Loading provider exams...
Sign Up & unlock 100% of Exam Questions
No Strings Attached!
Updated
Which two log types does the Cisco WSA provide to troubleshoot Cisco data security and external data loss prevention policies? (Choose two.)
This exam has 60 community-verified practice questions. Create a free account to access all questions, comments, and explanations.
What is the primary benefit of using Cisco Advanced Web Security Reporting?
When an access policy is created, what is the default option for the Application Settings?
What is a benefit of integrating Cisco WSA with TrustSec in ISE?
What is a valid predefined time range when configuring a Web Tracking query?
Want a break from the ads?
Become a Supporter and enjoy a completely ad-free experience, plus unlock Learn Mode, Exam Mode, AstroTutor AI, and more.
Which two parameters are mandatory to control access to websites with proxy authentication on a Cisco WSA? (Choose two.)
Which two types of reports are scheduled on the Cisco WSA to analyze traffic? (Choose two.)
What must be configured first when creating an access policy that matches the Active Directory group?
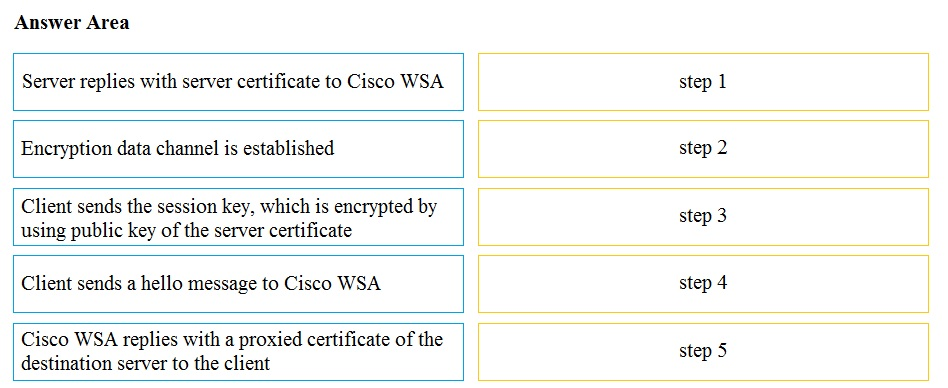
DRAG DROP -
Drag and drop the actions from the left into the correct order on the right in which they occur as an HTTPS session passes through the Cisco WSA.
Select and Place:
Which statement about configuring an identification profile for machine authentication is true?
Which two benefits does AMP provide compared to the other scanning engines on the Cisco WSA? (Choose two.)
Which response code in the access logs indicates that a transaction was blocked due to policy?
What is a benefit of integrating Cisco Cognitive Threat Analytics with a Cisco WSA?
An administrator wants to restrict file uploads to Facebook using the AVC feature.
Under which two actions must the administrator apply this restriction to an access policy? (Choose two.)
How does dynamic content analysis improve URL categorization?
What is needed to enable an HTTPS proxy?
What is the purpose of using AMP file analysis on a Cisco WSA to continuously evaluate emerging threats?
Which method is used by AMP against zero-day and targeted file-based attacks?
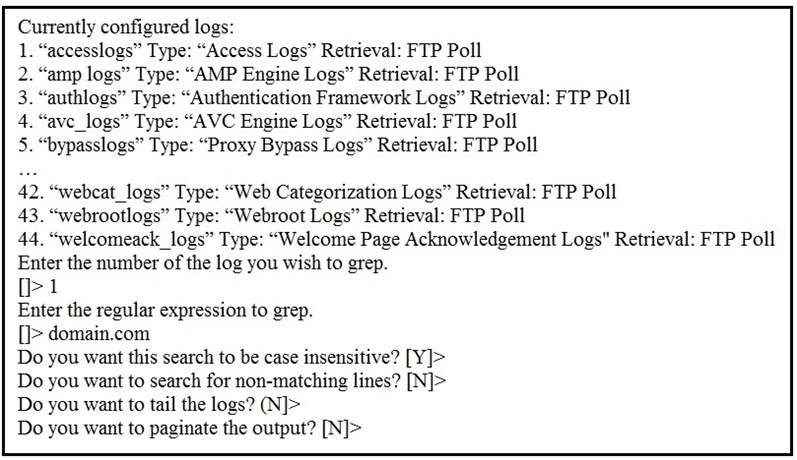
Refer to the exhibit. Which command displays this output?
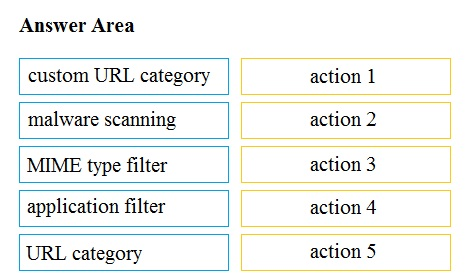
DRAG DROP -
Drag and drop the Cisco WSA access policy elements from the left into the order in which they are processed on the right.
Select and Place:
Which IP address and port are used by default to run the system setup wizard?
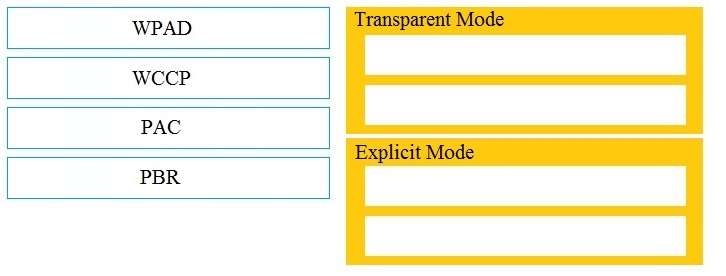
DRAG DROP -
Drag and drop the Cisco WSA methods from the left onto the correct deployment modes on the right.
Select and Place:
What causes authentication failures on a Cisco WSA when LDAP is used for authentication?
Which two features can be used with an upstream and downstream Cisco WSA web proxy to have the upstream WSA identify users by their client IP address?
(Choose two.)