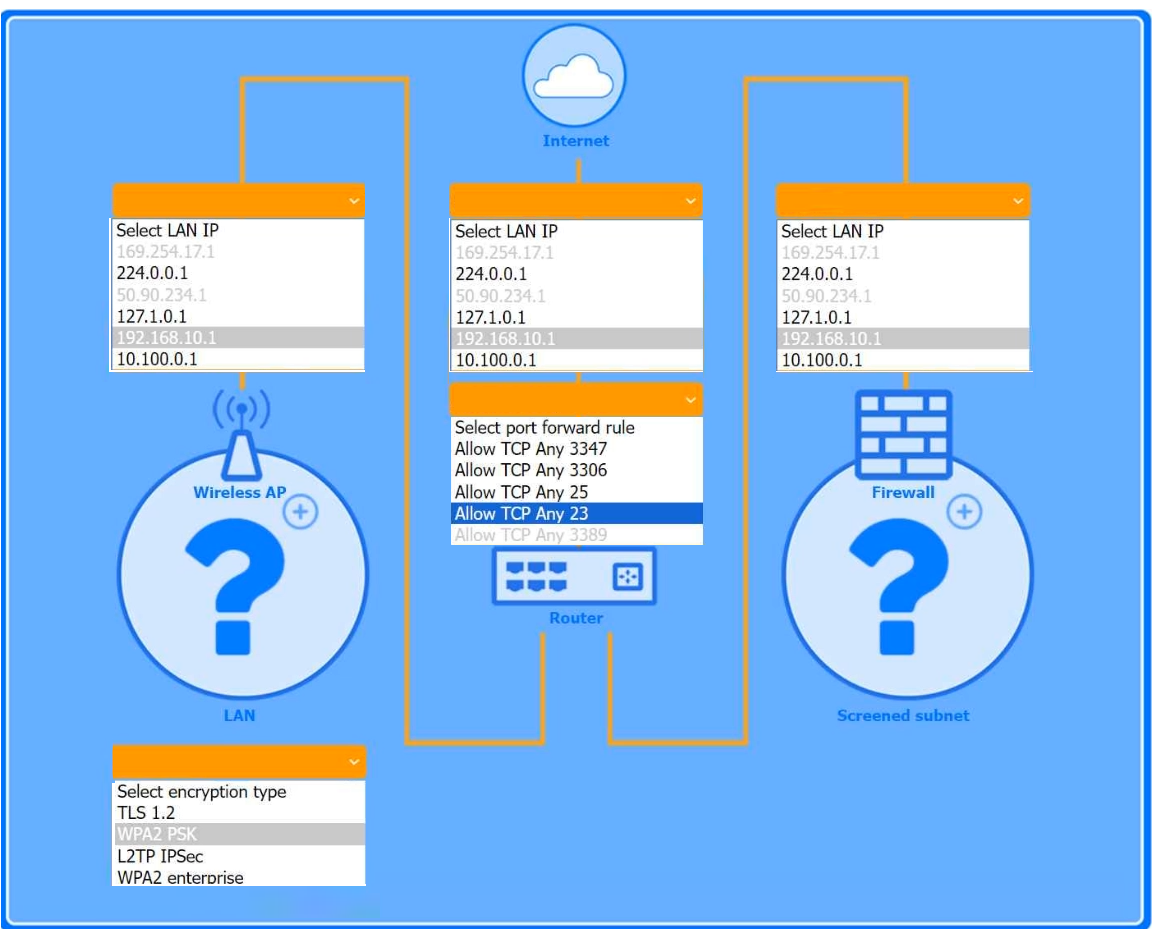
SIMULATION -
You are configuring a home network for a customer. The customer has requested the ability to access a Windows PC remotely, and needs all chat and optional functions to work in their game console.
INSTRUCTIONS -
Use the drop-down menus to complete the network configuration for the customer. Each option may only be used once, and not all options will be used.
Then, click the + sign to place each device in its appropriate location.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
Wireless AP LAN -
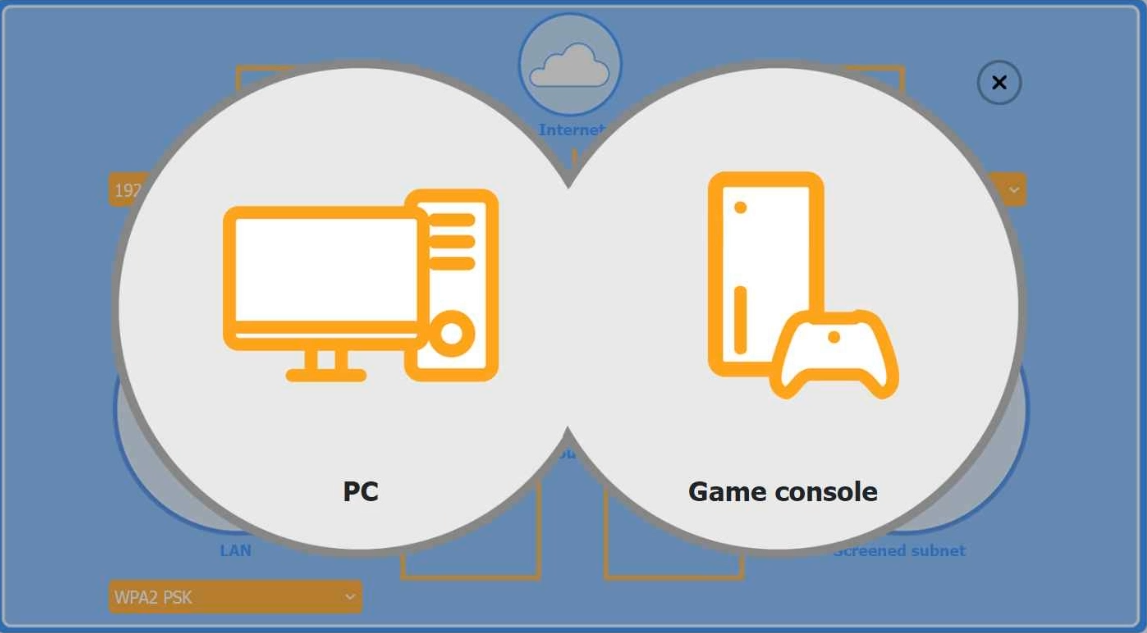
Firewall Screened Subnet -
Which of the following is used to detect and record access to restricted areas?
Users are reporting that an unsecured network is broadcasting with the same name as the normal wireless network. They are able to access the internet but cannot connect to the file share servers. Which of the following best describes this issue?
A small office reported a phishing attack that resulted in a malware infection. A technician is investigating the incident and has verified the following:
All endpoints are updated and have the newest EDR signatures.
Logs confirm that the malware was quarantined by EDR on one system.
The potentially infected machine was reimaged.
Which of the following actions should the technician take next?
Which of the following is the quickest way to move from Windows 10 to Windows 11 without losing data?