Loading provider exams...
Sign Up & unlock 100% of Exam Questions
No Strings Attached!
Updated
An IT company experienced the spread of malicious content between user endpoints, which impacted business critical resources. The company wants to implement a solution to control communication between individual endpoints on the network. Which approach achieves the goal?
A video game company identified a potential threat of a SYN flood attack, which could disrupt the online gaming services and impact user experience. The attack can overwhelm network resources by exploiting the TCP handshake process, leading to server unavailability and degraded performance. To safeguard the company's infrastructure and ensure uninterrupted service, it is essential to enhance the security measures in place. The company must implement a solution that manages and mitigates the risk of such network-based attacks. Which security product must be implemented to mitigate similar risks?
A developer company recently made a contract with new customer in the financial space. The customer has multiple remote sites and requires a VPN solution with the highest encryption. Which protocol must be used in IPsec Phase 2?
A logistics company wants to deploy an application in the cloud using cloud native techniques. The company must ensure that the development, testing, and production environments are as identical as possible with the lowest risk of the development and testing environments impacting production. Which solution must be used to accomplish the task?
An engineering company’s Chief Financial Officer recently fall victim to a phishing scam by responding to an urgent email. The mail appeared to be from a trusted business partner, and it requested sensitive tax information. The incident led to significant financial and reputational damage. To prevent similar occurrences in the future, the security team must implement an effective mitigation strategy. Which mitigation strategy must the security team implement to prevent similar occurrences in the future?
Want a break from the ads?
Become a Supporter and enjoy a completely ad-free experience, plus unlock Learn Mode, Exam Mode, AstroTutor AI, and more.
What is a use for AI in securing network infrastructure?
Which generative AI impact is addressed by a human-in-the-loop design policy?
How is generative AI used in securing network?
Which tool is used by SOC analyst to quarantine an endpoint?
Which benefit does AI provide in network security?
Which design policy addresses harmful content creation by generative AI?
Which tool must be used to prioritize incidents by a SOC?
Which tool is used to collect, analyze, and visualize logs from network devices, endpoints, and other sources in an enterprise?
In preparation for an upcoming security audit, a metal production company decided to enhance the security of container-based services running in a Kubernetes environment. The company wants to ensure that all communications between applications and services are encrypted. The administrator plans to implement mTLS service between application and services to secure the data exchanges. Given the need to manage encryption at scale and maintain efficient communication across the cluster, which network transport technology must be employed?
After a recent security breach, a financial company is reassessing their overall security posture and strategy to better protect sensitive data and resources. The company already\ deployed on-premises next-generation firewalls at the network edge for each branch location. Security measures must be enhanced at the endpoint level. The goal is to implement a solution that provides additional traffic filtering directly on endpoint devices, thereby offering another layer of defense against potential threats. Which technology must be implemented to meet the requirement?
Considering recent cybersecurity threats, a company wants to improve the process for identifying, assessing, and managing risks with a comprehensive and holistic approach.
Which framework must be used to meet these requirements?
What does watermarking AI generated content prevent?
A manufacturing company experienced a security breach that resulted in sales data being compromised. An engineer participating in the investigation must identify who logged into the sales system during the affected period. Which approach must be used to gather the information?
An employee of a pharmaceutical company accidentally checked in code that contains AWS secret keys to a public GitHub repository, which exposes production resources to attackers. Which mitigation strategy must a security engineer recommend to prevent future reoccurrence?
A security engineer on an application design team must choose a framework of attack patterns to evaluate during threat modeling. Which framework provides the common set of attacks?
A company recently discovered that a former employee, who left to join a competitor, continued to access and exfiltrate sensitive data over several weeks after leaving. The breach highlighted vulnerabilities in the organization’s data security and access management practices. To prevent such incidents in the future, the organization must adopt measures that detect and restrict unauthorized data access and transfer. Which mitigation strategy must be implemented to address the issue?
A developer is building new API functions for a cloud-based application. Before writing the code, the developer wants to ensure that destructive actions, including deleting and updating data, are properly protected by access control identifying sensitive fields such as those that contain passwords or personally identifiable information. Which approach must be used to score the risks proactively?
A retail company is facing a series of cyberattacks targeting the web servers, which results in disruptions to the online services. Upon investigation, the security team identified that these attacks involved invalid HTTP request headers, which were used to exploit vulnerabilities in the web application. To safeguard the company websites against similar threats in the future, the security team must deploy a security solution specifically designed to detect and block such malicious web traffic. Which security product must be used to protect the websites from similar attacks?
A developer company recently implemented a testing environment based on Linux operating system. The company needs a technology solution that produces tracing and filtering capabilities in the Linux kernel. Which technology meets these requirements without modifying the kernel source code?
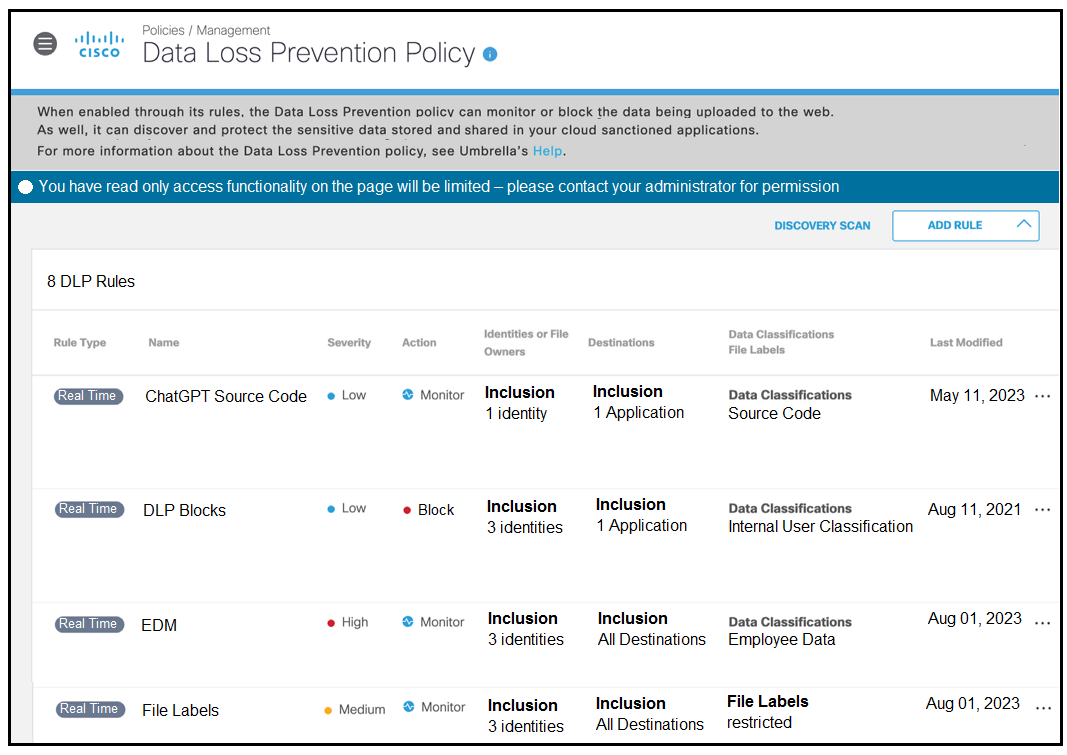
Refer to the exhibit. A software developer noticed that the application source code had been found on the internet. To avoid such an incident from happening again, the developer applied a DLP policy to prevent from uploading source code into generative AI tool like ChatGPT. When testing the policy, the developer noticed that it is still possible for the source code to be uploaded. Which action must the developer take to prevent this issue?