Loading provider exams...
Sign Up & unlock 100% of Exam Questions
No Strings Attached!
Updated
A corporation hires a group of experienced cyber criminals to create a prolonged and in-depth presence on the network of a competitor. This presence will allow the corporation to steal or sabotage sensitive data from their competitor.
Which type of attack does this scenario describe?
This exam has 46 community-verified practice questions. Create a free account to access all questions, comments, and explanations.
Log In / Sign UpWhich three authentication factors are valid for use in a multifactor authentication scenario? (Choose three.)
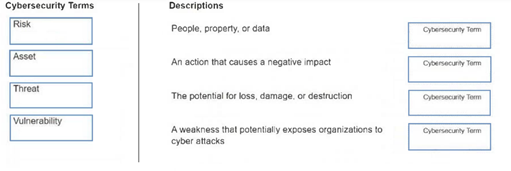
DRAG DROP -
Move each cybersecurity term from the list on the left to the correct description on the right.
Note: You will receive partial credit for each correct answer.
What does hashing provide for data communication?
The employees in the accounting department of a company receive an email about the latest federal accounting regulations. The email contains a hyperlink to register for a webinar that provides the latest updates on financial transaction security. The webinar is hosted by a government agency. As a security officer, you notice that the hyperlink points to an unknown party.
Which type of cybersecurity threat should you investigate?
Want a break from the ads?
Become a Supporter and enjoy a completely ad-free experience, plus unlock Learn Mode, Exam Mode, AstroTutor AI, and more.
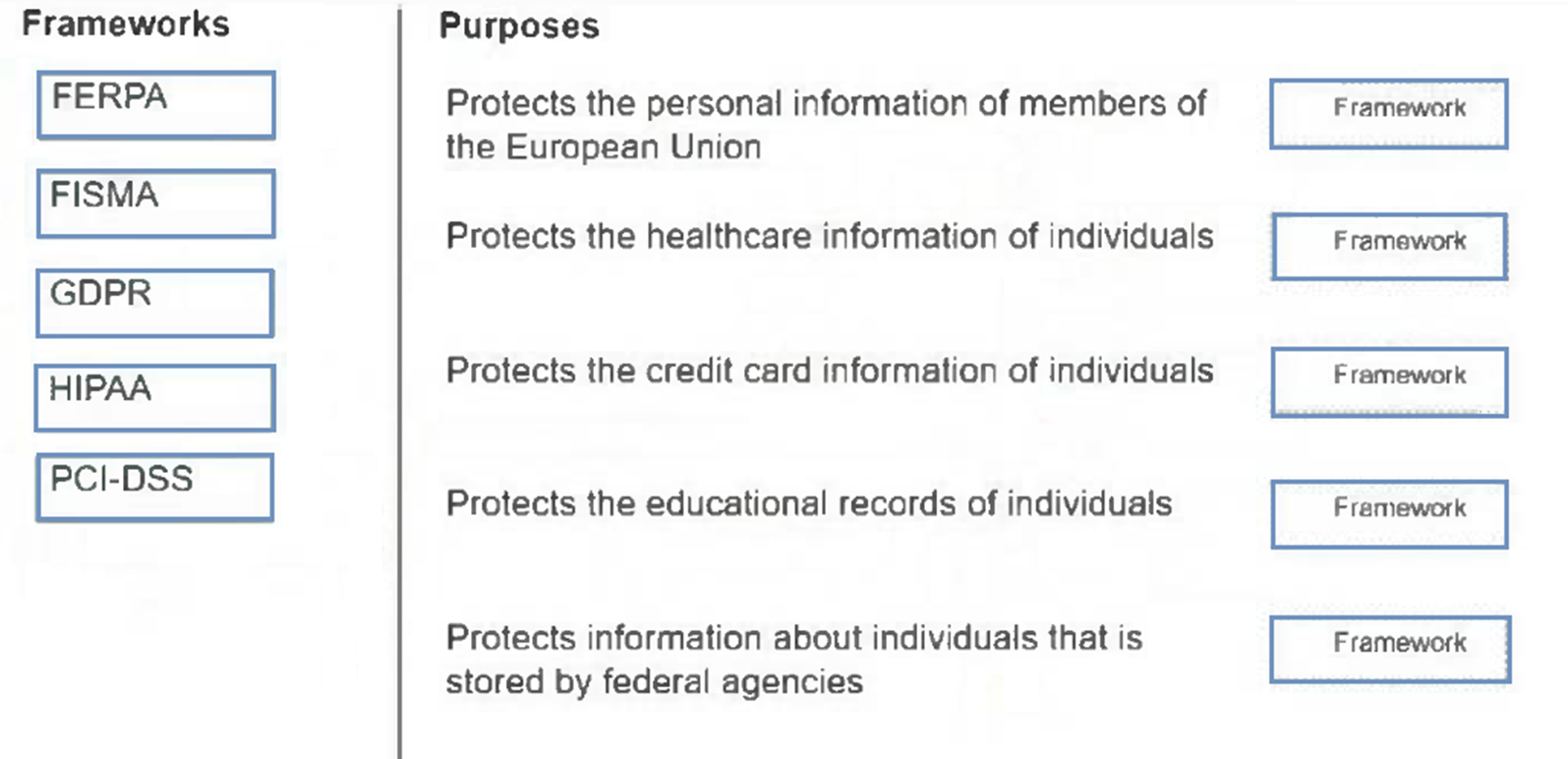
DRAG DROP -
Move each framework from the list on the left to the correct purpose on the right.
Note: You will receive partial credit for each correct answer.
In order to do online banking, you enter a strong password and then enter the 5-digit code sent to you on your smartphone.
Which type of authentication does this situation describe?
Which activity by an adversary is an example of an exploit that is attempting to gain user credentials?
Which wireless encryption technology requires AES to secure home wireless networks?
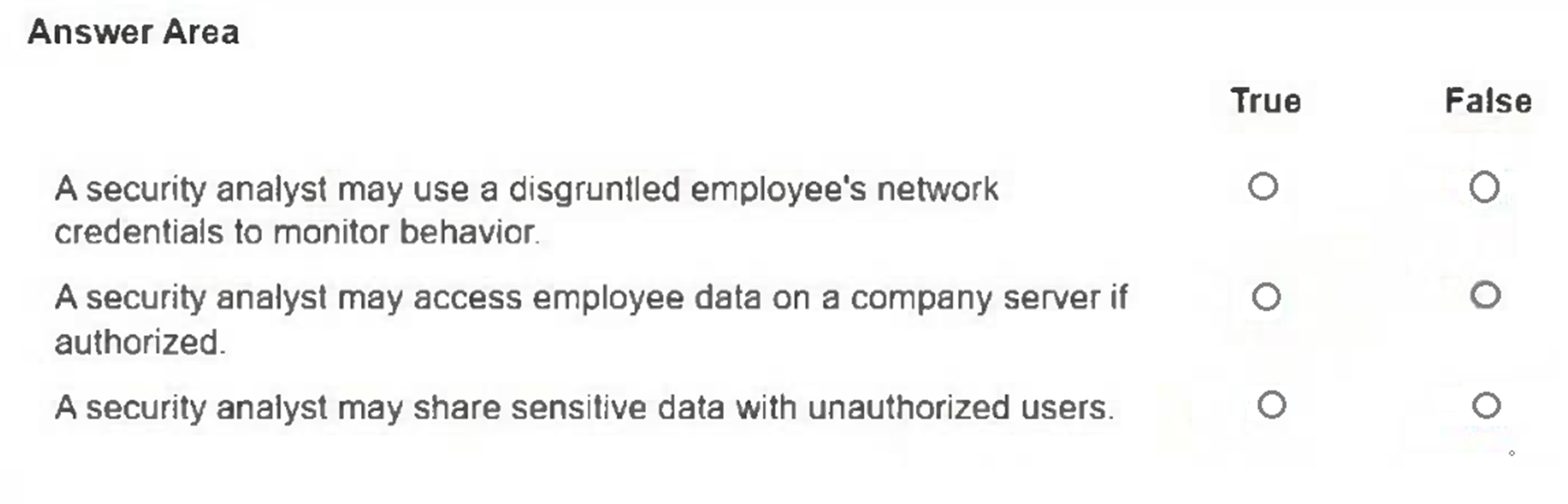
HOTSPOT -
For each statement, select True if the statement adheres to the cybersecurity code of ethics or False if it does not.
Note: You will receive partial credit for each correct selection.
You need to filter the websites that are available to employees on the company network.
Which type of device should you deploy?
Which two private IPv4 addresses would be blocked on the Internet to prevent security and performance issues? (Choose two.)
Note: You will receive partial credit for each correct selection.
You need to transfer configuration files to a router across an unsecured network.
Which protocol should you use to encrypt the files in transit?
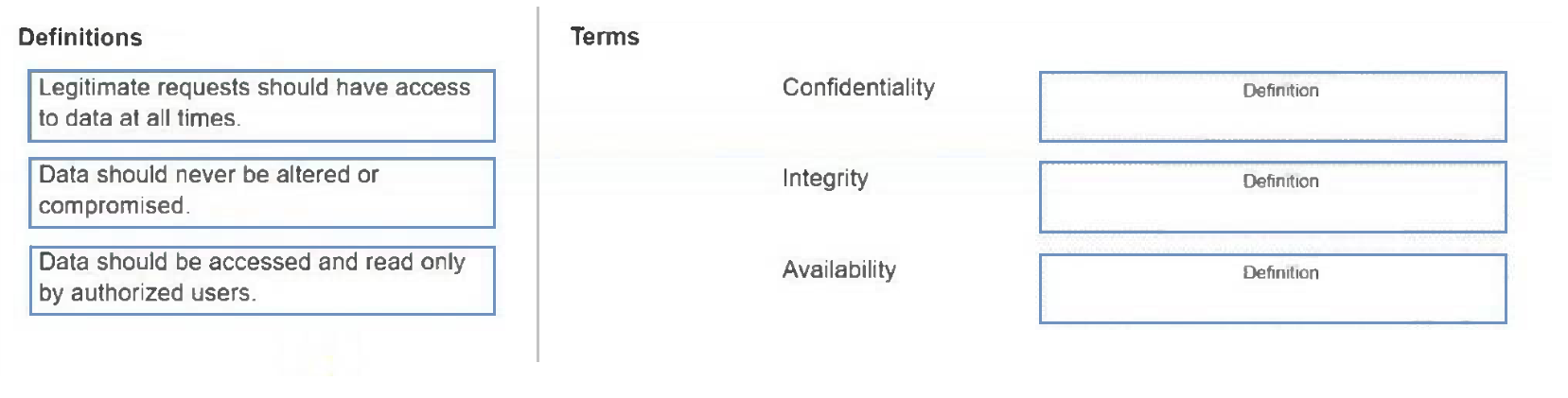
DRAG DROP -
Move each definition from the list on the left to the correct CIA Triad term on the right.
Note: You will receive partial credit for each correct answer.
Several employees complain that the company intranet site is no longer accepting their login information. You attempt to connect by using the URL and notice some misspellings on the site. When you connect by using the IP address, the site functions normally.
What should you do?
Customers of an online shopping store are complaining that they cannot visit the website. As an IT technician, you restart the website. After 30 minutes, the website crashes again. You suspect that the website has experienced a cyber attack.
Which type of cybersecurity threat should you investigate?
A system on your network is experiencing slower than usual response times. In order to gather information about the status of the system, you issue the netstat -1 command to display all of the TCP ports that are in the Listening state.
What does the Listening state indicate about these ports?
You are reviewing company remote access procedures and notice that telnet is being used to connect to the corporate database server to check on inventory levels.
Which two actions should you take immediately? (Choose two.)
Note: You will receive partial credit for each correct selection.
What should you create to prevent spoofing of the internal network?